Opportunities and challenges of open 5G RAN
Open RAN architectures promise open interfaces, advanced intelligence, and automation to enable cloud-based 5G RAN deployments with increased vendor diversity, interoperability, and deployment flexibility for communication service providers (CSPs).
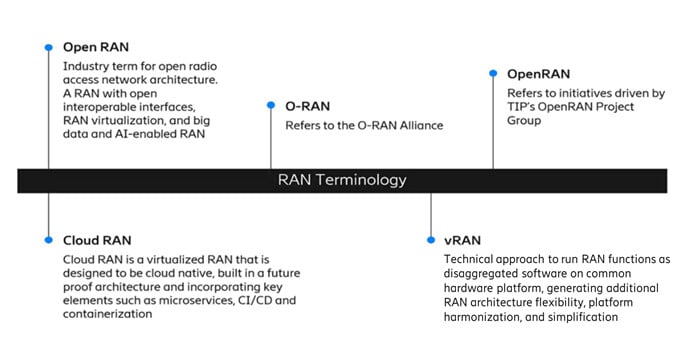
There are several active initiatives to achieve Open RAN, including 3GPP-based vRAN architecture, Cloud RAN, and O-RAN (as shown in Figure 1).
NOTE: O-RAN is specified by the O-RAN Alliance with additional functions and open interfaces built on 3GPP standards. O-RAN has additional security considerations due to its expanded attack surface that are currently being addressed in the O-RAN Alliance’s Security Focus Group (SFG
Securing 5G RAN deployments in the cloud
The primary security objectives of RAN implementations are to protect data, ensure performance, and guarantee availability. Cloud-based deployments can provide inherent security advantages such as isolation and geographical redundancy. They also introduce new internal and external security risks that must be considered.
Risks can be mitigated with the right combination of people, processes, and technology to ensure that RAN implementations, including Cloud RAN, are secure, trusted and robust. To address risks in the cloud there are existing practices that needs to applied and adapted for telco deployments, as described in the next section. RAN deployments in the cloud are not inherently more or less secure, and an assessment of security posture depends upon many factors, such as implementation, architecture, the supply chain, and use cases.
One thing to consider is that cloud-based deployments have a different threat surface compared to the traditional RAN, primarily due to the following:
- Decoupling of the software from the hardware
- Separation of software layers in the cloud-native stack
- Multiple tenants sharing the same hardware resources
- Third-party organizations managing the cloud infrastructure
- Open-source software components such as Docker and Kubernetes
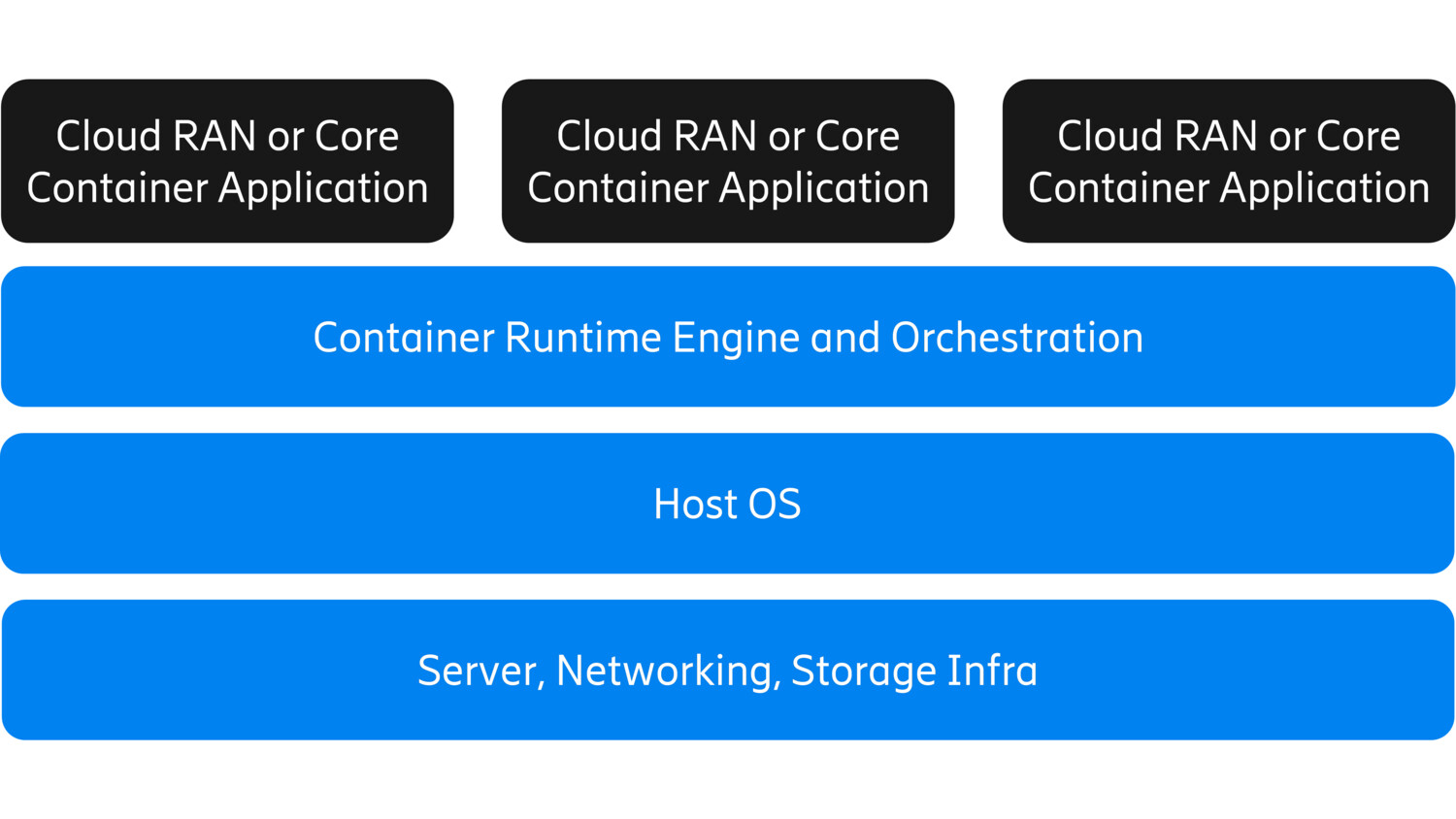
Vulnerabilities in the cloud infrastructure can be exploited in cloud-based deployments of RAN and Core. These vulnerabilities can exist at multiple layers, including container applications (microservices), container engines (a software that runs and manages the components required to run containers), host operating systems, and third-party hardware at the infrastructure layer (as shown in Figure 2).
Figure 2. Cloud-native stack for 5G deployments
An external attacker could, for example, compromise a container in one application then gain access to additional services and cloud infrastructure. Similarly, an attacker that gains access to a service can use it to gain access to other containers. Attack vectors such as supply-chain attacks, cross-container intrusions, weak authentication, and misconfiguration can be exploited by internal and external threat actors to compromise applications and breach data in transit, in use, and at rest for attacks on confidentiality, integrity, and availability. The availability of the cloud and cloud applications can be compromised by botnets, volumetric distributed denial-of-service, or DDoS, and application-DDoS attacks on the user plane from internal devices and external attackers.
Centralized deployments of Cloud RAN and Cloud Core may leverage a common cloud platform located in a data center, presenting common attack vectors for the RAN and Core, but with different impacts from breach or attack.
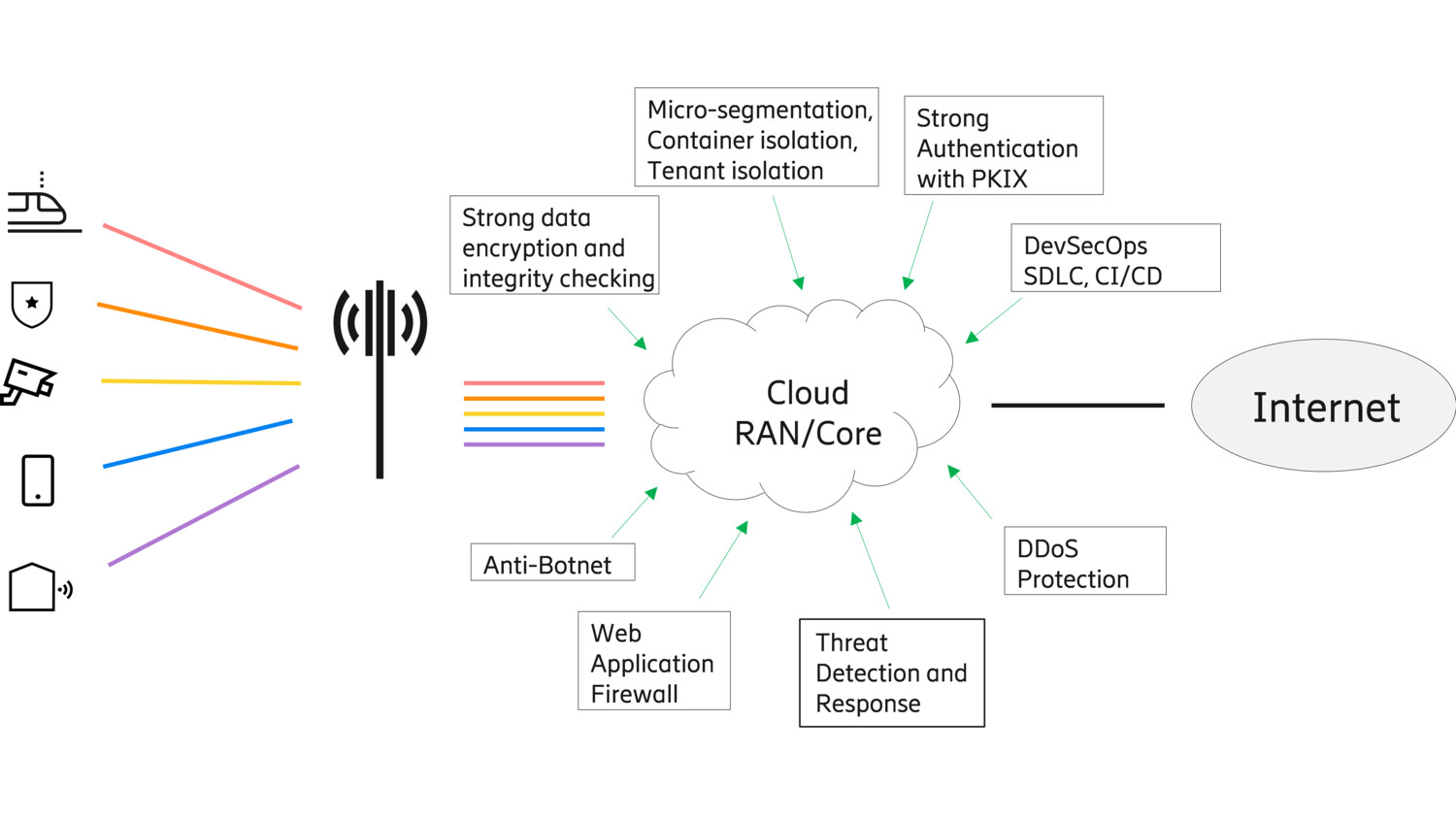
Practices of secure cloud 5G RAN
For a cloud-based open 5G RAN, a secure environment built on industry best practices is needed, including application of existing and evolving security best practices developed for the information technology (IT) domain. The trust stack in the environment includes trusted hardware, software, deployment, applications, and operations. A trust chain needs to be established with hardware root of trust based upon public key infrastructure, key protection, data protection and hardening of configurations according to best practices as described in the CIS benchmarks. Data needs to be protected while in-transit, at-rest, and potentially also in-use to ensure privacy of personal information and business-sensitive data.
A key security control in in a multi-tenant cloud is micro-segmentation, which provides isolation and mitigation for many of the attack vectors. Mission-critical and security-critical workloads should avoid sharing resources with workloads that have low criticality ratings. Isolation mechanisms include:
- Tenant isolation using dedicated host resources, such as memory, execution, storage, and networks, for each tenant in a multi-tenant environment.
- Physical isolation using physically separated hosts to prevent the compromise of one physical node allowing an attacker to move laterally across the virtualized network.
- Traffic separation using traffic filtering for inbound and outbound traffic.
- Secure configuration of the container runtime environment using software-based isolation mechanisms like namespaces, control groups, and file system protections to separate different workgroups from each other.
- 5G network slicing: Each slice can be architected to separate the enterprise’s control and user traffic while providing the opportunity for tailored security to match the use case. Slice-specific mutual authentication ensures that only authorized devices have access to the slice.
Another practice for securing a Cloud RAN is a zero-trust architecture, or ZTA. This is an important security model for cloud-based 5G network deployments because it is built on the principle that no user or network function can be inherently trusted, whether internal or external to the network. In a ZTA, as defined by NIST SP 800-207, there is no implicit trust granted to assets or users based on physical or network location, or ownership. This is relevant to cloud deployments which have multiple stakeholders: vendor, service provider, hyperscale cloud provider (HCP), and system integrator (SI).
A Cloud RAN designed for ZTA has the following security features:
- Hardware Root of Trust (HRoT) for the Commercial Off-The-Shelf (COTS) hardware with a Hardware Security Module (HSM).
- Strong digital identities with digital signing from a Certificate Authority (CA).
- Mutual authentication between device and network using 5G-AKA, EAP-AKA and EAP-TLS techniques for authentication.
- Mutual authentication using Transport Layer Security (TLS) or Datagram TLS (DTLS) with Public-Key Infrastructure and X.509 (PKIX) and strong cipher suites.
- Multi-factor authentication (MFA) for secure user access to CNFs and cloud infrastructure.
- Visibility, monitoring and logging for alerting and auditing.
The security posture of a cloud deployment also needs to be continuously managed as cloud-based networks are dynamic and threats are constantly evolving. Containers inherently provide software modularity and decomposition, which allow for independent LCM. However, lifecycle management, or LCM, will become more complex in a cloud environment and will require automated management and orchestration functions. The use of an automated security management solution for policy configuration, access controls, configuration validation, logging, and run-time compliance monitoring is recommended. Threat detection and response, or TDR, is a key function throughout the cloud-native stack, including hardware, operating system, runtime environment, and the application container.
Figure 3. Security controls for 5G Cloud RAN
Finally, with Open RAN deployments, the transfer of data ownership needs to be considered when a public cloud or a managed service provider is used. For the RAN operator, theft of sensitive or private data, may result in churn, fines, and loss of business due to compromised business reputation or regulatory violation. The service provider is responsible to ensure that data in-transit, at-rest and in-use are protected according to the requirements of the use case and industry best practices. The software vendor is responsible to apply LCM with security by design to their Cloud-Native Functions, or CNFs. The vendor, CSP, cloud provider, and system integrator must establish a multiparty relationship to agree upon clearly defined roles and responsibilities for implementing security controls to protect against internal and external threats. Changes to risk – due to evolving threats, attack vectors, and security control technologies – should be periodically assessed by all stakeholders.
In summary, Cloud RAN should be secured based upon the following principles:
- Embrace a zero-trust architecture including multi-factor authentication of users and automated mutual authentication with PKI-based certificates.
- Build a secure cloud environment including secure hardware, micro-segmentation, threat detection and response, and user plane protection.
- Use an automated security management solution for policy configuration, access controls, configuration validation, logging, and run-time compliance monitoring.
- Protect data-in-transit, data-at-rest, and data-in-use to ensure privacy of personal information and business-sensitive data.
- Software development organizations should apply LCM with security by design to their CNFs.
- Multi-party agreements are needed to clarify the responsibility of the vendor, service provider, cloud provider, and system integrator.
A trusted telecom security partner
Network security has been critical to Ericsson’s technology leadership throughout the company’s history. We understand that the battle against security threats is a constant and evolving one, and we are committed to our responsibility to provide secure and reliable products and solutions. The mitigations of security risks can be addressed with a combination of people, processes, and technology to ensure that RAN implementations, including Cloud RAN, are secure, trusted, and robust.
Ericsson follows industry best security practices and is a key contributor to 3GPP SA3 and O-RAN Alliance’s SFG. Ericsson’s Cloud RAN products are designed with zero trust in mind and built to be an integral part of a zero-trust architecture. Ericsson’s automated security management tools help operators maintain a secure Cloud RAN environment.
Security by design is embedded in the Ericsson generic design process in the holistic framework Security Reliability Model, or SRM, for Cloud RAN as well as for all other products. A security culture among the people at Ericsson is supported by our Security Master Model to ensure security competence across all teams – from design to deployment and support.
Ericsson is prepared for the security challenges of today and well positioned to evolve as the threat landscape changes.
For additional information, read our technical paper on Security considerations of Cloud RAN.