Trustworthy systems
Mobile networks are part of the critical infrastructure for society, industries, and consumers. On the journey towards the future, network capabilities will elevate to a level where the networks can fulfil the requirements of even the most mission and business critical use cases.
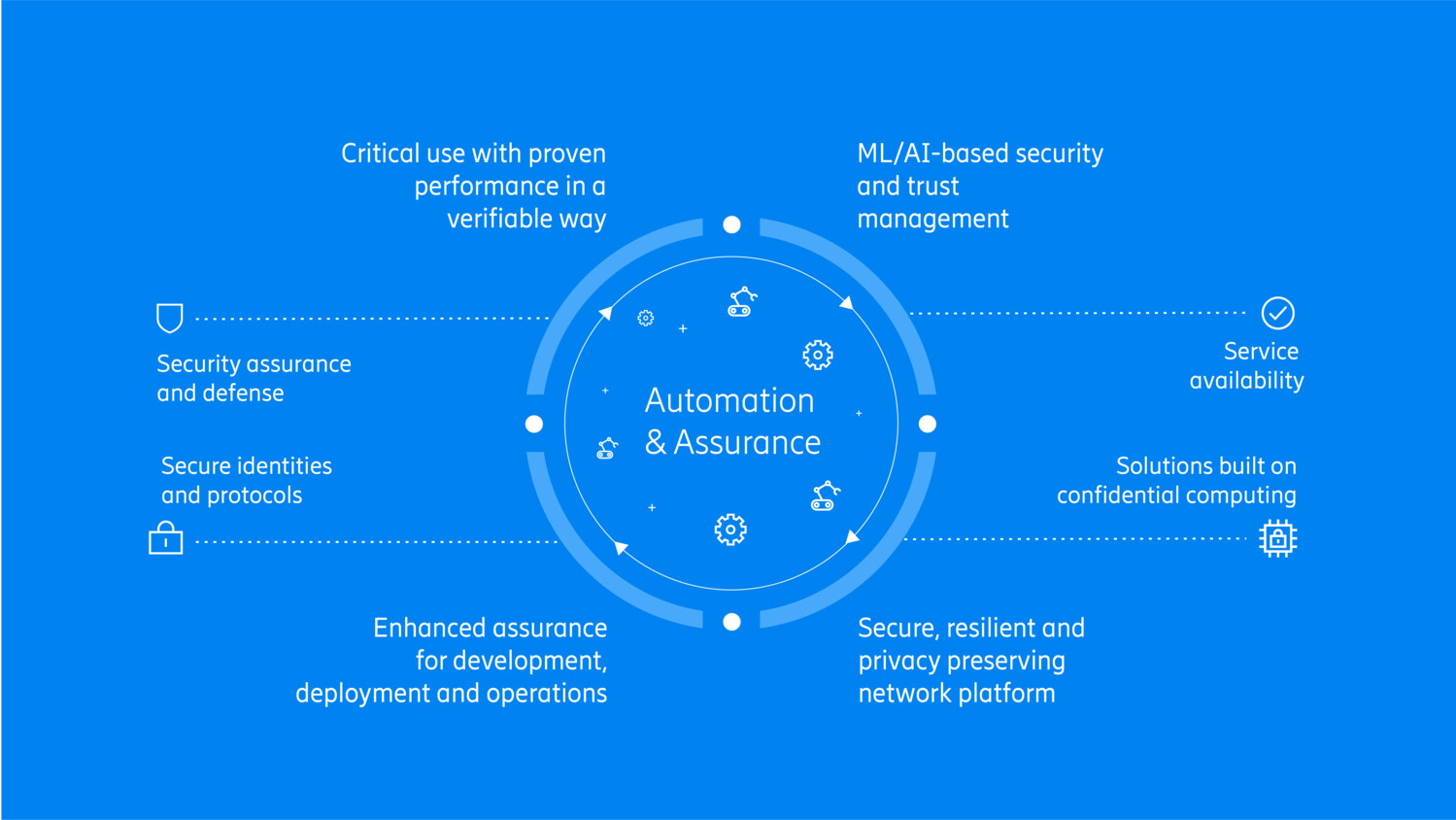
The trustworthy systems journey
The intelligent network platform offers security, privacy, reliability, availability, and robustness, to various degrees depending on the use cases. To realize these properties, different building blocks have been identified on the journey from 5G towards 6G.
Service availability
Increased focus on robustness, availability, and resilience of the 5G network platform supports new business and mission critical use cases. Take, for example, a factory - where disturbances in connectivity may cause production interruptions, and consequently, great financial impact.
Breaking this down, we identify efficient and robust resource provisioning, automated network operations, and predictive network operations as key requirements of consumers and industries in the future.
Solutions built on confidential computing
Confidential computing will be an important enabling technology for security with systems becoming increasingly virtualized. It allows us to protect data as it is being processed and stored, providing assurance to both users and regulators. Confidential computing will also form a basis for secure identity management.
A long-term vision is that we will have automated trust assessment of all network elements, including nodes, devices, applications, and virtual resources in the cloud, rooted in trusted execution environments and with artificial intelligence based processing.
Security assurance and defense
Security automation and assurance mechanisms are essential for the development, deployment, and operations cycle. Present-day security assurance methodologies put a lot of focus on product security. Our long-term vision is that solutions will have built-in assurance and proof-of-compliance mechanisms, supporting communication service providers and their subscribers, assuring full compliance with security specifications, standards, and regulations. New tools, some of which will use AI capabilities for detecting threats and dynamically responding to them, will significantly enhance assurance in the future.