How to keep 5G data secure with software probes
5G Core is built for security
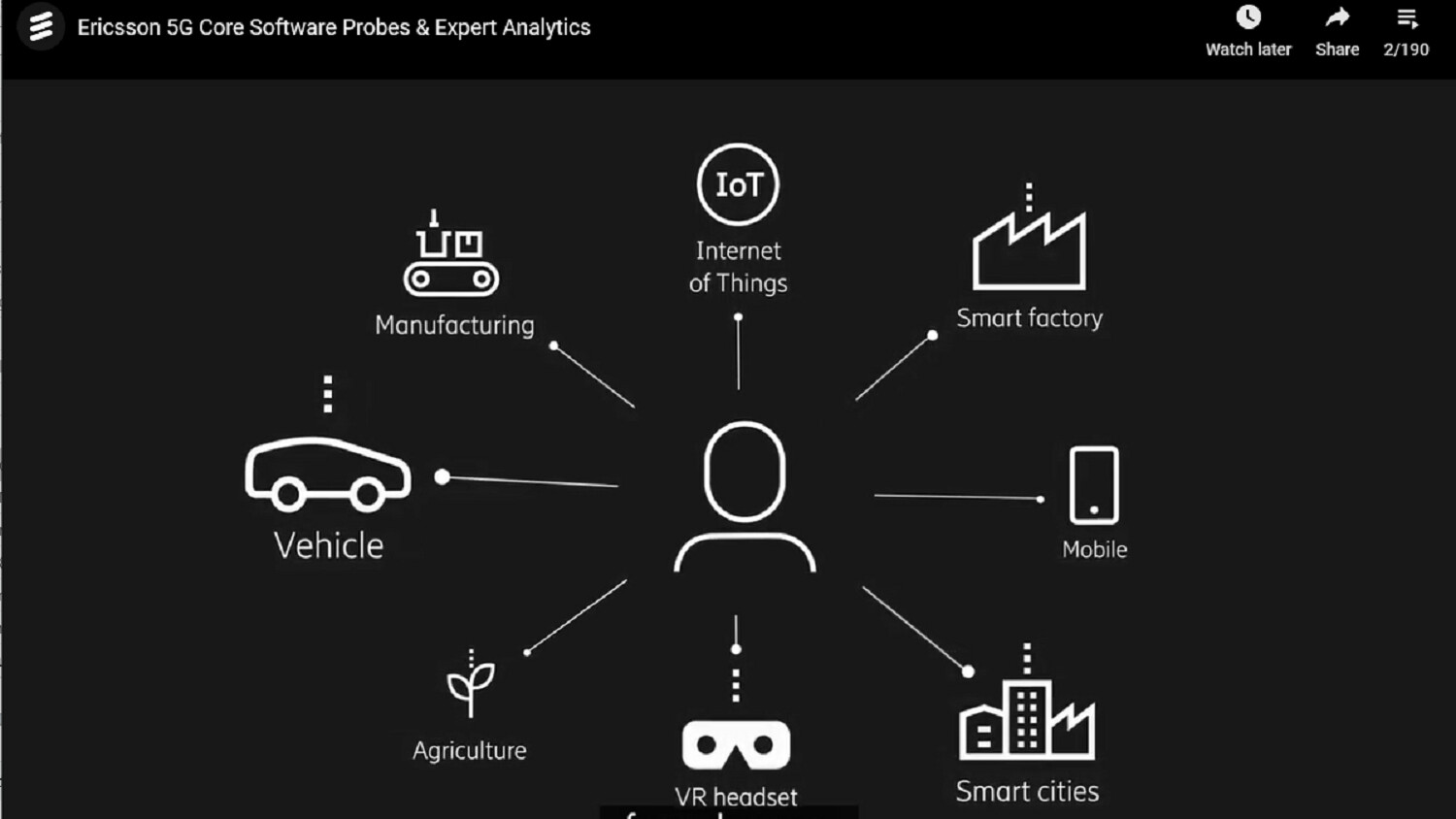
Enhanced security and privacy are cornerstones of 5G Core, but service providers still need to be able to capture quality, actionable data to secure the end-customer experience. Specifically, I’m referring to the data needed to perform troubleshooting, monitoring, customer care and analytics for marketing campaigns. But can this be done in 5G Core using traditional probing methods, without breaching security?
Traditional external probing methods are officially unsustainable
The 3GPP standardization for 5G considers enhanced security to be an essential network component. Imagine, for a moment, that we live in a world where it’s common for open heart surgery to be conducted remotely, and I’m sure you’ll agree. The need for a secure, reliable network has resulted in the introduction of a new Service Based Architecture (SBA) that utilizes encrypted interfaces between network functions (NFs). Traffic between network functions is deployed in a cloud native 5G Core Kubernetes node and will not be visible outside the cluster, meaning traditional probing solutions are unsustainable.
Service providers will face challenges tapping 3GPP traffic with probes located in the NFV infrastructure or underlying hardware infrastructure without breaching 5G Core’s system security.
Keeping sensitive data secure with software probes
The new security measures in 5G Core pose a new challenge when it comes to capturing data. How do service providers solve this issue, and keep sensitive data secure? The answer: use built-in software probes. Now, service providers can implement built-in tapping and probing functionalities within cloud native network functions software themselves.

Figure 1. Software probes solution overview
With software probes, service providers can ensure sensitive data, such as event reporting or full mirroring of 3GPP interface data, gets from A to B while maintaining security. Any data can be delivered over transparent, secure and standardized interfaces to provide customer centric insights and software probes. Watch the video for a quick overview on how this works.
By using built-in software probes for analytics, we ensure end-to-end protection of data which is sensitive from both a privacy and security perspective. Probing data can also be captured and anonymized within the network functions, and sensitive data doesn’t have to leave the network function. When we speak to service providers, most of them say they expect built-in software probes to be mandatory in the future, but their outlooks also vary depending on how far along they are in their 5G journey.
However, these built-in software probe solutions will be integral elements of future 5G networks, helping the industry meet increasingly strict security and privacy regulations and enabling service provider growth within a zero-trust environment. The 3GPP regulations specify that the 5G control plane must ensure trust and integrity – in other words – there must be ultimate trust between communicating network functions and the traffic must be protected from external attempts to listen in. With built-in software probes, this trust and integrity is fulfilled, and 5G networks hosted in a public or shared cloud environment can safely rely on these network functions. If sensitive, private data is extracted in the probing function and it will also be encrypted to ensure compliance with privacy regulations, such as GDPR in Europe.
A quick guide to tapping, probing and brokering functions
Now that you’ve been introduced to software probes, let’s familiarize ourselves with the words like ‘tapping’, probing’ and ‘brokering functions’.
| Tapping: | Capturing or mirroring network packets sent between Network Functions (NFs). |
| Probing: | Basic processing of packets to create metadata or correlate data sources. |
| Brokering functions: | More advanced data processes like filtering traffic, meeting multiple consumer needs, or optimizing security and traffic flow. |
Learn more about how tapping and probing can be achieved in cloud native container-based environments without jeopardizing network security in our latest paper: Securing the 5G experience with software probes.
In the paper you’ll also learn how these solutions can help minimize total cost of ownership – imagine the relief when you no longer have to maintain thousands of tapping points with hundreds of aggregators and physical probes!
New 5G Core podcast released
The advent of 5G will only increase the importance of probing to support the new needs of both customers and businesses. In our latest podcast, we discuss:
- How to ensure customer experience improves with 5G from day one
- How software probes with expert analytics can provide customer centric insights to secure superior experiences and fast-track the 5G onboarding
- Will probing and access to actionable data play a vital role in increasing automation, and the application of artificial intelligence and machine learning?
Listen to the 5G Core podcast, featuring Folke Anger, Head of Solution Line Packet Core, Thomas Kinnman, Head of Solution Line OSS at Ericsson and Dez Blanchfield, Industry Analyst, Business & Technology Consultant.
Read more
Discover how 5G core unleashes a new era of scalable and service-rich cloud-native networks.
Explore 5G core solutions that make it possible for you to deploy, scale and evolve your operations across multiple deployment scenarios.
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.