Privacy in mobile networks is at the top of our agenda
Privacy – a topic on everyone's mind
At Ericsson we identify privacy as one of the core properties to establish trustworthiness in 5G networks. Our work on privacy includes efforts in standardization, design and implementation considerations, adherence to regulatory requirements, and research activities to further address privacy aspects in the mobile networks.
One of the more recent developments affecting privacy is the EU General Data Protection Regulation (GDPR) that came into effect in 2018. The GDPR comes with a wide range of existing and new consumer rights that needs to be addressed by todays telecommunication systems and that 5G networks will have to support from the day of their launch. It shows that regulations are becoming stricter when it comes to how and what kind of processing on personal data a mobile operator can do.
Let's have a look at how we realize privacy requirements, and work towards future enhancements, in the mobile communication networks.
How we address privacy
To address the different aspects of privacy, we highlight the following four areas:
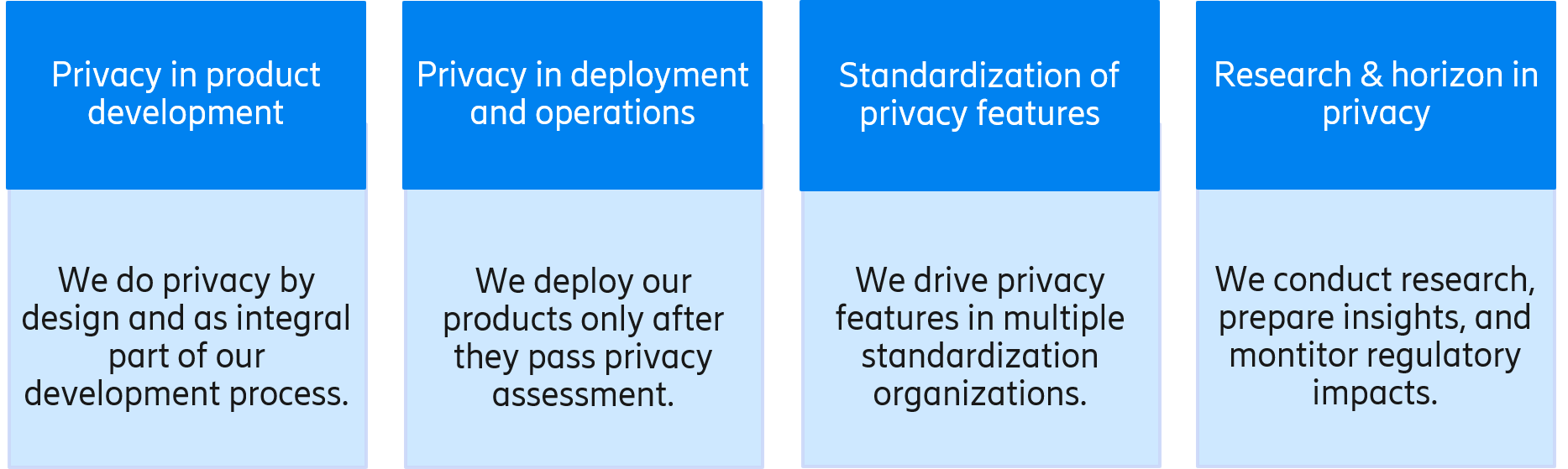
Privacy by design in product development
For many years Ericsson has worked systematically to incorporate privacy considerations into all phases of product development using our internal framework, the Security Reliability Model (SRM). This allows us to consistently deliver on security and privacy ambitions in our products. Through the model, we manage risks when developing software and hardware technologies and ensure compliance to regulatory demands such as the GDPR.

By defining baseline security and baseline privacy requirements for products and solutions, the Ericsson SRM ensures security and privacy by design, build, and use. The SRM also defines a set of privacy assurance activities, dividing them into three tiers: basic, advanced and tailored. While basic-level activities are performed by product development, advanced- and tailored-level activities are performed for parts of products in need of a higher privacy assurance level.
In this model, risks are analyzed in mandatory internal privacy impact assessments. The assessment also identifies the data which might have an impact on privacy. When it comes to identifying privacy issues, and implementing privacy-preserving measures, our risk-based approach puts privacy risks in relation to the personal data being protected. In addition to traditional subscriber data (IMSI, phone number), there are other types of data related to subscribers in the 5G ecosystem, for example telematics data in connected vehicles, medical data from health care sensors, or information from connected homes. All this needs to be properly handled.
Using Ericsson baseline privacy requirements and Ericsson privacy design rules, mitigations are identified to protect the identified data. This may include new software features (privacy engineering), assurance activities (privacy assurance) and privacy documentation for the mobile network operator customers (customer product information).
A unified approach to privacy in deployment and operations
In addition to product development, privacy considerations come into play when providing services or delivering an offering as-a-service. The main challenges here come from management and handling of the personal data of our customers, mostly subscriber data.
One of the most relevant contemporary aspects to mention is international data transfers. There are several restrictions across jurisdictions of what data can be processed and where. This impacts the selection of data centers and the location of support operations. As an example, certain jurisdictions demand that data shall primarily be stored within the nation's borders. Also, geopolitical situations, like Brexit for example, make the situation more complicated at times.
Another important aspect is the sub-processing of data. Mostly for support and troubleshooting reasons, it might be needed to pass over data to data sub-processors. In such cases, even though everyone respects a high level of data protection, chances of potential issues should not be overlooked.
For this reason, we take steps to ensure that real data is processed as little as possible, for example in troubleshooting or testing, and we may use privacy protection mechanisms like anonymization and pseudonymization of data when appropriate to mitigate potential risks.
At Ericsson, we take a unified security and privacy management approach to, in an automated manner, ensure privacy in the networks, monitor privacy compliance in near-real-time, ensure that needed evidence is collected in an event of a privacy breach, and perform necessary communications. Further, our privacy monitoring process is connected to our product security incident response team (PSIRT).
Standardized approaches to privacy – a key element
Standardization is a process in which many stakeholders define how networks around the globe will work together. We are present in all the major standardization organizations working for security and privacy in mobile communication networks, like 3GPP, IETF, GSMA, ETSI NFV, and ONAP, to mention a few. We continuously shape the industry by driving standardization of privacy-enhancing technologies, striving for globally agreed solutions in the mobile networks.
For example, we were one of the main advocates and drivers in 3GPP for protecting 5G against IMSI catchers. Protocols in the 5G system are designed in such a way that long-term subscription identifiers are concealed over-the-air and short-term subscription identifiers are regularly refreshed. Therefore, traceability attacks where attackers attempt to identify or trace their victims by passively eavesdropping or actively probing subscription identifiers are impractical in the 5G system. In 3GPP, we also drove a framework for detecting false base stations. All these are important wins against passive/active location privacy attacks over-the-air.
Authentication enhancements in 5G systems is something we are currently driving in both the IETF (perfect-forward secrecy for EAP-AKA') and 3GPP (authentication enhancements in 5G). The aim is to increase the system's resilience against pervasive surveillance, by preventing an attacker who has gained access to the long-term secret key from being able to decrypt all past communications. Furthermore, if the attacker stays merely a passive eavesdropper, attacks against future communications are also prevented.
On the horizon
While ongoing discussions and regulatory measures address many privacy aspects, and by themselves generate attention to privacy in our connected world, the debate on personal information in different forms continues all over the world.
Efforts like the general data privacy law in Brazil, the California consumer privacy act or the India Personal data Protection Bill will impact how data is being handled to a similar degree as the GDPR, and the upcoming European ePrivacy regulation will affect electronic communications directly. In addition, there are research efforts addressing privacy on top of and beyond what is currently required and mandated.
From a mobile communication network perspective, addressing privacy concerns in many cases boils down to defining technical solutions that can control, protect, and verify the use of data, in accordance with requirements and expectations. Interacting and engaging with consumers, network operators, industry in large, regulators, and academia is thus key to explore and understand needs and values around privacy – beyond current regulation and practice.
For example, studies from Ericsson ConsumerLab show that people believe your device will soon know you better than you know your device, and that many people feel that the apps they use are constantly spying on them.
Learnings and insights then generate research through collaboration engagements such as EU 5G ENSURE or the project at UC Berkeley on privacy-preserving analytics based on confidential computing. Other examples of our research are the transparent logging which provides new means to trace data that informs the user how their data has been used, anonymization techniques to prevent the linking of data to a specific person, intelligent means to lock and control you own personal data online, mechanisms to enhance privacy in 5G networks, and our award-winning thesis on privacy and 5G.
Finally, with the increased interest in machine learning and artificial intelligence (AI) comes the notion of handling personal data and information so that the data is protected while being processed, and so that conclusions concerning the persons in question are drawn with respect and responsibility. This expands the topic even further and lays the ground for more exciting research and discussion in the space of privacy.
In short, privacy is a topic that remains top of Ericsson's agenda.
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.