NFV builds 5G trustworthiness through security compliance
Building trustworthiness for 5G networks is of paramount importance as 5G networks start to play a critical role in the operation of society and delivers services that directly pertain to citizens and societal functions. As stated in Ericsson’s Technology Trends 2020, namely Trend #6: ‘Trustworthy Infrastructure’, increasing the trustworthiness in 5G networks boils down to ensuring that all parts of the network fulfill all requirements, including security requirements, even those that are the most mission and business critical.
An important part of the 5G network is the underlying NFV and software-defined networking (SDN) technologies, which help address the diverse needs of emerging applications (for example, higher data rates and lower latency) and enable economies of scale.
NFV and SDN are becoming codependent. Where NFV is in charge of dynamically creating and managing the network functions and provisioning various network services, SDN provides the capabilities to manage and orchestrate the virtual networks among these services. In the following section, we use an NFV environment to refer to an NFV infrastructure with SDN support.
Security compliance and trustworthiness
In more practical terms, one possible solution to increase the trustworthiness of the NFV environment is by assessing the compliance of the implemented security controls with respect to relevant requirements in corresponding security standards (for example, NIST 800-53, ISO 27001/27002), regulations (GDPR, for example), and application-specific security requirements.
A security compliance assessment is a review of a system, both during its design time and at runtime. At runtime, the security compliance assessment fundamentally relies on adequate observability mechanisms such as logging and monitoring. These mechanisms allow data items from the deployed system to be collected, to capture its current security state and perform adequate security requirement verifications.
SDN and NFV enable enhanced security capabilities. However, they also introduce additional complexity, leading to challenges with security compliance management – particularly in logging, monitoring and the verification of compliance of an NFV-based 5G environment. Figure 1 illustrates a high-level overview of these topics and how they interconnect.
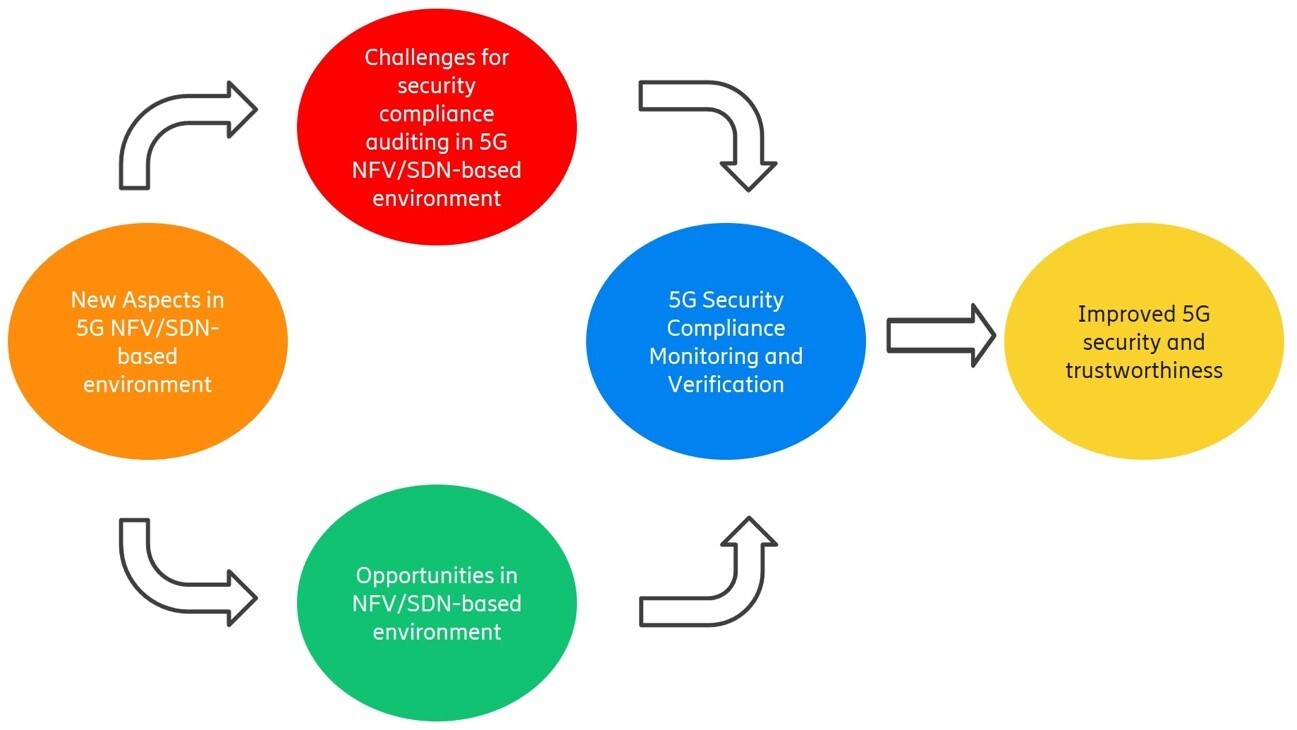
Figure 1: New aspects brought by NFV/SDN can outweigh the challenges, to benefit security compliance monitoring and verification, and increase trustworthiness in 5G.
Despite possible challenges ahead (multi-vendor, multi-level aspect, multi-tenant, dynamism and scalability) with respect to the use of recent technologies such as NFV in future-generation networks, these same technologies also open up new opportunities. These are based on effective automation, adaptable and scalable security compliance monitoring and verification solutions towards an improved 5G security and trustworthiness.
Key opportunities enabled by NFV to enhance security compliance and monitoring
Figure 2 illustrates the opportunities enabled by NFV to enhance security compliance.
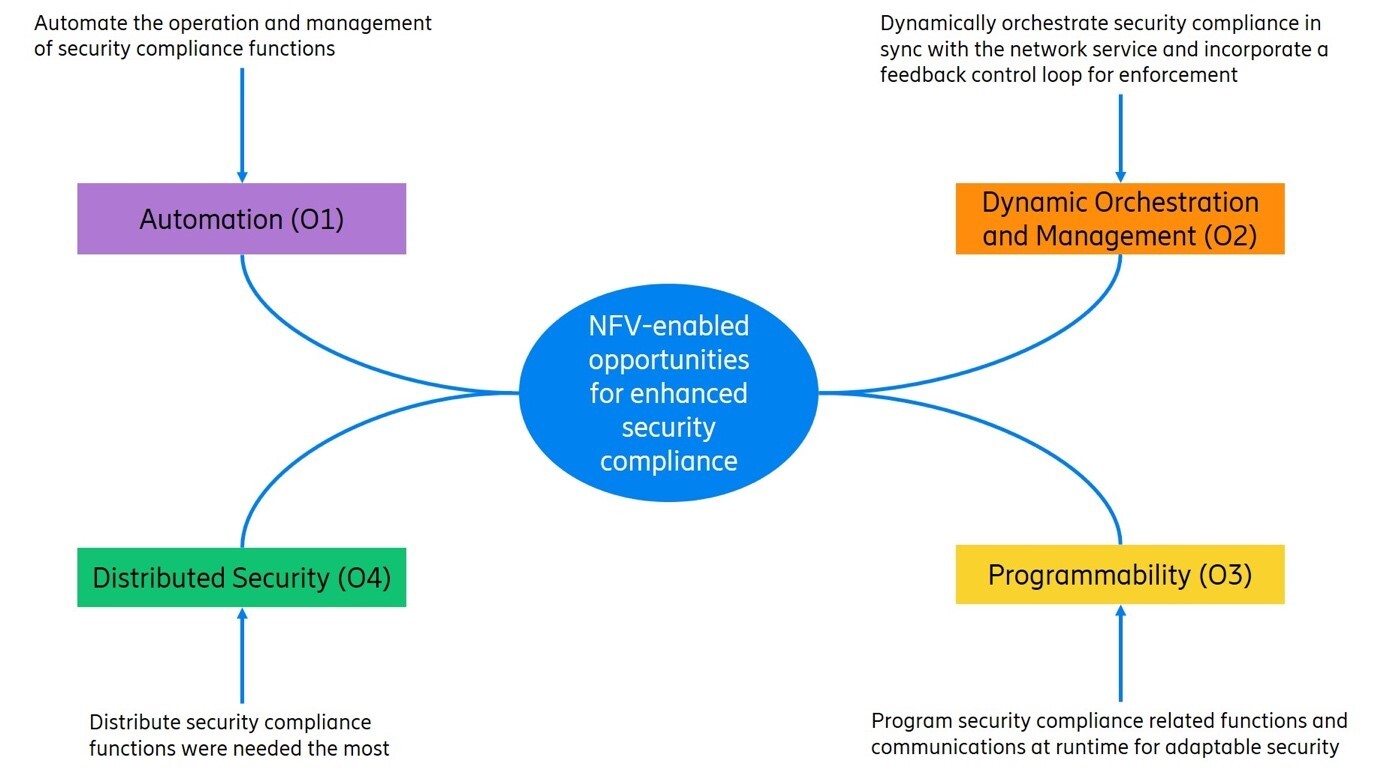
Figure 2: Summary of the key opportunities brought by NFV to enhance security compliance and monitoring
Below we go into more detail with these opportunities and explain how it would work.
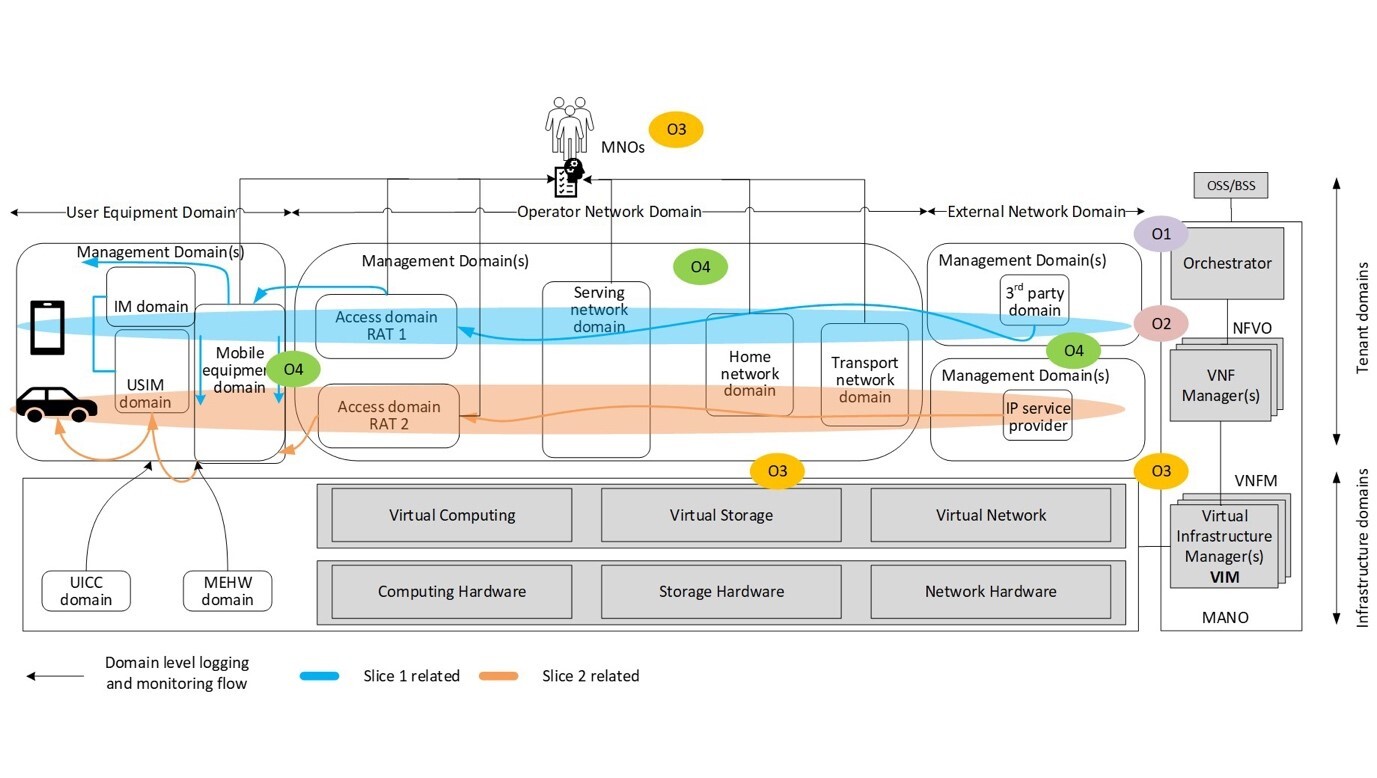
Figure 3: Opportunities with respect to the enabling components and the possible benefiting domain in a 5G environment.
O1: Increased automation
NFV and automation go together, and this is made concrete here by the Management and Orchestration (MANO) layer. NFV promises significant cost savings by providing the opportunity to automate the creation, reconfiguration and scaling in and out of network services – and to do it on-the-fly, based on the workloads’ needs. This mechanism is key when it comes to automating security mechanisms, as well as their operations and management. For example, logging, monitoring, and verification functions can be automatically instantiated and managed, depending on what and when security mechanisms are needed by the virtual resources and applications.
With the help of advances in AI-based approaches, NFV automation can help achieve better and faster insights into the security posture and proactive security compliance enforcement to avert compliance breaches.
O2: Dynamic security orchestration and management
5G operators leverage NFV and SDN to automatically create network services on-the-fly to accommodate their customers in real time. With the help of NFV orchestration management, they can rapidly scale network services in and out. Building on the dynamic nature of NFV and its multi-layered management orchestration capabilities, runtime logging, monitoring, and compliance verification mechanism deployment can be efficiently orchestrated at different layers.
As the virtual resources can be dynamically modified or instantiated, NFV admins can instantiate new monitoring instances, reconfigure or modify the existing ones at the right location in the network according to available resources or security contexts. Note that even though this was possible before, the dynamism and flexibility provided by NFV make this approach much easier to realize.
Furthermore, these augmented orchestration capabilities can be incorporated with a feedback control loop to mitigate non-compliance at runtime, reduce response time, and non-compliance window.
Finally, the trustworthiness of the environment is enhanced through the combination, collaboration, and aggregation of the distributed security functionality throughout the NFV infrastructure.
O3: Improved programmability
Programmability can offer the flexibility needed to have adaptable security, instead of a one-size-fits-all approach.
Since NFV is rooted in virtualization and softwarization technologies, it offers the augmented programmability of virtual resources for delivering the network service in a flexible and dynamic way. This programmability can in turn be used to provide security functions such as logging, policy monitoring, and verification mechanisms, in a dynamic and flexible way, adapting them at runtime to the provided services and their security contexts.
For example, the granularity of logging can be programmed to fit specific contexts and policy verification prioritizing certain critical policies. Service providers can therefore leverage this opportunity to tailor the compliance verification and monitoring functionalities according to their applications and their needs at different administrative domains.
O4: Highly distributed security functionality
The softwarization aspect in NFV provides a good fit for highly distributed approaches – not only for network services but also for security. 5G network services are deployed across multiple administrative domains, generally corresponding to different security domains (access, and transport network domains, for example). Additionally, they can be instantiated, managed, and orchestrated by different administrative domains.
The NFV approach allows for the dynamic distribution of the instantiated VNFs throughout the virtualized infrastructure at the edge, at the core or at the operator’s data center. In the same way, monitoring can also be distributed and take place at different locations in the operator’s network covering different parts of the network. Even though it was possible before NFV to do so, the static nature of hardware-based solutions made practical implementation more difficult.
Putting the theory to the test
To illustrate different aspects, we presented a simple example in Fig. 3. Let’s assume that the 5G service provider has instantiated two network slices for two different customers: e-Health, and Automated and connected vehicles.
The e-health customer has privacy concerns. Protected health information must be used in accordance with the requirements of the relevant regulations, for example the Health Insurance Portability and Accountability Act (HIPAA) in the USA, and Article 9 of the European GDPR.
The Automated and connected vehicles (AV/CVs) industry is subject to other requirements including IEEE 1609.2 security services for authentication of vehicle safety messages.
Security compliance should be guaranteed for each of the two network slices: e-Health and AV/CV. These slices are deployed across different administrative domains over different physical and virtual computing, networking and storage resources.
To satisfy the needs of the e-Health slice network services (for example, low latency or load balancing), several VNF instances from different vendors may be instantiated at runtime. In our example, different monitoring and verification functionalities can be instantiated as the virtual resources are created, scaled in/out in different virtual networks and in different slices using NFV programmability capabilities (O1). The service provider may then automatically distribute diverse security functionalities throughout different administrative domains (O2).
Additionally, the NFV management can create the most suitable security functionality for each VNF instance based on VNF functionality and needed Quality of Protection (QoP). The subsets of the security compliance verification for the relevant requirements can then be put in place for different network slices (O3).
Finally, in case of a cyber attack on a particular e-Health slice, the security management may choose to dynamically instantiate/reconfigure the security mechanisms at the edge, to eliminate the attack closest to the source (as a better location). Another option could be to steer the traffic into the operator data center for load-balancing reasons (for more efficiency, for example) (O4).
Building 5G trustworthiness with NFV-enabled opportunities
In conclusion, there may be increasing concerns around security as 5G rolls out globally, but if implemented properly, NFV can provide a fertile ground to implement a more efficient, dynamic and flexible approach for security compliance monitoring and verification.
Learn more
Read Ericsson’s full Technology Trends 2020 report.
Read more about Ericsson’s security manager and how Ericsson is ramping up with different NFV security products to improve security of future generations telecommunication networks.
Here’s our guide to 5G network security.
Read our report Mastering complete 5G network security.
Learn the latest news on Ericsson RAN and network security standards.
Learn about Ericsson’s 5G security collaboration with Canada’s Concordia University.
Here’s how to master E2E network security when introducing 5G core.
Read more about 5G Core.
Acknowledgement: The author would like to thank Mengyuan Zhang, Makan Pourzandi, Ari Pietikäinen, Jukka Ylitalo, Giovanni Zanetti, Jonathan Olsson, and Jorden Whitefield for their valuable contribution and review of this blog.
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.