Here’s how 5G security can be your industrial virtual airbag!
Airbags can be found in cars, on motorbikes, and even on downhill skiers. Whatever their location, they all aim to protect humans in hazardous situations by fully inflating within milliseconds.
Safety-related systems in industries aim to provide protection to critical assets including human life. Yet, as more industries become connected to the outside world, safety functions themselves need protection from intentional malicious attacks. In this blog post, we look at safety security in general, with a focus on how 5G security can fill the needs of security for safety.
Safety is generally defined as the state of being free from unacceptable risk of direct or indirect harm to human health, environment or property. Safety requirements are among the most important when designing an Industrial Internet of Things (IIoT) system, and that is why dedicated elements, named safety-related systems (SRS) or safety-instrumented systems (SIS), are used to assure safety.
These systems are responsible for maintaining safety by continuously monitoring safety-related statuses via sensors and taking necessary actions via actuators, similar to how an airbag inflator is triggered when crash sensors detect an unusually high deceleration. A robot reducing its operating speed when a human is nearby or an automated sprinkler turning on when a potential fire is detected are both examples of such “industrial virtual airbags”.
Safety and security
Security and safety are interrelated concepts that have similarities and differences. Both have the main objective of preventing harm from unwanted incidents, and therefore they are related to risk and require risk management. The main source of risk in safety is unintentional incidents such as natural disasters, accidents, human faults or system errors. Security risks, however, originate from deliberate malicious adversaries acting as creative and determined agents, which could be humans or AI-based software. Safety related incidents impact the physical world , while exploited security vulnerabilities can affect both the physical and the cyber world.
Traditionally, security-related systems and safety-related systems have mostly been split and operated in their own cyber or physical domains. But recently, these two systems are being intertwined, as seen in Figure 1. This happens when Industrial IoT systems connect conventional industrial system elements like machines and robots – so-called Operational Technology (OT) – to enterprise Information Technology (IT) networks and the internet.
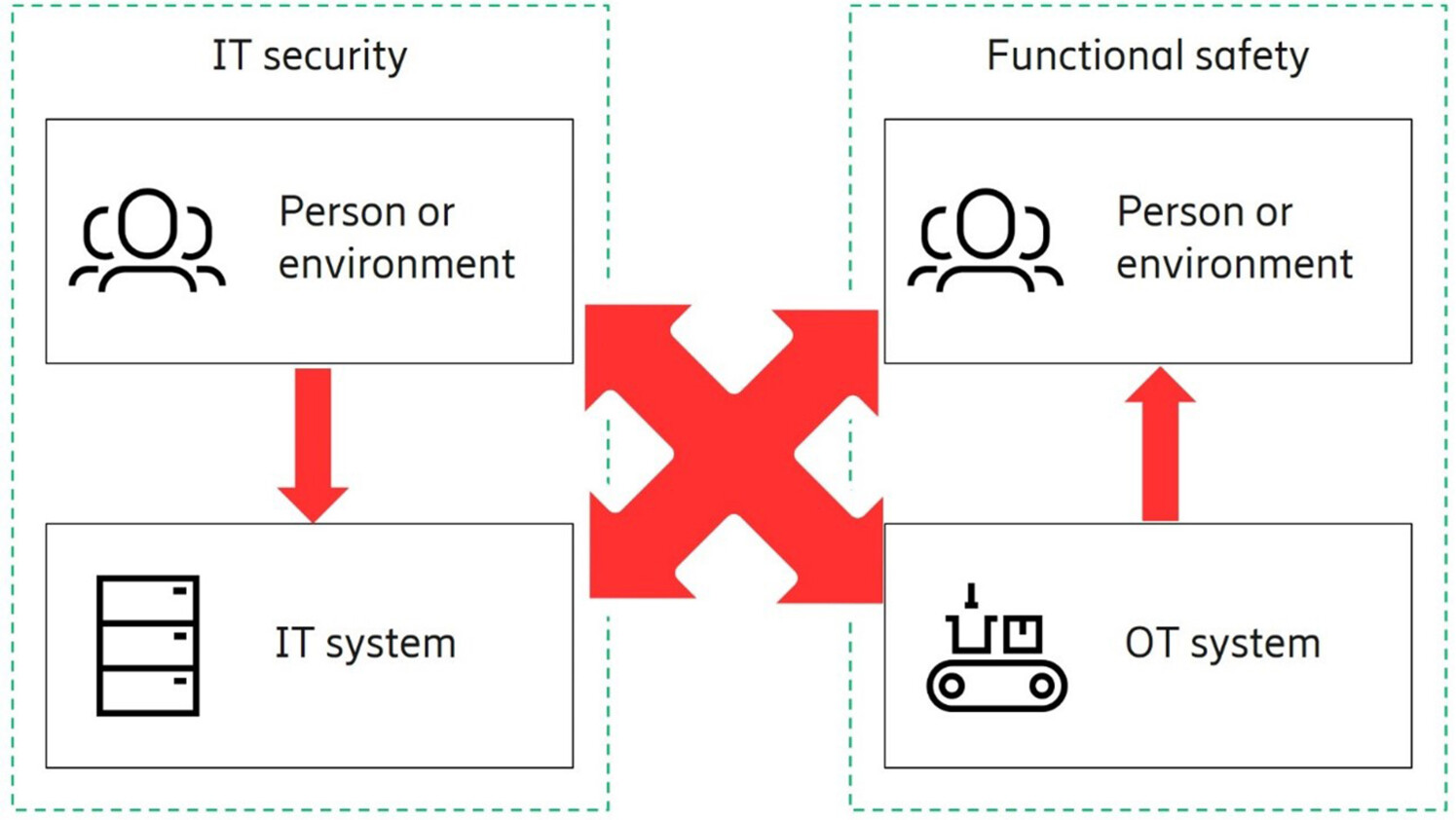
Figure 1: The safety/ security relationship
An attack initiated from the IT network by malicious adversaries can cause harm to the OT systems. The damage can be exacerbated by directly targeting the safety function in the OT network. Therefore, security protection should be provided on the safety function. This is possible with proper specification of security requirements on safety.
Security requirements on safety
One main type of component in an industrial automation system is called Equipment Under Control (EUC). These components are the devices such as robot arms or automated guided vehicles used in a manufacturing process. EUCs are mostly controlled by software, called Control Programs, running on dedicated hardware. Safety-related actions of an EUC are controlled by separate software called Safety Programs, which also usually runs on dedicated hardware. As depicted in Figure 2, besides the Safety Program, there are two more main components of a generic safety system: (i) Safety Sensor(s), and (ii) Safety Actuator(s), both of which can be attached to EUC or be separate.
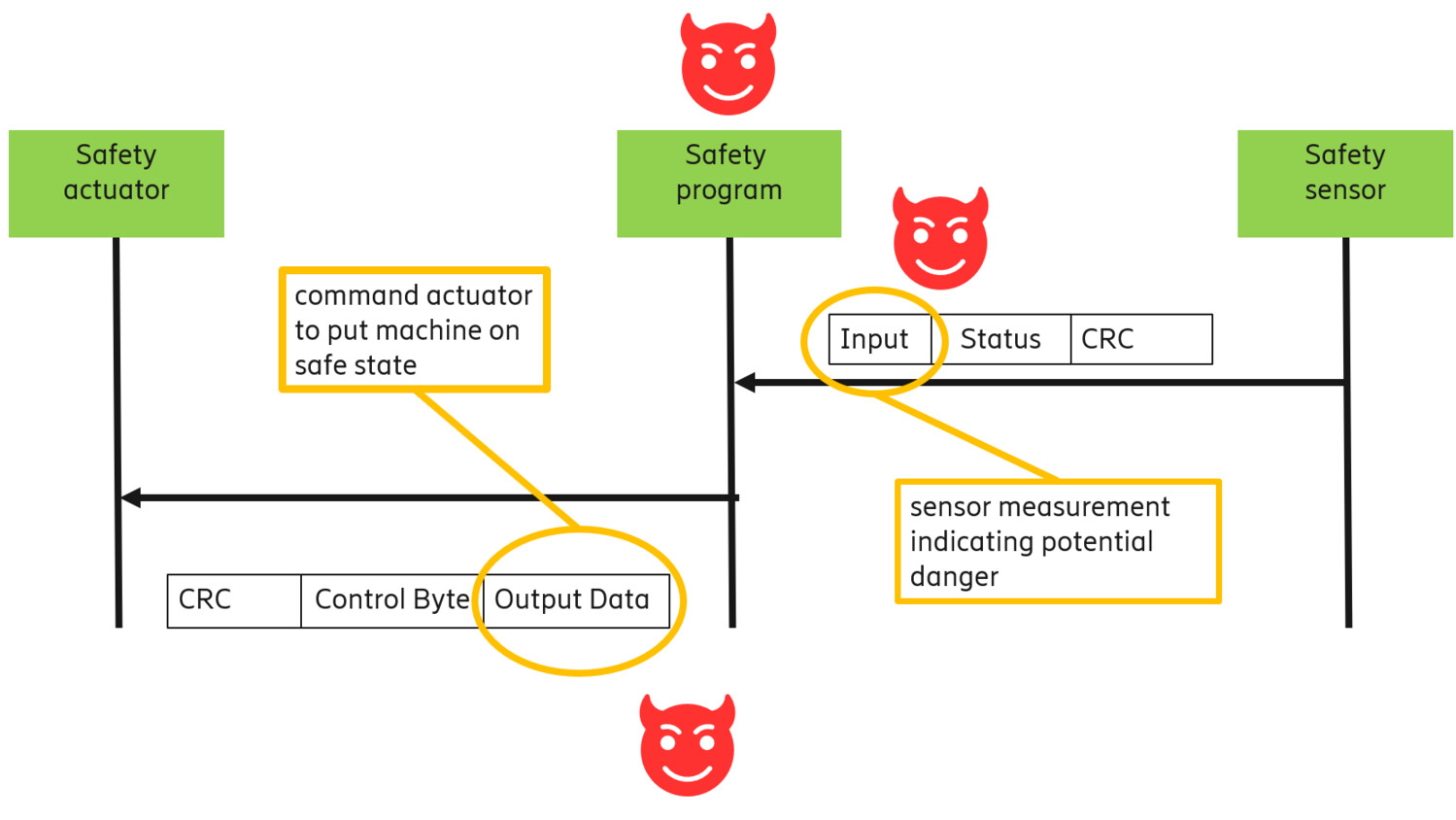
Figure 2: Safety related system components.
Safety-related systems in smart manufacturing detect any safety-related incidents through safety sensors and take preventative counter actions through safety actuators before any hazardous event occurs. Possible safety actions might be performing an emergency full stop, slowing down the speed of rotating components, or any other fail-safe mode action previously defined in Safety Program code.
In order to detect dangerous events and take timely action, protection of source code, as well as communicated protocol messages is vital. Communication between components of a safety-related system include, for example, the transfer of measurement data from safety sensors to a safety program or action commands from the safety program to safety actuators. This communication is critical and handled by application layer safety protocols. Such protocols, for example Profisafe, handle possible faults and hazards caused by the underlying communication network with the objective of keeping error probability under certain limits. However, these protocols are not originally designed to provide protection against malicious intentional parties but only against unintended faults like channel errors.
In normal operation of a safety-related system, the Safety Program periodically polls Safety Sensors, which in turn send their measurements about safety-related ambient conditions such as temperature or pressure. Measurement values are compared to pre-set threshold values in the Safety Program. If the received sensor measurement is out of the range dictated by the threshold values, a potentially dangerous situation is detected, and the Safety Program sends the control command to the Safety Actuator to perform action to mitigate damage to people, equipment or environment.
As depicted in Figure 2, this whole critical process is composed of: (i) sharing ambient condition information measured by sensors, (ii) assessing potential dangerous situations by the Safety Program and (iii) commanding safety action to safety actuators.
If the process is not correctly and timely performed by the overall safety function, unwanted consequences can occur. Therefore, protecting the integrity of safety-related messages, authenticating their sources, controlling access to safety-related system components and assuring the Safety Program source code and configuration parameters like thresholds are intact is very important.
Protecting the safety function
Frameworks and standards provide a valuable guide on how to provide security and safety for industries. Nevertheless, until recently, most standards regarded security and safety in industrial systems as concepts to handle separately. Consider for instance the standards published by the International Electrotechnical Commission:
- Safety-system related application, design, deployment and maintenance methods are defined in IEC 61508. It is a basic functional safety standard applicable to all industries.
- Security aspects of industrial control systems are covered by IEC 62443, with several series dealing with various parts.
Two newer IEC standards do address safety and security together, with a sector agnostic approach.
- IEC 63069, one of the first such standards, guides the joint application of the IEC 61508 and IEC 62443. IEC 63069 describes how to handle safety and security analysis and how to resolve conflicts arising from different countermeasures within the lifecycle of the system.
- IEC 63074 offers guidance on the use of IEC 62443 in cases where security threats and vulnerabilities could affect functional safety of the system.
These standards do explain what kinds of policies and practices should be followed to protect the safety function and Industrial IoT systems in general. What they usually do not do is present sufficient information on how to put these best practices into action using existing technologies. Now, let us start to fill this gap. Table 1 below maps 5G security features to the particular security requirements needed to protect the safety function.
| Security Requirments | Relation to functional safety | 5G Security Features |
| Message Integrity | Protection against malicious parties aiming to modify critical safety messages intentionally | User plane integrity protection |
| Message & Source Authentication | Countering against safety protocol messages originating from unauthorized parties |
5G-AKA, EAP-AKA, EAP-TLS Mutual authentication |
| Access Control | Isolation of safety-related devices & networks from non-safety OT devices & networks |
Network Slicing Closed Access Groups |
Taking the rows one by one:
- Integrity protection of critical safety messages can be assured by the user plane integrity protection feature in 5G.
- Communication between main components of a functional safety system – comprising Safety Program, sensors and actuators – should be secured in terms of message and source authentication. 5G allows use of various types of strong Extensive Authentication Protocol (EAP)-based authentication methods which can be deployed to provide mutual authentication also for IoT devices without a SIM-card.
- The network slicing and closed access group features of 5G support creation of proper security zones between safety-related device networks and other device networks, and therefore prevents potential malicious message flows from a compromised device or network segment to the safety-related system.
5G mechanisms for secure credential storage and processing provide strong protection against identity compromise and spoofing. More details on these 5G security features supporting safety can be found in the Ericsson Whitepaper “5G security - enabling a trustworthy 5G system” as well as 3GPP Technical Specification “TS 33.501 - Security architecture and procedures for 5G System”.
Before concluding, let me emphasize a few points:
- To provide protection, all the technical security features mentioned above must be implemented and enabled. It is not enough to only do one or two.
- All these solutions for securing safety functions should be considered for the whole system lifecycle.
- Implemented countermeasures should be monitored and improved based on results and on lessons learned from previous safety-security events.
When properly implemented and used, 5G security could then act as a virtual airbag for safety in industrial settings.
Explore more
A more futuristic perspective on trustworthy systems for the 6G era around 2030 can be found in the Ericsson Whitepaper “Ever-present intelligent communication”.
Learn more about our research into Future network security.
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.
