How can Cloud RAN strengthen your network security?
Press play on photo to watch the video
Do you want to listen to this videoepisode instead? Play the audio only.
Cloudification of RAN opens some exciting business opportunities for mobile network operators. One of the benefits is utilizing the same hardware for different applications, known as “resource sharing”. The next one is high reliability and flexible scaling of compute resources, known as “agility”, provided by the cloud Infrastructure. The list of new deployments and capabilities is further extended with the improved network automation capabilities and optimized performance gained from the non-real-time radio intelligent controller (Non-RT RIC).
Enhancing network security is also an important capability of the Open RAN. Mobile network operators are already the number one target for cyberattacks, as Crowdstrike’s 2021 Global Threat Report reveals. Consequently, gaining and keeping absolute security in the network is a must-do.
What advantages does Open RAN bring in the area of network security? Security can be enhanced through the secure use of open-source software that can enable transparency and common control. It can also happen through the application of specified open interfaces, ensuring the use of interoperable and secure protocols. Other benefits include disaggregation, which enables supply chain resilience through vendor diversity, and the use of AI/ML, allowing visibility and intelligence to achieve greater security. The move to the cloud also enables the possibility of deploying nodes with high availability and redundancy. And the list goes on.
Don’t get too excited, though, because Open RAN also brings new considerations to the secure deployment of 5G critical infrastructure in the cloud due to the expanded attack surface.
Let’s take a deeper look at the main security challenges to be solved in Open RAN.
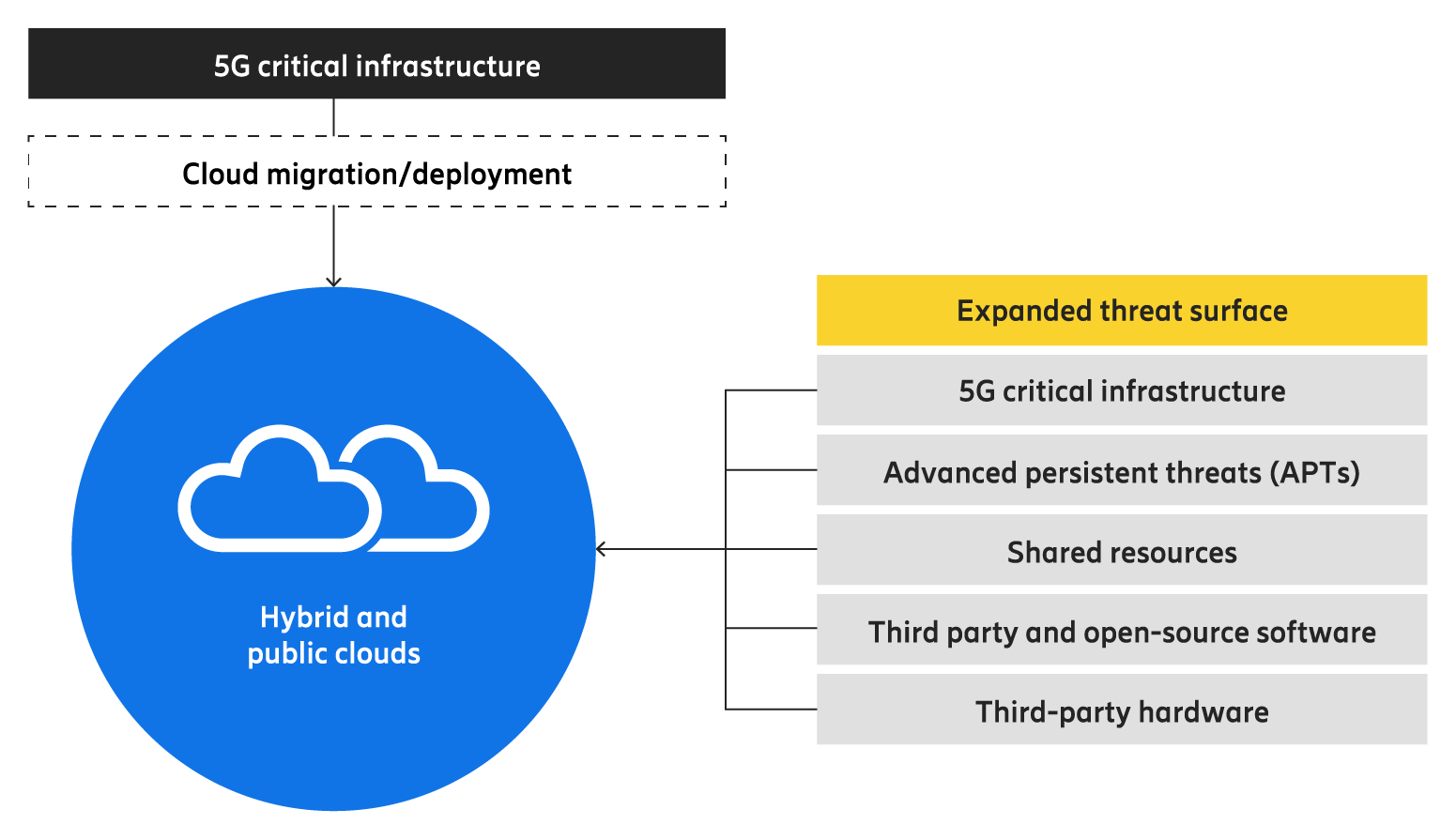
5G critical infrastructure has expanded the threat surface in the cloud
What are the four main security challenges to be solved in Open RAN?
1. Cloud introduces internal threats
As 5G migrates to the cloud, the attack surface gets broader, and consequently, new threats to critical infrastructure must be considered. ENISA’s NIS Cooperative Report on Open RAN Cybersecurity identified 5G Core and Open RAN to have increased risk of internal threats in the cloud due to greater dependency on cloud service providers, lack of defined security roles across stakeholders, resource sharing with other tenants, broader use of open-source software, and use of insecure third-party hardware.
What were assets running in networks on infrastructure in facilities owned, managed, and controlled by the operator are now operator-owned assets running in networks on infrastructure in facilities owned, managed, and controlled by a third party or third parties. The good news is that deployment in a mobile network operator’s private cloud can reduce risks from the threats identified by ENISA.
It is important to consider cloud threats when performing a risk analysis, particularly for deploying 5G critical infrastructure in the cloud.
2. Lack of multi-layer protection
Each layer of the cloud stack must be protected from external and internal threats actors who can exploit vulnerabilities at each layer of the cloud stack. The data, containers and applications, container run-time engine and orchestration, host operating system, and infrastructure layers share common vulnerabilities. Insecure APIs, weak encryption, security misconfigurations, and exposed credentials may compromise confidentiality, integrity, and availability of data and network functions.
An example of such threats posed by the cloud was presented by Karsten Nohl. An industry-recognized ethical attacker demonstrated in his video at the MCH Hackers Conference that exploits can be performed on an Open RAN system running in a cloud-native environment without properly secured configuration of the operating system, container run-time, and orchestration.
3. Open-source software further exposes the supply chain
The increased use of open-source software in cloud deployments has many advantages, but it also requires proper handling to mitigate inherent risks in the supply chain coming from the lack of security focus by contributors and malicious threat actors. Inherited vulnerabilities may compromise a trusted manufacturer’s software or hardware. Open RAN developers must apply due diligence to ensure open-source software is securely consumed.
4. Shared responsibility model
While mobile network operators are accountable for the security posture of their cloud deployments, the Cloud RAN deployment model influences the risk assessment with multiple stakeholders. All of them - vendors, mobile network operators, and cloud service providers - are responsible for implementing security control.
The key stakeholders in cloud deployments are a cloud service provider and a cloud consumer - mobile network operator. Mobile network operators can deploy 5G critical infrastructure in hybrid and public clouds.
In those more complex and dynamic cloud deployments, the risk of security misconfiguration increases, and automation is needed to ensure that both the cloud platform and the telco application follow the intended security baseline and policies.
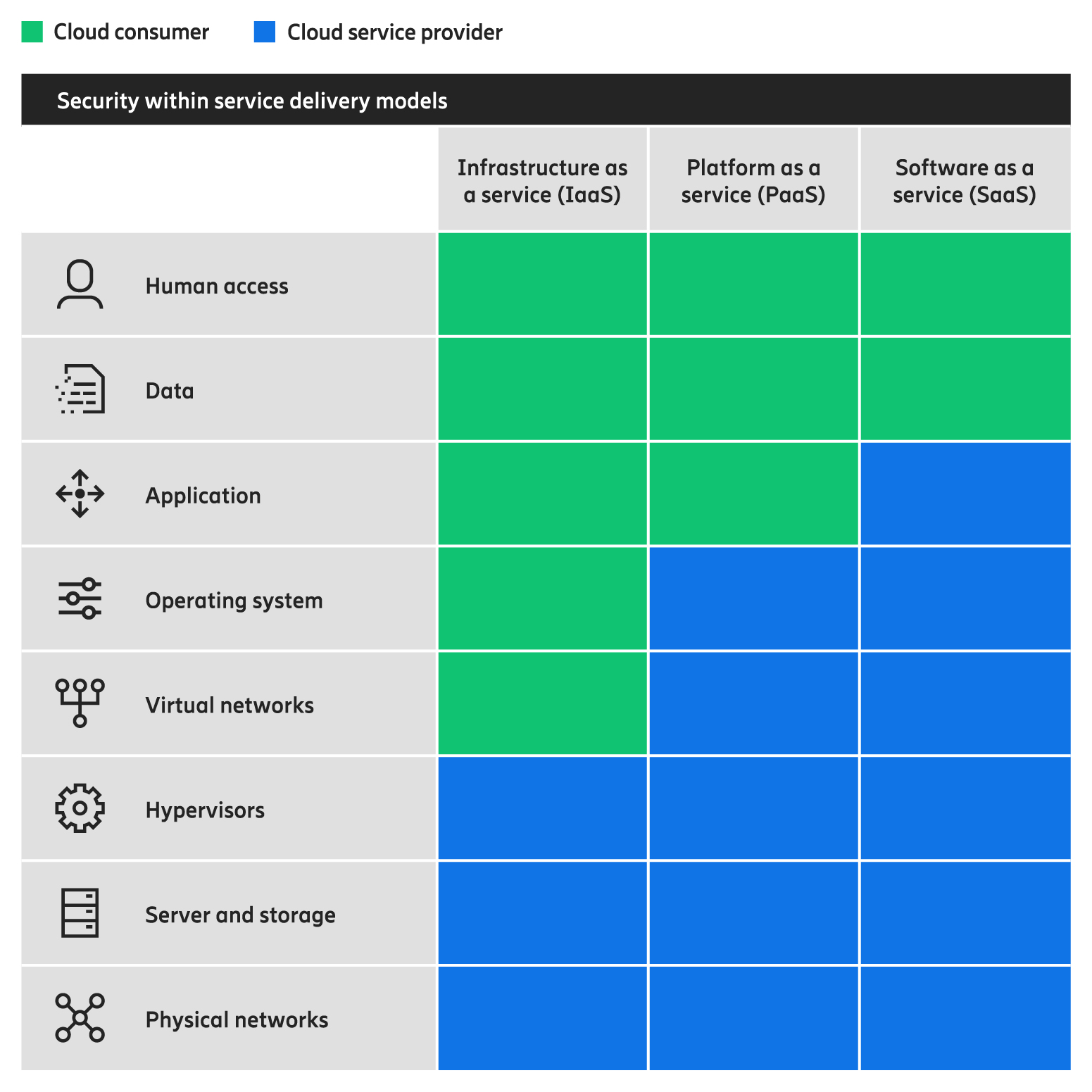
Cloud shared responsibility model
Let’s talk about solutions for strong security using Cloud RAN!
Now that we have walked you through the biggest security challenges in Open RAN, it is time to talk about solutions.
Embrace zero trust architecture
Zero trust architecture (ZTA) approach should be applied vertically in the cloud stack and horizontally between the network elements with three main characteristics:
- to make the protect surface perimeter-less or narrowed to micro-perimeters, rather than relying upon traditional perimeter defenses that protect against only external threats
- to set the policy of no implicit trust granted to an asset based upon ownership, physical location, or network location
- and to assume that the adversary is already inside the network when doing the risk analysis
Each layer of the cloud stack must be protected from external and internal threats and actors who might compromise the confidentiality, integrity, and availability of data and networking functions. An effective ZTA builds upon continuous monitoring, logging, and alerting at all layers of the cloud stack.
Ericsson Cloud RAN security solution is built upon a zero trust approach to enable mobile network operators to mitigate external and internal threats. The Cloud RAN solution will include functionality for protecting the data on all internal and external interfaces and support for establishing trust via mutual authentication.
Use Security by design or DevSecOps
Attackers may compromise a trusted manufacturer’s software, hardware, or established open-source libraries. That’s why achieving products with a strong network security posture, both security functions and embedded secure processes in product development, is a must.
To mitigate threats against the supply chain, Ericsson practices security by design supported by the Security Reliability Model (SRM). The SRM framework includes the management of open-source software. It starts with selecting third-party sub-suppliers and open-source software forums. SRM stipulates requirements in the sourcing and inbound supply stage to ensure that third-party products and sources are properly scrutinized prior to integration.
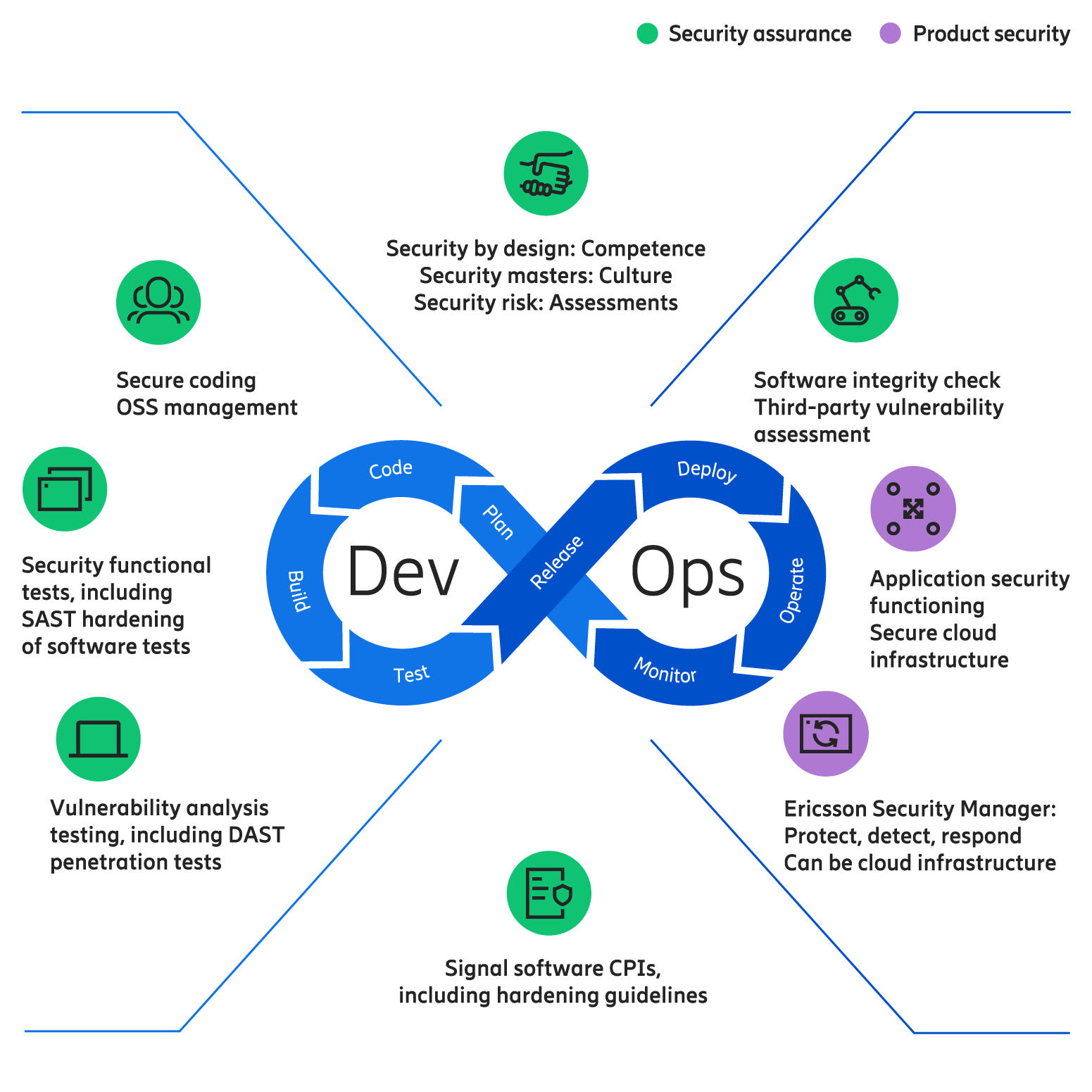
Ericsson DevSecOps practices for a strong security posture
Deploy a secure solution
Industry best practices for cyber hygiene, such as security configuration validation and software updates for critical vulnerabilities, should be components of a strong security posture in the cloud.
With the prerequisite that the security functions are in place, another key to secure deployments is to use and maintain a consistent and secure configuration.
Ericsson Cloud RAN pods are delivered with a secure-by-default configuration and tested on a hardened infrastructure. Cloud RAN will support security automation and intelligence through the Ericsson Security Manager (ESM) and the Ericsson Intelligent Automation Platform (EIAP), a service management and orchestration platform capable of hosting security-specific rApps.
Why should mobile network operators choose Ericsson Cloud RAN Security solution?
Here are the facts that speak for themselves.
Ericsson builds Cloud RAN Security solution and security assurance processes based on experience from purpose-built RAN deployments of scale and collaboration with the leading IT infrastructure vendors.
Our Cloud RAN products are developed according to industry best security practices. DevSecOps is embedded in the Ericsson generic design process in the holistic framework Security Reliability Model (SRM) for Cloud RAN and all other products. The security culture among the people at Ericsson is supported by our Security Master Model, which ensures security competence in all teams, from design to deployment and support.
We are a key contributor to 3GPP SA3 and O-RAN Alliance WG11 security specifications. Ericsson’s Cloud RAN offering has passed the independent Network Equipment Security Assurance Scheme (NESAS) audit, making it fully compliant with the security requirements defined by global standards organizations 3GPP and GSMA.
The Cloud RAN solution has security built-in to provide a strong security posture, as in Ericsson’s purpose-built RAN and Transport portfolio. This is important since Cloud RAN and traditional RAN may be deployed in parallel by mobile network operators in so-called blue field deployments. The goal for securing RAN, whether Cloud RAN or purpose-built RAN, is to protect the availability and high performance of the network and communication services while also ensuring confidentiality, integrity, and availability.
Achieving these goals in Cloud RAN requires a defense-in-depth approach in which security is enforced for all network communications and in each layer of the cloud stack keeping in mind dependencies between the layers.
Cloud-native networks anywhere and secure
Ericsson Cloud RAN enables service providers to seamlessly evolve towards cloud-native technologies and open network architectures and grab new business opportunities brought by Open RAN.
Our aim is to enable mobile network operators to deploy cloud-native networks virtually anywhere, on any cloud and server platform, and do it securely.
Read more
Telecom security for a connected world
Ericsson Cloud RAN. Virtually everywhere.
Download the paper - Evolving to a strong Cloud RAN security posture
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.
