Research on adversarial security modeling in RAN: User Behavior Analytics and Deception
Insiders pose significant security risks because of the initial foothold they have inside an organization’s network. They may have default access authorizations, such asvia valid authenticated and authorized accounts, to sensitive and protected resources. In this regard, insider threats can be substantially more detrimental than attacks that originate from outside of the organization’s network. Unfortunately, insider threats are also the hardest to detect, because traditionally they are trusted based on their location inside of the organization’s network and therefore, out of reach for classic perimeter-based security mechanisms. Detecting insider attacks requires first that insiders are monitored. In addition, analytics capabilities are also necessary to actively monitor user activity and detect behaviors that may be harmful to the target organization. Addressing the insider threat also contributes to the transition to the zero-trust principle in the network, through continuous monitoring and containment of threats inside a target network.
Current state of the art technologies provide a range of possible solutions to address the insider threat, where user behavior analytics (UBA) and cyber deception are two concrete examples. Both UBA and cyber deception provide the possibility to better understand attacker methods and tactics (attacker behaviors in general) and to address insider threats. In addition, they both can enhance a network’s detection capabilities. Taking that into consideration, we applied and evaluated the efficacy of UBA and honeypots (a deception technique) for Radio Access Network (RAN) in our research. More specifically, we have explored the possibility of running and operating UBA to detect risky and abnormal user behaviour in the management interface of a Radio Base Station (RBS). We have also explored how a honeypot – co-located with an RBS – could be used to quarantine a detected insider to further isolate and monitor the insider’s activity.
UBA in RAN
The zero-trust security model assumes that a breach is inevitable, and that a breach may already be occurring in the network. An attacker may already be in the network and may attempt to impersonate a management user or gain unauthorized access to network resources. Additionally, insiders can accidentally or intentionally cause breaches in the network. For instance, employees may have made a mistake that has caused a breach in the network, and disgruntled employees or malicious users might abuse their access rights to intentionally cause a breach. Therefore, it is essential to have proper monitoring solutions that continuously monitor and evaluate the users within the network to accurately identify suspicious or malicious behaviour, i.e. indicators of compromises.
One such solution is user behaviour analytics (UBA). UBA utilizes applied data analytics techniques, such as machine learning, to detect abnormal user behaviours. The purpose of UBA in the IT security realm is to detect and identify insider threats by creating behaviour profiles that characterize either (or both) malicious or normal users. In cases where UBA is used to characterize normal behaviour, behaviours that deviate from these baseline profiles are identified as anomalies (suspicious/abnormal behaviours) and thus, a potential indicator of compromise. In the case of characterizing malicious users, behaviours that are similar or match these malicious user profiles are considered anomalies. Ultimately, UBA enables the detection of insider threats that are otherwise hard or very costly to eradicate.
In our research, we have explored how UBA can be utilized in the context of RAN. More specifically, we mainly cover operations and maintenace (OAM) insiders – employees, disgruntled employees, and malicious users – in the management interface of a Radio Base Station (RBS). This entails that the UBA utilize the security and audit trail logs generated by the RBS as input to analyze the behaviors of the OAM insiders. Note that our research can also be extended in the future to include Cloud RAN. That said, the threat vectors the UBA address are the various valid and authorized OAM accounts used to manage and troubleshoot an RBS. An insider could utilize these accounts to cause damage to various resources and potentially move laterally in the network to attack other entities. For instance, an insider having access to an authorized and authenticated OAM account could leverage the violation of certain Command Line Interface (CLI) commands on an RBS to extract confidential information and disrupt UE traffic. In this regard, the UBA ingests the logs generated by the RBS in real-time to detect the malicious execution of commands at an early stage, as these specific execution formats are not considered normal behaviour in the management interface. Therefore, incorporating UBA could be highly beneficial as it could enhance the overall security of a RAN and can be an enabler for continuous monitoring and evaluation of users.
Honeypots in RAN
Honeypot systems have been extensively studied and used to complement the current IT security arsenal. Honeypots are essentially decoys that can, for example, mimic an OS, a system, or an application, and are exposed as vulnerable entities to entice attackers into compromising the system. In addition, they are equipped with extensive monitoring capabilities to track adversarial activities in the honeypot. Within the honeypots, there may be bogus data and services planted to deceive the attackers. Honeypots offer the capacity to lure attackers and divert them away from valuable assets to be protected. When carefully designed and deployed at key vantage points, honeypot systems provide early warning support and enable the collection and processing of targeted threat intelligence data. Despite their key promises, there have been only a few applications involving the use of honeypots in the context of RAN.
In our research, a honeypot that mimics the management interface of an RBS node was prototyped. The honeypot looks identical to the genuine CLI in the management interface and also consists of fake CLI commands that mimic the functionality of the commands in the genuine CLI. As this honeypot provides a fake interactive environment, it allows an attacker to interact, for instance by executing commands and traversing directories. The honeypot also has extensive monitoring capabilities which allows for close monitoring of the activity in the honeypot. Doing so helps to identify and understand the techniques and methods used by the attackers and what their intentions are. In this regard, the honeypot can be a fully isolated environment that is collocated with the genuine RAN environment; thus, providing the possibility to use the honeypot as a response action for suspicious users on the genuine RBS.
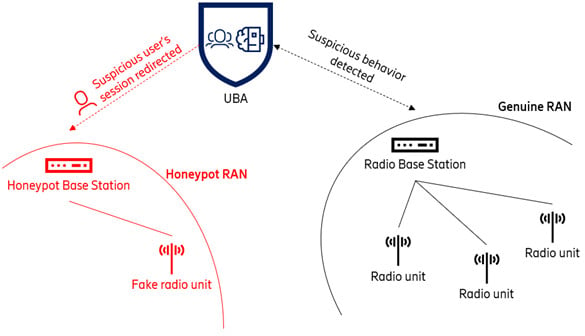
Figure 1. UBA redirecting a suspicious user's session to the honeypot transparently
This entails that the UBA could potentially operate in harmony with the honeypot (as depicted in Figure 1), where the UBA functions as a detection control – detecting suspicious users on the genuine RBS and transparently redirecting the sessions to the honeypot RBS – and the honeypot functions as a response action which contains and isolates the suspicious users that were detected by the UBA. More specifically, when UBA detects abnormal and suspicious user behaviors, response actions should be taken accordingly. If a suspicious user is detected, then a policy can be applied to lock the user’s account and terminate the active session. However, this would mean that we cannot monitor and evaluate the suspicious user further and thus we lose the possibility to gain adversarial behavior insights, such as what kind of attack techniques and methodologies the user utilizes to attack a resource and what motives the attacker has. Therefore, an alternative response could be to redirect the user’s session transparently to a fully isolated and controlled environment to further study their behavior. A UBA solution coupled with our honeypot could achieve just that. By redirecting a suspicious user detected by the UBA transparently to the honeypot, it allows continued monitoring and evaluating the user and thus study the various techniques, methodologies, and motives the user has. It is essential that the redirection mechanism is transparent, meaning the suspicious user is oblivious of the redirection and continues to interact with the honeypot while believing it is still the genuine RAN environment. As a result, we could potentially witness attacks or certain techniques that have never been seen before in mobile networks, such as zero-day attacks.
More opportunities for security in RAN
Both state-of-the-art solutions, UBA and honeypots, achieve detection and containment of an ongoing threat, as well as acting as enablers to adopt other security models and develop different capabilities in telecom networks today. A couple of the opportunities in RAN related to security architecture and capabilities are the Zero Trust Architecture and threat intelligence for mobile networks.
Zero Trust Architecture
In the Zero Trust Architecture publication published by National Institute of Standards and Technology (NIST), the basic principle of a zero trust security model states that assets or subjects are not inherently trusted. Access to resources by other resources or subjects should be either granted or denied by an adaptive policy that is dependent on the contextual attributes and measurements and the behavior of the requesting resource or subject. Moreover, in a Zero Trust Architecture, the security posture of subjects and resources should be continuously monitored and evaluated, and based on the output of the evaluation, informed decisions should be made and policies should be enforced accordingly.
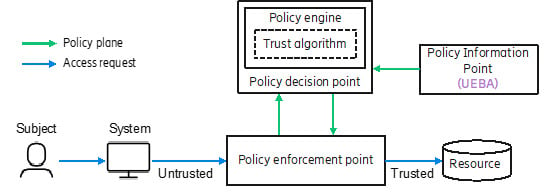
Figure 2. UEBA as an example of PIP in ZTA
In the context of ZTA, UBA could potentially be used as a Policy Information Point (PIP), meaning the UBA supplies the Policy Decision Point (PDP) with additional context information regarding the subject’s request to aid the PDP in the decision process of granting the subject access to a resource (see Figure 2). For instance, the UBA could provide attributes or measurements to the PDP as input for trust evaluation, where the trust score is evaluated by a trust algorithm in the PDP resulting in a decision to whether grant the subject access to a resource or to deny access to a resource.
Behavior analytics are not only limited to user activity but can also include entity behaviors. In this regard, User and Entity Behavior Analytics (UEBA) not only monitor and evaluate user behaviors, but also non-person entity behaviors (e.g. network functions, interfaces, and UEs). Thus, UEBA is beneficial to apply in telecom networks, especially after the transformation to cloud-based architectures, as it can facilitate detecting compromised network functions, and thus, potentially prevent further lateral movements in the network.
Threat intelligence for mobile networks
Attackers are versatile, meaning their attack techniques and behaviors can change drastically over time. Therefore, a lack of insight and understanding of what techniques and methodologies the attackers use to achieve their objectives can result in a limited view of the threat landscape in mobile networks. Having a limited view of the threat landscape entails that a mobile network is less prepared for the threats out in the wild, meaning security mitigation and detection controls are not adapted to the ever-changing threats. In this regard, UBA and honeypots could be enablers for creating a threat intelligence framework for mobile networks, in which insights and understandings of attacker techniques, methodologies, and intents, specifically for mobile networks, can be collected. Consequently, the framework can be used to implement robust security mitigation controls and to enhance current controls accordingly.
Summary
Behavior analysis of subjects and resources and deception are two security concepts that can be used as adversarial modelling techniques. Within Ericsson, we will continue to research and evaluate further different adversarial modelling techniques and their efficiency in RAN.
Finally, we would like to thank our colleagues, Prajwol Kumar Nakarmi, Jonathan Olsson, Henrik Forssell, Antti Jaakkola, and Luca Margone, for their invaluable feedback and contribution.
Learn more
Read more about Telecom Security in high-performance networks
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.