Our Security Reliability Model
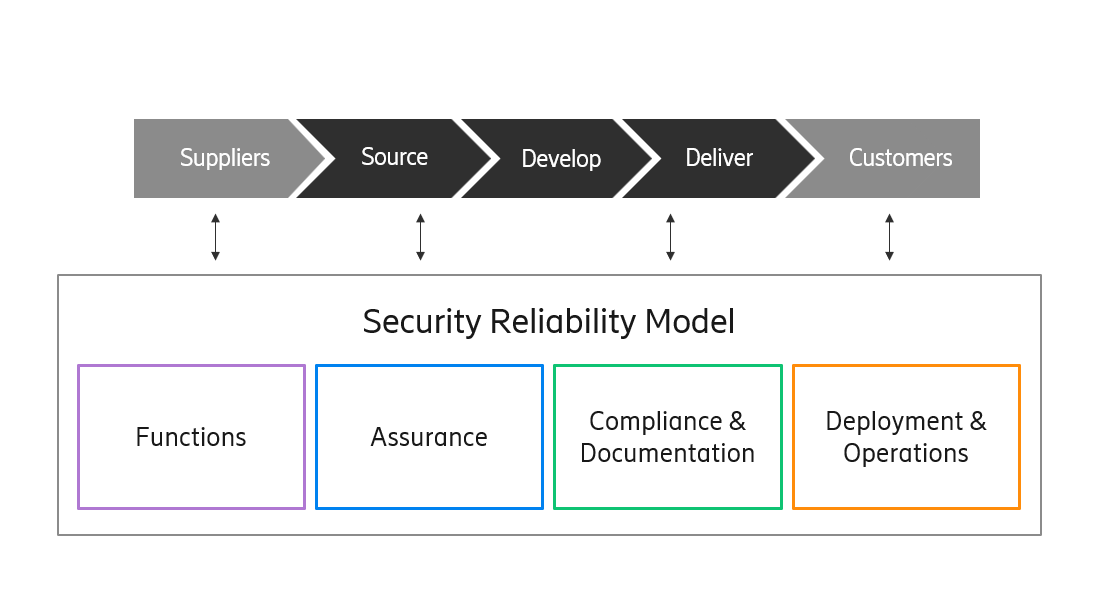
Ericsson has a long history of systematically incorporating security and privacy considerations into all relevant aspects and phases of our product value flow. Our efforts in this area follow a well-established internal control framework known as the Security Reliability Model (SRM). The SRM enables a managed, risk-based approach to security and privacy implementation where requirements are tailored to the target environment and demands. This approach helps us meet stakeholders' expectations and cater for the rapid evolution of technology and the continuous changes in legislation globally.
The SRM defines Ericsson’s approach to achieving our product security and privacy by design ambitions. Its purpose is to:
- set the product security and privacy ambition levels for our products and solutions
- specify the control framework that will enable Ericsson to fulfil the ambition levels
- outline how this control framework covers the product value flow, from the sourcing of components throughout the development activities to deployment and operations in customer networks
- demonstrate how we achieve compliance with relevant laws and regulations
The SRM divides security and privacy controls into four key areas: (1) Functions, (2) Assurance, (3) Compliance & Documentation and (4) Deployment & Operations. We apply the controls in these four areas continuously through well-defined activities across our product value flow, all the way from our suppliers to our customers.
To read all about the Ericsson’s Security Reliability Model
SRM area : Overview
SRM area 1: Functions
The SRM mandates that each product organization shall analyze, decide and document the applicability and compliance to our Generic Product Requirements (GPRs) for security and privacy. To assist them in this work, it also defines a set of generic security and privacy functions for Ericsson products. Risk assessment and privacy impact assessment processes are used to identify and prioritize the applicable security and privacy functions from the set of GPRs.
SRM area 2: Assurance
Assurance refers to the activities conducted to ensure that the final product is secure when it is running in its target environment. They include risk assessments, privacy impact assessments, secure coding, vulnerability analysis and hardening. The SRM specifies the relevant assurance activities for each category in every phase of the product value flow: Source, Develop and Deliver. Depending on the characteristics of the product, the appropriate level of assurance activities – basic, advanced or tailored – is set for each category.
SRM area 3: Compliance & Documentation
The Compliance & Documentation area covers all the information that demonstrates the security and privacy status at product release and in the customer documentation. It also defines applicable certificates and statements of conformance for external stakeholders, as well as providing necessary guidelines to maintain security and privacy in customer environments. Customer Product Information, security test reports and security standard conformance all play a key role in this area.
SRM area 4: Deployment & Operations
The Deployment & Operations area groups together the operational aspects of product security that arise in the product value flow, including security in system integration, guidance that operators require to operate their network in a secure way and customer support to resolve any incidents that arise.
Ericsson’s Security Reliability Model ensures that product security and privacy gaps are identified as early as possible – ideally during the conception phase of a new feature, product, service and solution. This allows us to control the direction of product development towards secure implementation. Considering relevant security and privacy requirements during the product design phase enables a secure implementation.
By ensuring that deployed products are free from unacceptable risks, we can avoid many potential security and privacy incidents. The security and privacy assurance is documented and the outcome is known and is used for improvements in subsequent releases, as part of the product roadmap. Vulnerabilities are managed through the lifecycle of the product.
Our comprehensive approach to addressing the security and privacy aspects of our products enables our customers to operate them securely and in compliance with relevant privacy laws and regulations.




