Fighting IMSI catchers: A look at 5G cellular paging privacy
In one of our earlier blog posts, we wrote about protecting 5G against IMSI catchers, which is a significant privacy enhancement introduced for the 5G standard in the UPLINK direction. Long story short, the long-term identifier in 5G, called SUPI, can be privacy protected over-the-air in the UPLINK by using a concealed identifier instead, called SUCI, which is freshly generated each time using asymmetric cryptography.
In this blog post, we introduce the 5G standard's DOWNLINK privacy enhancements, specifically in the 5G cellular paging protocols.
Paging procedure in 5G
In a mobile network, when a device does not have any ongoing data transmissions, it enters an IDLE state in order to preserve battery. If new data arrives for the device, the network probes the IDLE device by sending a so-called "paging" message and the device correspondingly responds.

This procedure, which is aptly called the paging procedure, works because even while in the IDLE state, the device keeps monitoring for the paging message at certain device-specific times. The device is able to preserve battery because, at other times, it may apply what is called "discontinuous reception" or DRX, meaning that it can switch off its receiver.
The paging procedure is controlled by a core network and exists in all generations of mobile networks (2G, 3G, 4G, and 5G). One of new things in 5G is that this paging procedure can also be controlled by a radio access network to some extent for devices in a special state, called the INACTIVE state.
Privacy enhancements in 5G paging procedure
3GPP adeptly capitalized on a golden opportunity of 5G standardization to introduce several privacy enhancements to the paging procedure compared to the earlier generations - 4G, 3G, and 2G. This is a result of admirable collaborative work between multiple working groups in 3GPP, mainly the ones responsible for security (SA3), system architecture (SA2), and radio interface protocols (RAN2).
Let's briefly take a look at those enhancements.
1. Paging timings

The device-specific times, at which the device switches on its receiver and checks for a paging message, are determined by what are called Paging Frame (PF) and Paging Occasion (PO). The PF is a radio frame which may contain one or multiple POs for a set of devices. The PO is the specific time instant where the network can transmit the paging message for a subset of devices corresponding to the same PF. In the example in the figure above, the PF occurs in frame 47 and the POs occur in subframes 4 and 9.
One privacy enhancement in 5G paging procedure comes from a change in how these PF and PO are determined.

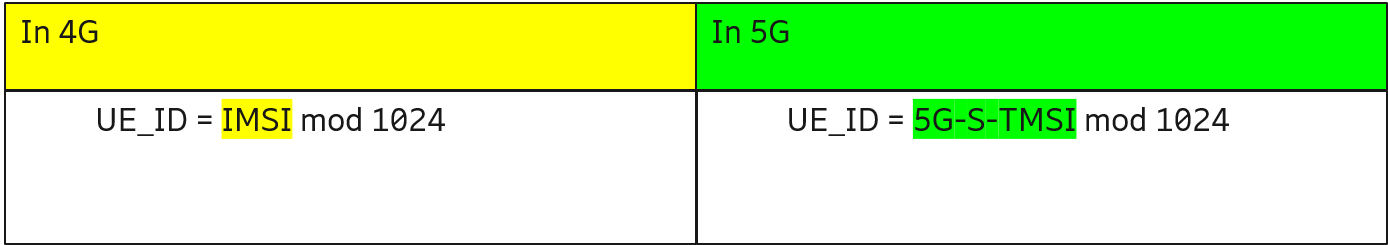
While in 4G paging timing was determined based on a long-term identifier (called IMSI), now in 5G they are determined based on a temporary identifier (called 5G-S-TMSI). More specifically, the PF and PO are determined based on a short 10-bit device identifier called UE_ID which, in turn, is calculated as below:
We had proposed the above change in 3GPP RAN2 which was then adopted. The effect of this change is that it becomes infeasible for an over-the-air attacker to deduce information about a device's long-term identifier by monitoring the air interface and detecting which paging occasions the device is monitoring. Therefore, this results in enhanced privacy.
2. Paging identifier
The above might raise a few questions. Since the device identifier UE_ID mentioned above is only 10 bits long and there can easily be many thousands of devices in any given area, won't multiple devices likely have the same device-specific times i.e. the same PF and PO? In which case, how can devices know if a paging message is intended for their specific device?
These are very valid questions. The answer is - when paging occurs, an identifier of the paged device, called paging identifier, is carried in the paging message. Thus, only the device whose identifier matches the paging identifier will respond to the network.
Another privacy enhancement in 5G paging procedure comes from a change in "what" this paging identifier is.

While in 4G, the paging identifier could be either a long-term or a temporary identifier, on 5G networks, it can only be a temporary identifier. To illustrate how this can look, the paging identifiers are as shown below:
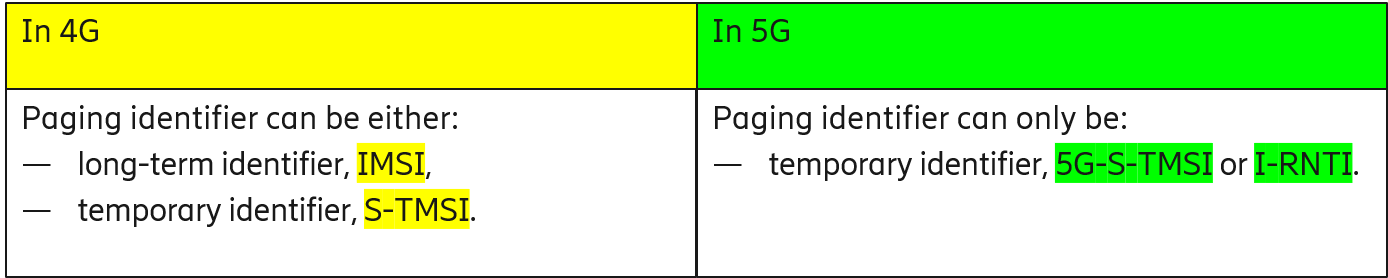
Long-term identifiers (called IMSI) were historically supported as paging identifiers in earlier generations for what is known as restoration procedures i.e. to support an event of loss or corruption of device context information (including temporary identifier) in the core network entities. Now in 5G which natively supports virtualization and cloud-based implementations of the network, it is more practical to assume geographically redundant availability of the core network and also a fail-safe storage of the device context information (including temporary identifier). Thus, the support for a long-term identifier (called SUPI in 5G) as a paging identifier can safely be dropped.
In 3GPP SA2, we proposed to remove SUPI based paging which was eventually adopted. The effect of this change is that even if an attacker would have succeeded (in an imaginary situation) in prompting the network to reveal the device's long-term identifier, such an attack would still not work in 5G because there is no SUPI based paging to start with. Therefore, resulting in enhanced privacy.
So far so good.
3. Temporary identifier
At this point, a few doubts may be raised. For example, if the temporary identifier used as paging identifier is not refreshed regularly, won't it then practically become yet another long-term identifier? In which case, won't the above privacy enhancements fall apart?
Another valid point, and another privacy enhancement introduced in 5G paging procedure is exactly about this aspect. More specifically, this determines how often the temporary identifiers (and ultimately the paging identifiers) are refreshed.
Firstly, the I-RNTI is a temporary identifier used by a radio access network. Its use as the paging identifier is a new feature in 5G compared to 4G. And by design, this I-RNTI is made for one-time use i.e. it is compulsory to refresh the I-RNTI after every use.
Secondly, the 5G-S-TMSI is a temporary identifier used by a core network. And 5G enforces a stricter policy for refreshing this 5G-S-TMSI.

While in 4G, it is optional to refresh the temporary identifier - the S-TMSI - after paging, on 5G networks it becomes compulsory to refresh the 5G-S-TMSI. Furthermore, it is also compulsory to allocate new 5G-S-TMSI at initial registration and mobility registration update procedures – however, we will not go into details of these since we are focusing on paging procedure.
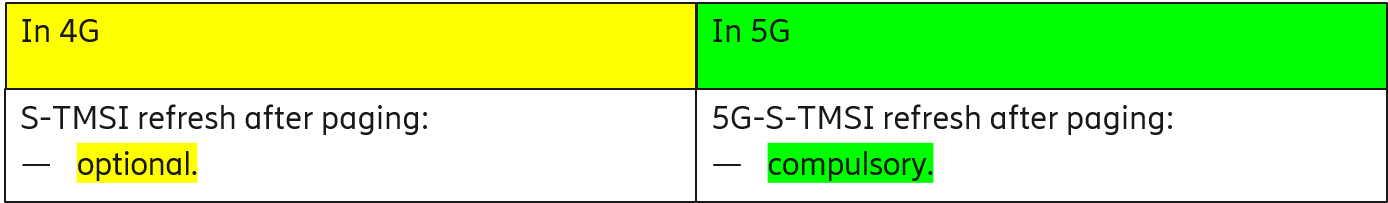
We had driven strictly refreshing temporary identifier in 3GPP SA3 which was approved. The effect of this change is that, not only the paging identifier (5G-S-TMSI) but also the above-mentioned paging timings (PF and PO) regularly get refreshed, making it impractical for an over-the-air attacker to use those values for identifying or tracking the device. Again, therefore, resulting in enhanced privacy.
Takeaway message: Carefully designed privacy enhancements make 5G networks more resistive than ever to IMSI catchers or Stingrays
We discussed that 3GPP decoupled long-term identifier from 5G paging procedure and introduced important privacy enhancements which are – (1) paging timings based on temporary identifier instead of long-term identifier, (2) removal of long-term paging identifier and use of only the temporary paging identifier, and (3) strictly refreshing temporary identifier.
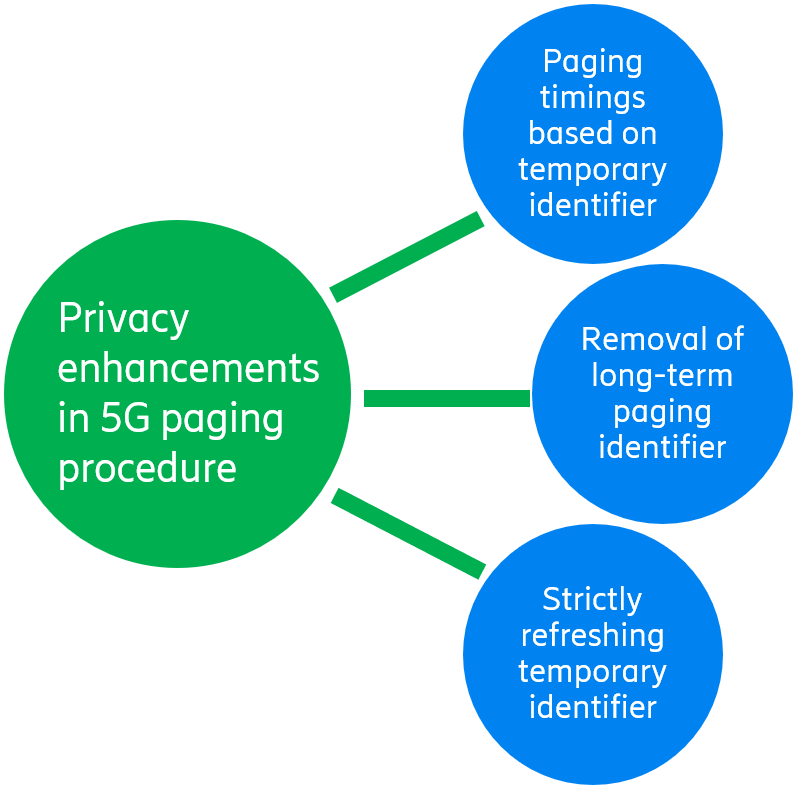
These enhancements are the perfect example of how we, at Ericsson Research, bring our experts from various areas (like RAN2, SA2, and SA3) to work together and design a holistic solution. We are grateful and proud of the hard work of our whole team, thanks to which, privacy attacks on cellular paging protocols are now infeasible on 5G networks – even for attackers with comprehensive knowledge of those protocols.
We also cannot go without accrediting many other companies who work hard in 3GPP and have significant contributions in terms of proposals, discussions, and feedback. 3GPP is a joint work of companies around the world.
For more details, tech savvy readers may indulge themselves in the following 3GPP technical specifications – 23.501, 23.502, 38.300, 38.304, 38.331, and 33.501.
We bid adieu to you for now. Mind that privacy in mobile networks is a very important topic for Ericsson, and something which we will continue to drive in standardization.
Read more
Explore the fundamentals of modern network architecture and how it is driving a new era of agile, cloud-native network operations.
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.