Authentication and key agreement cheat sheets for 2G, 3G, 4G and 5G
3GPP has developed more than 10 releases of technical specifications for the four generations of mobile networks, 2G to 5G, which span three decades. With each release, and especially with each new generation of mobile networks, additional features and enhancements have been introduced to address contemporary needs and to enable novel use cases.
Security is one of the topics in which substantial improvements have been made from 2G to 5G. Today, 5G is the most secure and trustworthy mobile network, for example, in terms of user privacy and data protection. The foundation of security in mobile networks lies in cryptography, particularly two fundamental processes: authentication and key agreement.
Authentication and Key Agreement (AKA)
Authentication is a security process to get a cryptographic assertion that the mobile phone and the network are the entities they are claiming to be. The network cryptographically authenticates a mobile phone so it can be certain that the services are being provided to the legitimate users, the users cannot deny their bill, and one user cannot impersonate another user. Similarly, the mobile phone authenticates the network so that an unauthorized party (such as an IMSI catcher, which is a malicious device trying to impersonate a legitimate base station) cannot successfully engage with it.
Key Agreement is another security process that enables the mobile phone and the network to establish one or more shared security keys for the cryptographic protection of traffic sessions, mainly encryption and integrity protection. With these protections in place, it is infeasible for unauthorized users to read the original message or tamper with the original message without the receiving side detecting the tampering.
AKA: In 3GPP, the combination of these two processes is called Authentication and Key Agreement, AKA.
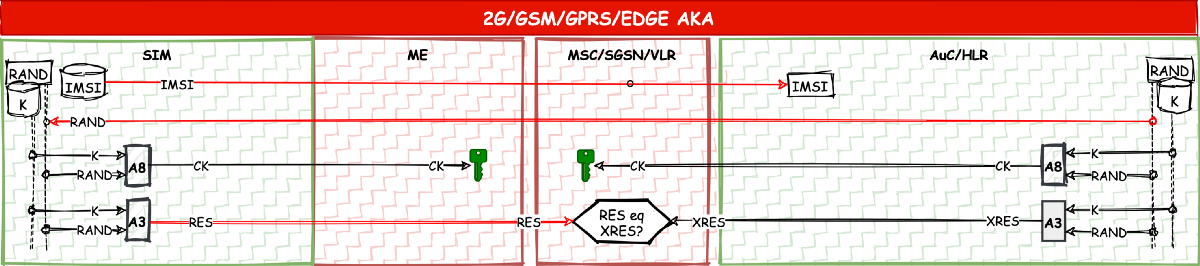
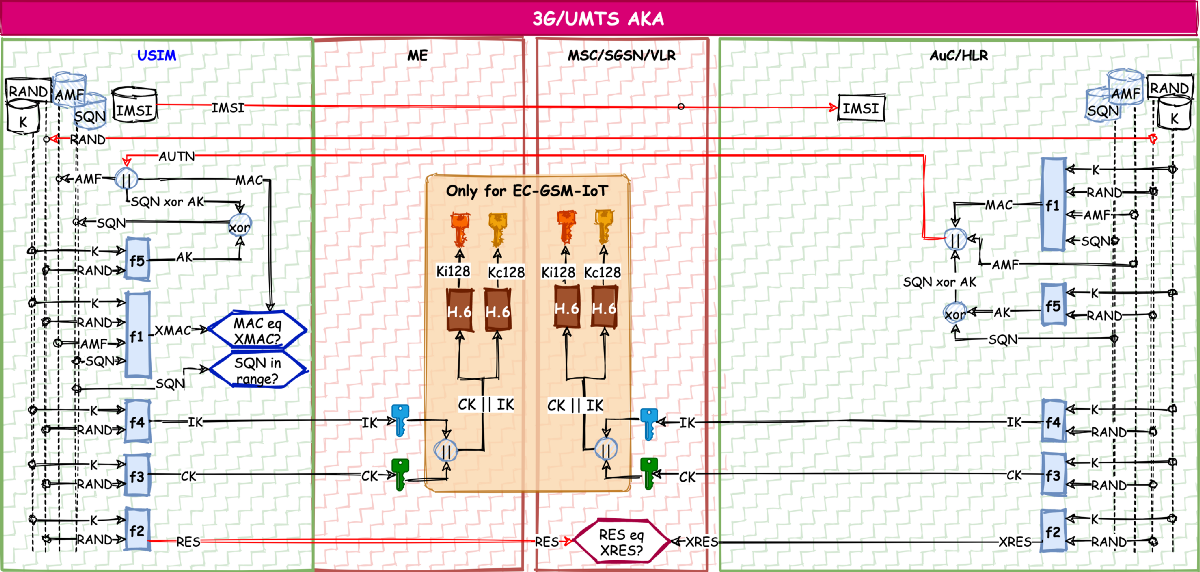
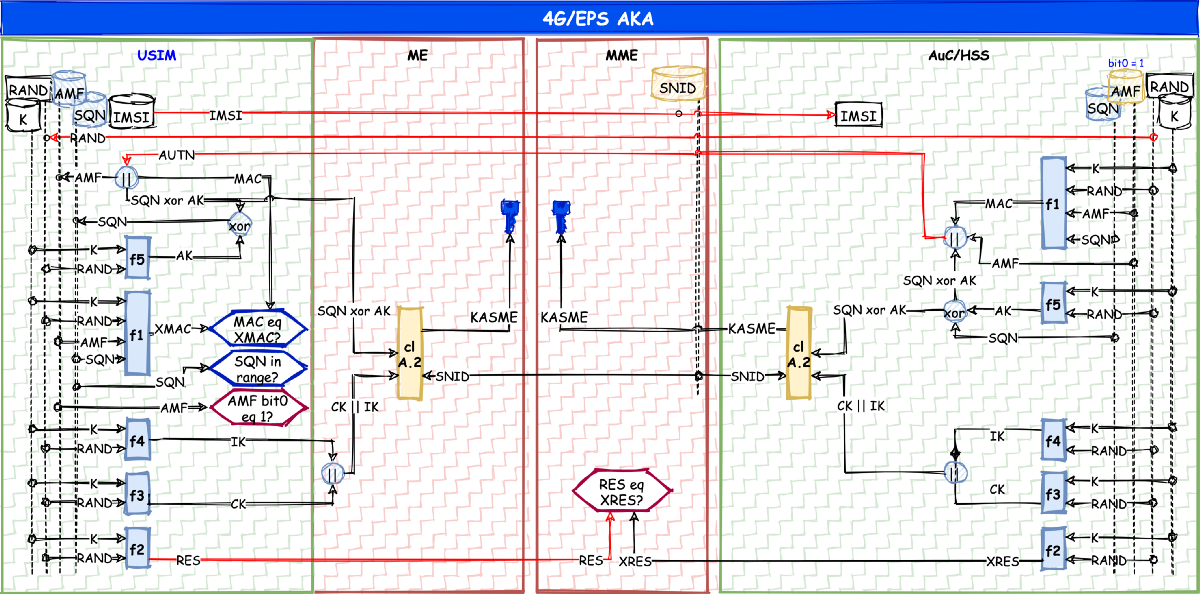
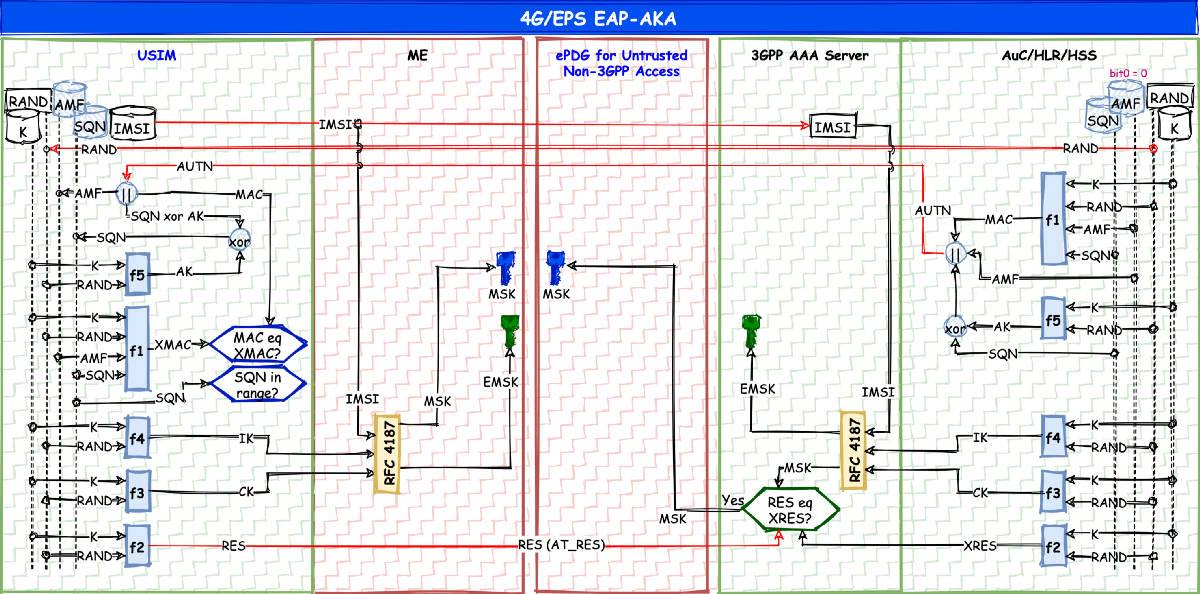
3GPP has always revised AKA and made improvements when developing a new generation. An example of this on the authentication side is that while only the network authenticated the mobile phone in 2G (one-sided authentication), it was the mobile phone that authenticated the network as well in later generations (mutual authentication). A similar example of the key agreement improvements is that while only an encryption key was setup in 2G, an additional key for integrity protection was also set up in later generations.
There are eight main versions of AKA in 3GPP from 2G to 5G. What is common to them is that they are in a form of ‘challenge-response’ protocol in which the network provides a cryptographic challenge, and the mobile phone provides a cryptographic response.
In addition, all AKAs are based on ‘symmetric cryptography’ with a root, pre-shared symmetric key (K) shared between the network and the SIM card. From this root K, security keys for protection of traffic sessions are derived and used between the mobile phone and the network.
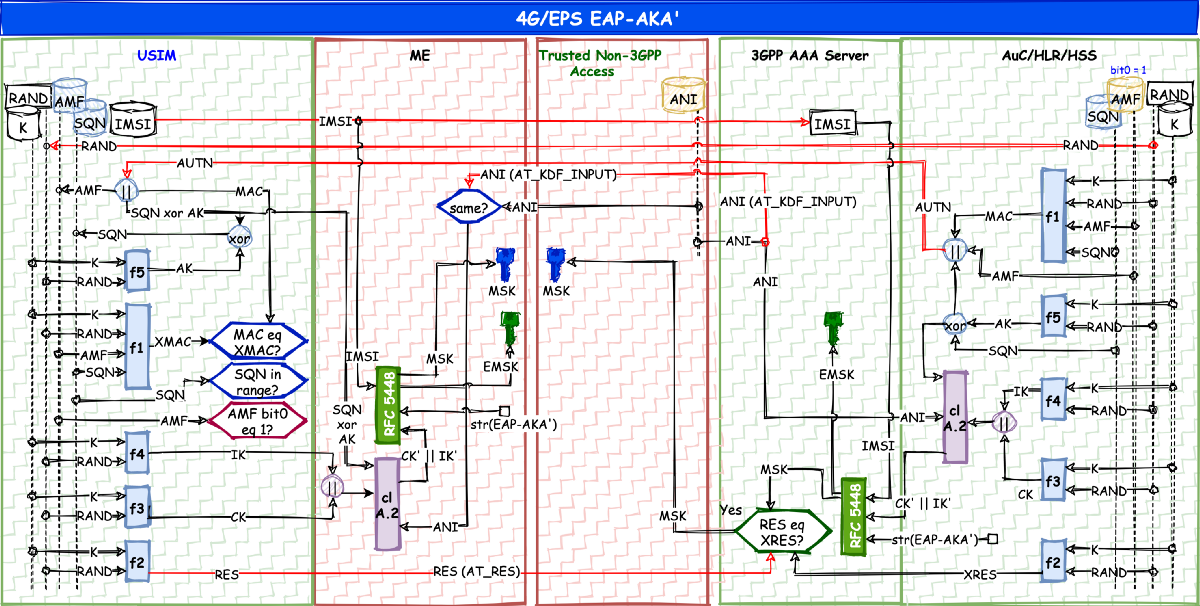
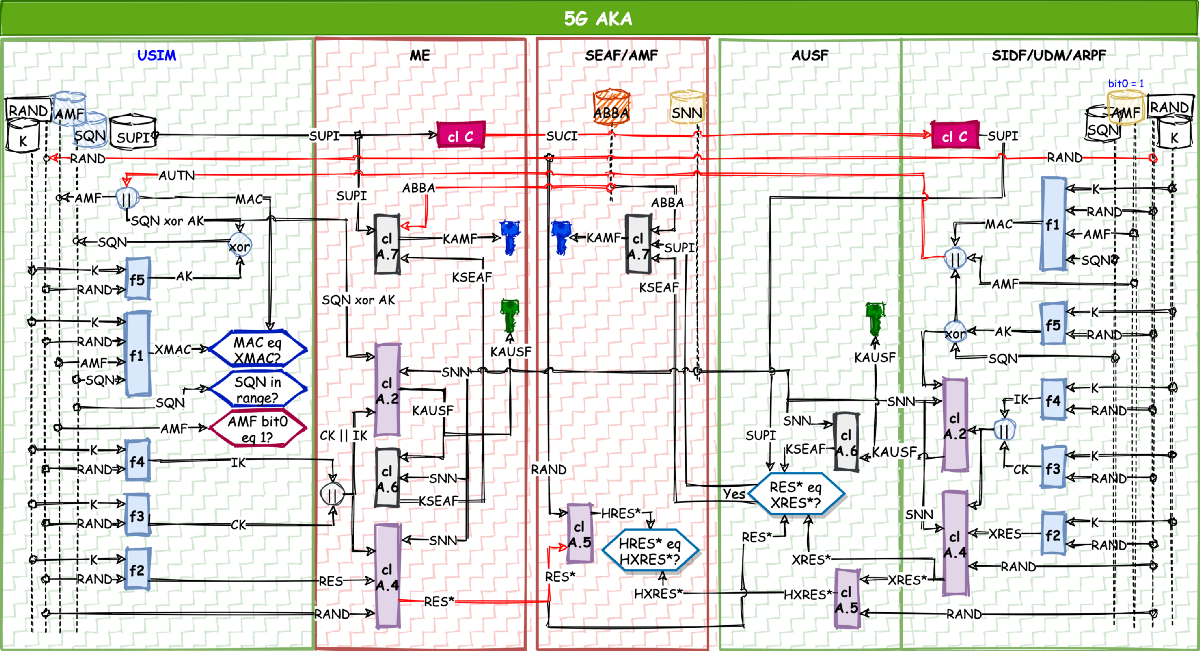
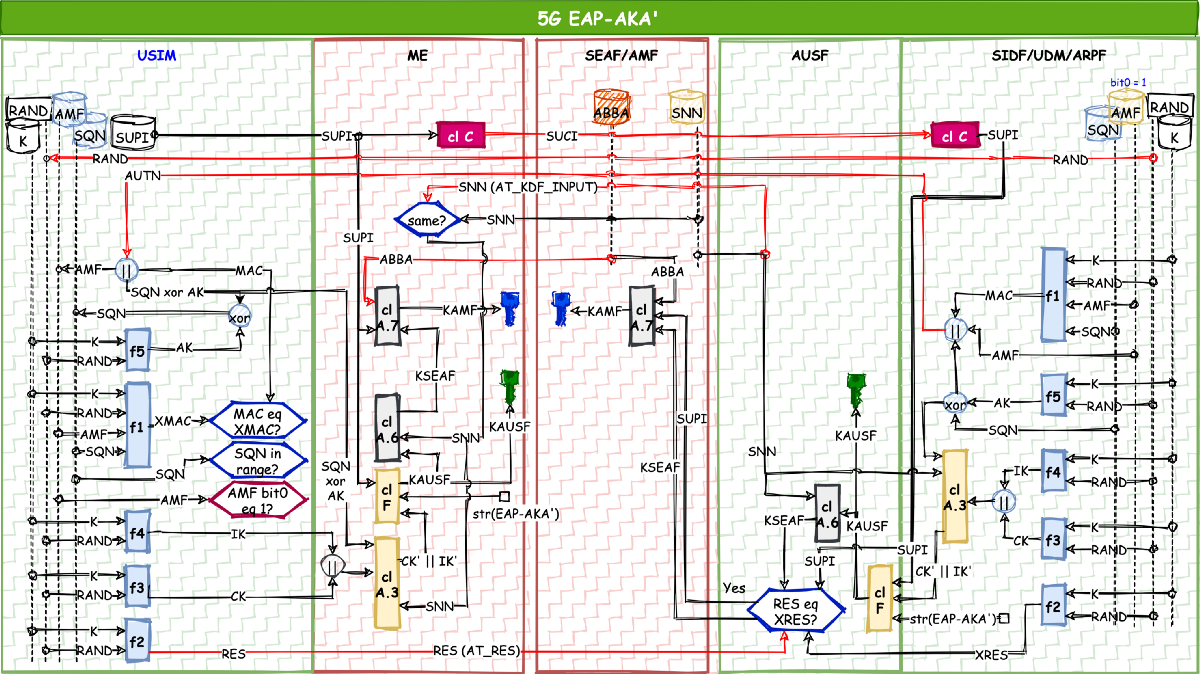
AKA cheat sheets
Without any further delay, let me share with you the cheats sheets that I prepared for my own convenience. I’m keeping this blog post short by not explaining the acronyms used in the cheat sheets. For those, my tutorial paper at arXiv is available.
Last words
In the tutorial paper, I have listed the main properties in each AKA. If I was to summarize by picking one major feature of AKA in each generation, they would be as follows:
2G had only one-sided authentication in which the mobile phone was authenticated by the network. But the mobile phone did not have the means to authenticate the network, which made it easier for IMSI catchers to trick the mobile phones.
This was fixed in 3G by introducing mutual authentication between the mobile phone and the home network. Still, it was possible that session keys generated for one roaming network were valid for another roaming network, meaning there was no cryptographic separation of security keys between roaming networks.
In 4G, this was fixed by cryptographically binding the roaming network identifier with session keys. However, the authentication still terminated in the roaming network, which informs the home network that a certain mobile phone is in its network. The home network had no means of guaranteeing if the mobile phone was really present in that roaming network.
To fix this, authentication in 5G is terminated in the home network.
In conclusion, the various revisions of AKA definitely showcase how well 3GPP has addressed known and future threats to provide a solid foundation of secure mobile networks. So far, so good. And if there are any more enhancements to come in 6G,
I’ll be on it.
If you find any corrections to be made in the cheat sheets, do let me know. Thank you.
Learn more
Explore these earlier blog posts and articles
A summary of 3GPP Release 16, 5G phase 2: Security and RAN
3GPP Release 15: An end to the battle against false base stations?
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.