Migration to quantum-resistant algorithms in mobile networks
Risk of cryptographically relevant quantum computers and actions taken
A cryptographic algorithm is quantum-resistant (QR) if it is not feasible to break even with a large and robust cryptographically relevant quantum computer (CRQC). A CRQC is a quantum computer that can break algorithms currently used for public-key encryption, key exchange, and digital signatures such as RSA and elliptic curve cryptography. Such a quantum computer needs to be much larger and much more robust than current quantum computers.
Quantum-resistant cryptography is also known as post-quantum cryptography but will be deployed and used long before any CRQC is built. It is still uncertain when, or even if, CRQCs will ever be built, but the formidable threat of CRQCs and the slow pace at which we can introduce new algorithms means that we must act on the risk and plan for migration – particularly in mobile networks that serve billions of users.
The work on making ICT systems quantum-resistant is quickly moving from research to standards, implementation, and deployment. After a multi-year effort with participation of hundreds of researchers from all over the world, the US National Institute of Standards and Technology (NIST) announced in 2022 that they intend to standardize the key encapsulation mechanism Kyber and the three signature algorithms Dilithium, Falcon, and SPHINCS+. Kyber and Dilithium are the primary chosen quantum-resistant algorithms and can be used instead of the currently used public-key algorithms like RSA and elliptic curve cryptography.
Standards and implementation overview
The selected algorithms have been chosen in open competition just like the previous NIST algorithms AES and SHA-3. NIST plan to release draft standards for public comment in 2023 and hope to publish the final standards by 2024. They expect to make several changes in the final standards. NIST will prioritize the two primary algorithms Kyber and Dilithium.
NIST’s algorithm usage is implemented primarily through its incorporation in Internet Engineering Task Force (IETF) protocols, and only few ICT systems implement them directly. IETF has been following NIST’s work closely and is preparing to include the NIST standardized QR algorithms in all important security protocols.
3GPP has been actively following the ongoing standardization in NIST and IETF and will introduce QR algorithms in 5G as soon as the final NIST algorithm and IETF security protocol standards have been published. 3GPP has some of the best and most secure profiles for security protocols, like TLS and IPsec. 3GPP profiles are updated at every release based on IETF standardization work, government requirements, and academic research to ensure that they remain state-of-the-art. QR algorithms will likely be introduced as part of 3GPP Release 19 or 20. This will make 6G – which is expected from Release 21 – fully quantum-resistant from the start.
Adoption of the new algorithms – US
Based on the NIST announcement, the US National Security Agency has already announced the Commercial National Security Algorithm (CNSA) Suite 2.0. They have also announced the anticipated timelines for when US national security systems are expected to support CNSA 2.0 for protection of TOP SECRET information that often needs to stay confidential for up to a century.
CNSA 2.0 is a major update as it replaces RSA and elliptic curve cryptography with QR algorithms that offer protection against future deployments of CRQCs. CNSA 2.0 selects Kyber and Dilithium with ‘security level V’ as the general future public-key algorithms.
The CNSA 2.0 timelines are very demanding, see Figure 1.
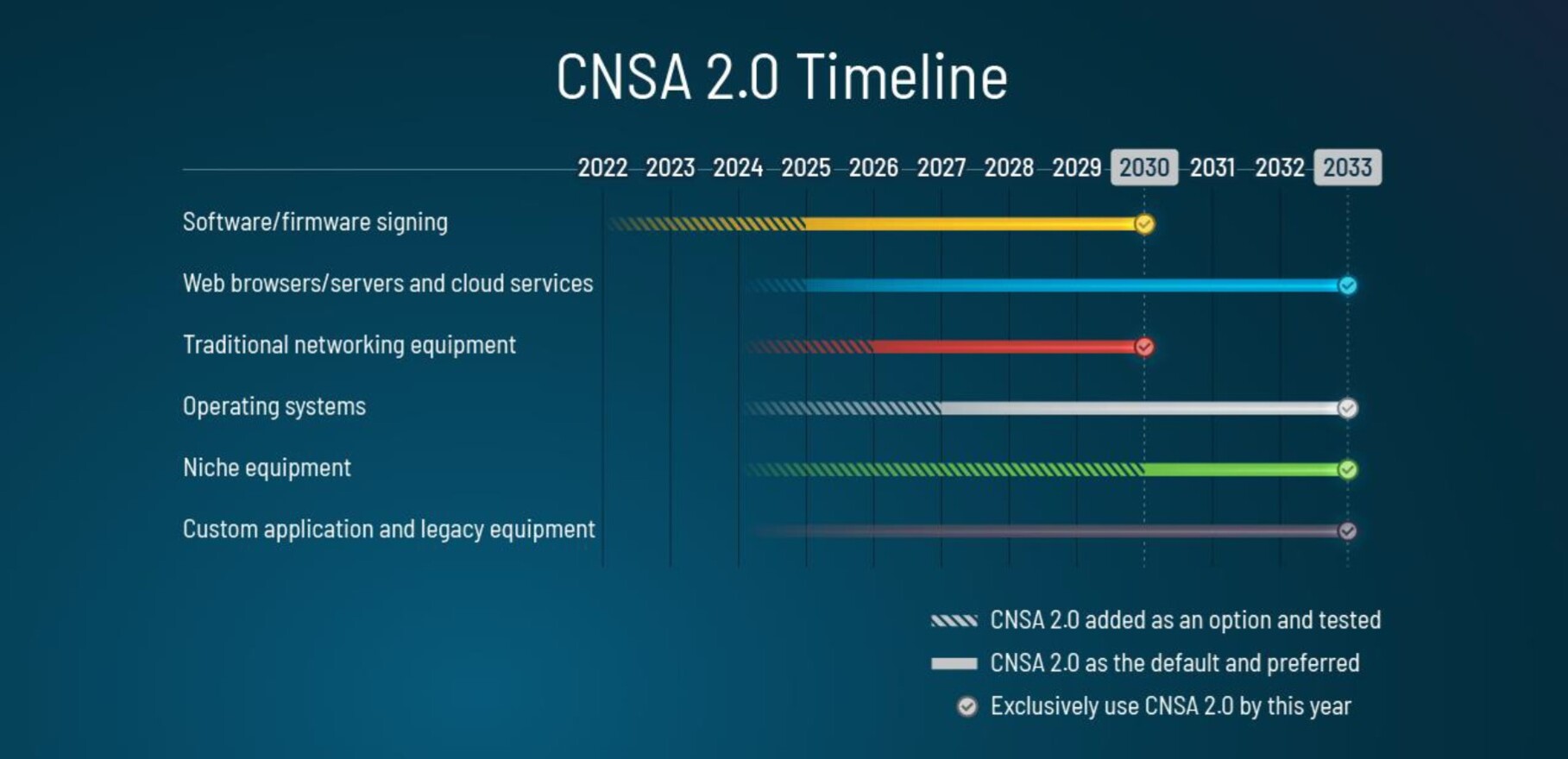
Figure 1. CNSA 2.0 timeline for US national security systems (Source: source: NSA Cybersecurity Advisory, Announcing the Commercial National Security Algorithm Suite 2.0).
Network equipment is required to support QR algorithms by 2026 and all equipment is required to support QR algorithms by 2030. Following that, RSA and elliptic curve cryptography are required to be phased out everywhere by 2033. The US National Security Agency stresses that non-standardized algorithms such as the current specifications of Kyber and Dilithium will not be allowed for production use.
Implications for mobile networks
Mobile networks are not national security systems, yet they are considered critical infrastructure that generate high economic and societal value, and with a clear need to be protected and secured against future attacks. Hence, there are strong arguments for bringing the new algorithms to mobile networks. But mobile network security builds on various standards and how these standards will adopt the QR algorithms. So, it is still unclear exactly when, in the end, mobile networks will use these algorithms. In addition, current QR algorithms are not stable, there are no algorithm standards, no protocol standards, and certainly no implementations of the final standards. The CNSA 2.0 timelines will be very hard to meet even for national security systems.
In previous decades, very few standardized cryptographic algorithms have been broken. Instead, attackers have used implementation aspects, such as implementation bugs, side-channel attacks, or faults in the use of algorithms in protocols. Implementations need to be hardened and, in some cases, certified before they are used. Using non-standardized algorithms and protocols, or non-hardened implementations would lower security rather than strengthen it.
Kyber, Dilithium, and Falcon: The new quantum-resistant algorithms in more detail
Kyber, Dilithium, and Falcon are all lattice-based algorithms where the security is based on well-known mathematical problems in 512-1024 dimensions. The lattice-based algorithms NIST will standardize are as fast or faster than the fastest elliptic curve algorithms but have much larger public key, encapsulation, and signature sizes (download pdf for details).
As summarized in Table 1, the sizes are at least twice as large as RSA and at least ten times larger than elliptic curve algorithms with the same security level. The performance, see Table 2, is so fast that additional hardware acceleration is often not needed. This is true even on embedded processors such as the Arm Cortex-M4. All the lattice-based algorithms use SHA-3 hash functions and performance will likely increase in future when more processors support SHA-3 acceleration.
When using Kyber for key exchange in protocols like TLS and IPsec, the client performs a key pair generation operation followed by an encapsulation operation while the server only performs a decapsulation operation, see Table 2. For the new algorithms, NIST has stopped talking about “bits of security” and has instead introduced five security levels based on standardized symmetric algorithms (AES-128, SHA-256, AES-192, SHA-384, AES-256). Level I for example means that the algorithm is as hard to break as AES-128 on a classical or quantum computer. NIST plan to recommend Level III as the default option for Kyber.
| Security level | ||||||
| I | II | III | IV | V | ||
| Kyber | Public key | 800 | 1184 | 1568 | ||
| Encapsulation | 768 | 1088 | 1568 | |||
| Dilithium | Public key | 1312 | 1952 | 2592 | ||
| Signature | 2420 | 3293 | 4595 | |||
| Falcon | Public key | 897 | 1793 | |||
| Signature | 666 | 1280 | ||||
Table 1. Public key, encapsulation, and signature sizes in bytes (B) for the lattice-based algorithms NIST will standardize. Security levels as defined by NIST
| Security level | ||||||
| I | II | III | IV | V | ||
| Kyber | Key pair generation | 6,4 | 11,1 | 15,7 | ||
| Encapsulation | 9,3 | 14,2 | 20,4 | |||
| Decapsulation | 7,5 | 11,6 | 16,9 | |||
| Dilithium | Key pair generation | 20,9 | 38,1 | 59,0 | ||
| Sign | 41,8 | 87,8 | 103,1 | |||
| Verify | 23,2 | 38,4 | 61,0 | |||
| Falcon | Key pair generation | 4902,3 | 15810,3 | |||
| Sign | 104,7 | 207,4 | ||||
| Verify | 20,9 | 42,3 | ||||
Table 2. Performance in microseconds (μs) on AMD Ryzen 9 5950X for the lattice-based algorithms NIST will standardize. Security levels as defined by NIST
As mentioned, NIST expect to make changes in the final standards. Two changes suggested by Ericsson that may be included are:
- reducing the number of variants of the SHA-3 hash function
- strengthening Dilithium so that it is secure even if the random number generator is weak, while still offering good protection against so-called side-channel attacks where the attacker uses physical information such as timing, radiation, or power consumption.
Adoption of the new algorithms – standards
In addition to lattice-based algorithms, NIST will also standardize the hash-based signatures that rely on the security of cryptographic hash functions. The stateless hash-based signature algorithm SPHINCS+ complements the stateful hash-based algorithms LMS and XMSS that the IETF and NIST have already standardized. Hash-based algorithms are significantly slower than lattice-based algorithms and have significantly larger signature sizes. Stateful hash-based algorithms require the user to keep state, have stringent requirements on private key management, and are only suitable for a few specific use cases. Hash-based algorithms are therefore not expected to see as much deployment as the lattice-based algorithms.
As mentioned above, very few ICT systems make use of NIST algorithm standards directly. Most uses of NIST algorithms are implemented through IETF protocols such as TLS, IKEv2, JWS, CWT, HPKE, and the IETF profile of X.509. IETF has been following NIST’s work closely and is preparing to include the NIST standardized QR algorithms in all important security protocols.
Except for US national security systems, initial deployments of QR algorithms will likely use a so-called hybrid mode, where QR algorithms are used together with RSA or elliptic curve cryptography. Hybrid mode increases implementation complexity but remains secure even if one of the algorithms or its implementation is broken.
The two signature algorithms Dilithium and Falcon have different properties and are an effective complement to each other. Falcon has smaller signatures, smaller public keys, and faster verification, while Dilithium has faster signing and key generation, see Table 2. Some deployments will likely use Falcon for certificate validation and Dilithium for the end-entity public keys used for signing in protocols like HTTPS and IPsec.
As mentioned, 3GPP is set to introduce QR algorithms as soon as it can be done. 3GPP currently relies on IETF protocols like X.509, IKEv2, TLS, DTLS, DTLS/SCTP, JOSE, COSE, and EAP-TLS for almost all uses of public-key cryptography. An exception is the Subscription Concealed Identifier (SUCI) encryption mechanism, but that will likely rely on the new IETF protocol HPKE for future quantum-resistance. Figure 2 illustrates where public key is used in the 3GPP 5G connectivity layer, further uses of public-key cryptography are found in the infrastructure, application, and management layers.
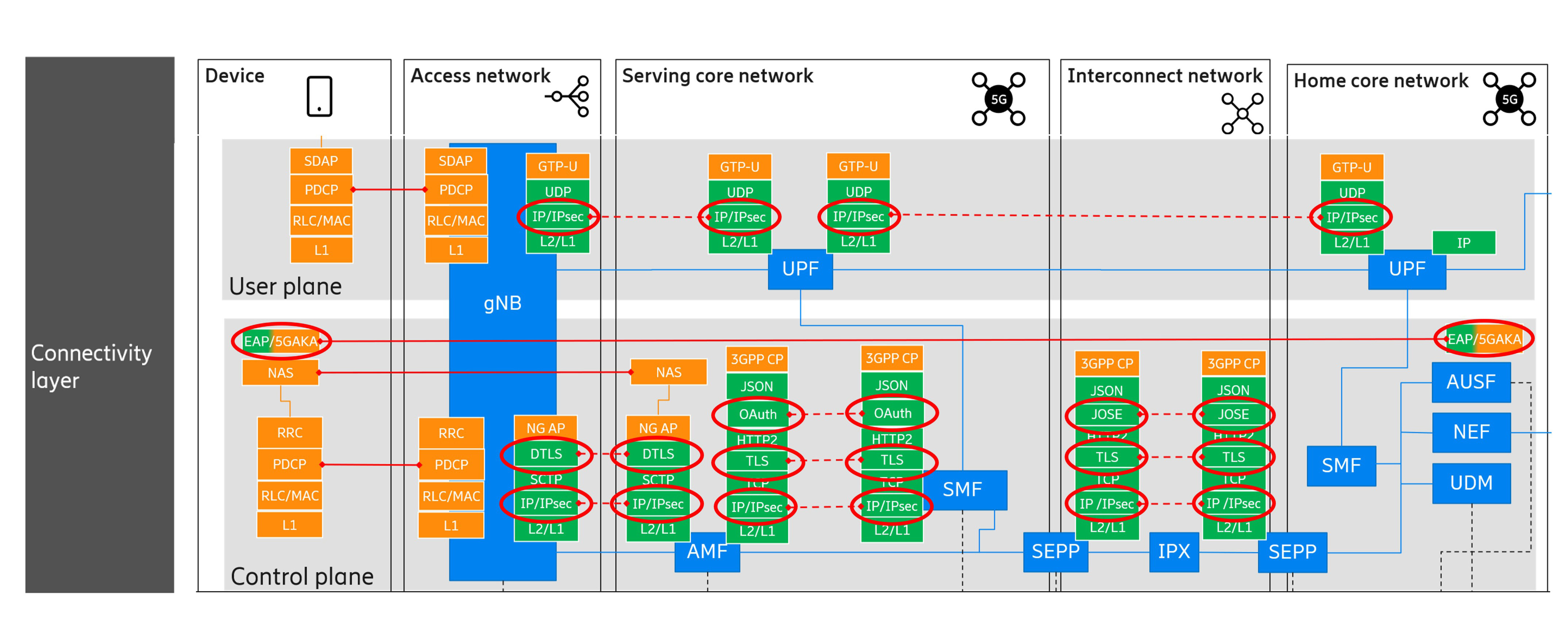
Figure 2. Public key cryptography in the 3GPP 5G connectivity layer.
What will happen next?
NIST’s post-quantum cryptography project will continue even after the currently selected algorithms have been standardized. The project will study alternative algorithms based on other mathematical problems than lattices and hash functions. And while the current lattice-based algorithms work very well for the Web and IPsec, they lead to unacceptable performance degradation in many constrained use cases (download pdf to read more).
Elliptic curve cryptography will likely dominate the Internet of Things even when lattice-based algorithms are used for non-constrained use cases. With 64-byte public keys and a lot of additional features missing from Kyber, the relatively new CSIDH algorithm (pronounced ‘sea‑side’) seems like an extremely promising algorithm for future constrained radio networks.
Further reading
Read the article: Quantum technology and its impact on security in mobile networks
Read the blog post: The evolution of cryptography in mobile networks and how to secure them in the future
Learn more about the new QR algorithms in the NIST resource center
Explore 5G
Explore IoT
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.