Unifying threat modeling and hunting at runtime for proactive cyber defense
- Technology is advancing rapidly, the Internet of Things (IoT) is growing at a fast pace, and digital transformation is taking off. In combination, these developments lead to a surge in both data creation and novel digital applications. An undesired consequence is increased opportunities for new and sophisticated threats that are hard to detect.
- This blog post from Ericsson’s security research team addresses how to combine the methods of threat modeling and threat hunting to provide a comprehensive and proactive approach to identify and mitigate security threats.
Recent advances in digital transformation provide great opportunities for innovation and growth and have the potential to reshape several industries. 5G – and eventually 6G – networks can connect billions of IoT devices that can share data and interact with centralized systems and with each other. The massive expansion of generated data and interconnected devices that follows will significantly enlarge the cyber-attack surface, introducing more opportunities for suspicious activities and malicious actors, for example, advanced persistent threats (APTs). This risk is further escalated by the diversity of platforms, protocols, and devices, which leads to the development of new attack techniques and threat variants.
Many different industry sectors are connected to telecom networks to provide and to utilize services. Threat actors have been known to exploit weak configurations in cloud infrastructure, underlying operating systems, and cloud native network functions to gain initial access to other systems. In addition, some threats may already be present in an organization's network, remaining undetected for months.
Let us give you two examples of attacks involving telecommunication networks:
Mandiant exposed the activities of a threat group called APT1 that succeeded in making unauthorized intrusions to over 150 victims, including governments and major industries.
Similarly, CrowdStrike revealed that the LightBasin attack has been active since 2016, but went unnoticed for six years, and was not detected until 2022.
In such an evolving ecosystem, traditional security measures must be improved to address these types of attacks. Relying on threat modeling to anticipate vulnerabilities or attack detection to identify existing threats is no longer sufficient.
Threat hunting is a proactive line of defense that identifies threats before they become full-blown attacks. This is achieved by navigating beyond the traditional indicators of compromise (IoC: a sign that a system has already been breached) and indicators of attacks (IoA: a sign that an attack is in progress or being attempted) to uncover potential threats and stop attackers.
Knowledge of specific attacks is crucial for effective threat hunting. An all-purpose threat hunting tool would be ideal, but it is often unfeasible due to the complexity and creativity of the attackers.
Read our comprehensive survey paper on threat hunting
Download the paper
Threat modeling, attack detection, and threat hunting—how do they differ and complement each other?
Organizations employ multiple lines of defense, including threat modeling, attack detection, and threat hunting.
Threat modeling involves the proactive identification and assessment of potential security threats related to the network or system. Examples for telecom networks include fake base stations, radio resource control signaling storm and paging attacks. Threat modeling enables organizations to design their systems with robust security from the outset and prioritize their security efforts effectively. This approach helps to mitigate risks before they can be exploited, but also improves the overall security posture of the organization.
Attack detection, in tandem with threat modeling, plays a critical role. Here, network traffic and system logs are monitored to identify any signs of malicious activity, for example, in the network data analytics function of a 5G service-based architecture. The runtime identification of threats through detection tools minimizes potential damage and helps in understanding the techniques used by attackers.
Threat hunting is a proactive defense strategy where security experts analyze various telemetry data to identify advanced threats that have evaded detection mechanisms. The data can include information collected from endpoints, users’ activities, and control plane interactions, for example. Proactive hunting helps uncover hidden threats, reduces the time attackers spend undetected within the network, and continually enhances security measures and incident response capabilities.
A comprehensive security strategy should include these three steps:
- comprehensive threat modeling to minimize and address security issues during the design phase,
- effective attack detection mechanisms to identify threats in real-time,
- a proactive threat hunting approach to capture attacks that inevitably bypass defenses undetected.
| Threat modeling | Attack detection | Threat hunting | |
| Definition | A systematic process to identify and address potential threats during the developmental phase of a system | Continuously monitoring systems to detect and report suspicious activities as they happen | A proactive, iterative approach to finding advanced threats that bypass existing detection solutions |
| Approach | Proactive | Real-time monitoring | Proactive |
| Focus area | Architecture | Known threats | Stealthy threats |
| Execution | During the design phase | Continuous, in real time | Ad-hoc, based on suspicions or indicators of compromise |
| Expertise | A broad understanding of the system's architecture and potential risk areas | Automated tools and solutions, expertise in configuring and maintaining these systems | Deep knowledge of cybersecurity for analytical and exploratory investigations |
| Techniques | Data flow diagrams, Attack trees, STRIDE methodology, and more | Signature matching, anomaly detection, machine learning (ML) algorithms, and more | Statistical analysis, ML, user and entity behavior analytics, and more |
| Tools | Microsoft Threat Modeling Tool, OWASP Threat Dragon, and more | Security information and event management, intrusion detection systems, endpoint protection platforms, and more | Advanced threat intelligence platforms, big data analytics platforms, and custom scripts and algorithms for deep data analysis |
| Security capabilities | Preventing threats | Detecting known threats and generating alerts for immediate response | Proactively discovering new, unknown threats and generating intelligence |
| Outcome | Preventive measures for identified threats | Immediate response to threats and alerts | Enhanced security posture by proactive threat identification |
Table 1: Qualitative comparison between threat modeling, attack detection, and threat hunting
Integrating threat modeling with threat hunting—why is it crucial?
The integration of threat modeling and threat hunting helps update the threat model during runtime, with newly discovered threats guiding the threat hunter to the most prioritized risks. This integration forms a comprehensive defense strategy against known threats while anticipating and adapting to new and evolving cybersecurity challenges, thereby strengthening the overall defensive posture.
Here we visualize how this would work.
The animation first illustrates a timeline-based scenario of detecting a sophisticated attack. We will call it APT X telecom or enterprise attack.
The attack was not defined in the knowledge base, nor did it trigger any known IoC or IoA during its execution. APT X is not defined in the threat model database since threat modeling is executed during the development phase and may not contain definitions or signatures of APT X. Therefore, the detection mechanism may not be able to detect the attack in time and mitigate it before its full execution. Future occurrences of APT X might also go undetected.
This is where threat hunting becomes invaluable. The threat hunter proactively searches for hidden attacks using new IoC and unconventional attack patterns. Once identified, the information is added to the cyber threat intelligence knowledge base, a structured repository of information about cyber threats, their techniques, and tools.
However, as shown in the animation, manually hunting a threat and uncovering its pattern can take a lot of time and effort since multiple tools and techniques must be used. Meanwhile, another attack could occur even before the first one is detected.
A synergistic approach that combines threat modeling with threat hunting by updating the threat model database at runtime will enhance attack detection capabilities. As illustrated in the final part of the animation, the threat model database will be updated with the information discovered by the threat hunter, leading to faster detection of new attacks in the future.
Runtime threat modeling and threat hunting—what are the contemporary challenges?
Despite the importance and the benefits shown by threat modeling and threat hunting in enterprise networks, several challenges can hinder their effectiveness in the telecom domain:
- Expert dependency: Threat modeling is highly dependent on expert knowledge, both in the system and in the security domains. Threat hunting still requires manual intervention, for generating hypotheses, analyzing patterns, correlating events, and investigating hypotheses. Manual processes are time-consuming and prone to human error. They also do not scale well in larger and complex environments such as networks that comprise multiple security domains and multiple planes for data and signaling isolation, making it difficult to keep pace with the rapid evolution of cyber threats within networks.
- Managing the surge in event volume: Mobile networks continuously evolve to support new use cases and enable new capabilities. This increases the number and diversity of devices, assets, and data in the network, which in turn leads to an exponential growth of call logs and alerts. Such a flood of information makes it challenging for threat hunters to scrutinize and identify genuine threats in networks. The sheer volume can overwhelm network monitoring systems and analysts, resulting in alarm fatigue, delayed responses, and potentially missed threats.
- Navigating the risk of false detection: In the process of detecting threats, systems often flag benign activities as malicious (false positives), leading to a waste of time and resources, as security teams must investigate each alert. Additionally, systems can flag stealthy activities as benign (true negatives), leaving the threat lurking within enterprise networks.
- Continuous race against evolving threats: Cyber threats in telecommunication networks are continuously evolving. Attackers constantly develop new tactics, techniques, and tools to bypass network security measures. Staying updated on the latest threat landscape is a significant challenge. Continuous learning and adaptation of security strategies are needed, which can be resource-intensive and difficult to manage.
Use case examples
Threat modeling and threat hunting can be integrated to identify stealth attacks in networks strategically. When combined, they can detect attacks on both enterprise and telecom networks.

Example: Identify credential dumping by threat actor groups
Threat modeling helps identify threats to critical assets and define countermeasures to prevent or mitigate their effects. For example, an organization's active directory could be a target for threat actors attempting to escalate privileges.
The model can highlight specific MITRE adversarial tactics, techniques, and common knowledge (ATT&CK) techniques, such as credential dumping, which are relevant to the threat landscape. The threat model indicates that adversaries may use tools such as Mimikatz or Windows built-in commands to dump credentials. These indicators guide threat hunting practitioners in focusing on identifying suspicious processes, unusual access to the security account manager (SAM) database, or abnormal use of local security authority subsystem service (LSASS) memory, which can lead to identifying an APT campaign.
Example: Iteratively improve detection of a stealthy jamming attack
The initial threat modeling identifies jamming attacks, using MITRE FiGHT, as a high-risk threat to the physical layer of the RAN, targeting the communication between user equipment and the base station.
Threat hunters detect signs of reduced signal quality or abnormal power consumption in certain frequency bands. They discover that certain network segments have experienced subtle interference that mimics regular radio noise, making it difficult to detect using conventional means. These hunting findings are then used to adjust and refine the original threat model at runtime by incorporating these new stealth techniques.
What are the dynamic approaches for integrating runtime threat modeling with threat hunting
How can threat modeling guide and enhance threat hunting efforts?
This combination approach aims to use threat modeling to guide and prioritize threat hunting activities, addressing a wide range of security threats, including those in mobile networks. As illustrated in figure 1, threat modeling serves as the foundational step for (intent-based) threat hunting by identifying key assets in networks and potential threats. The hunting activity leverages intelligence, such as IoCs and IoAs derived from threat modeling, to guide and enhance the hunting process
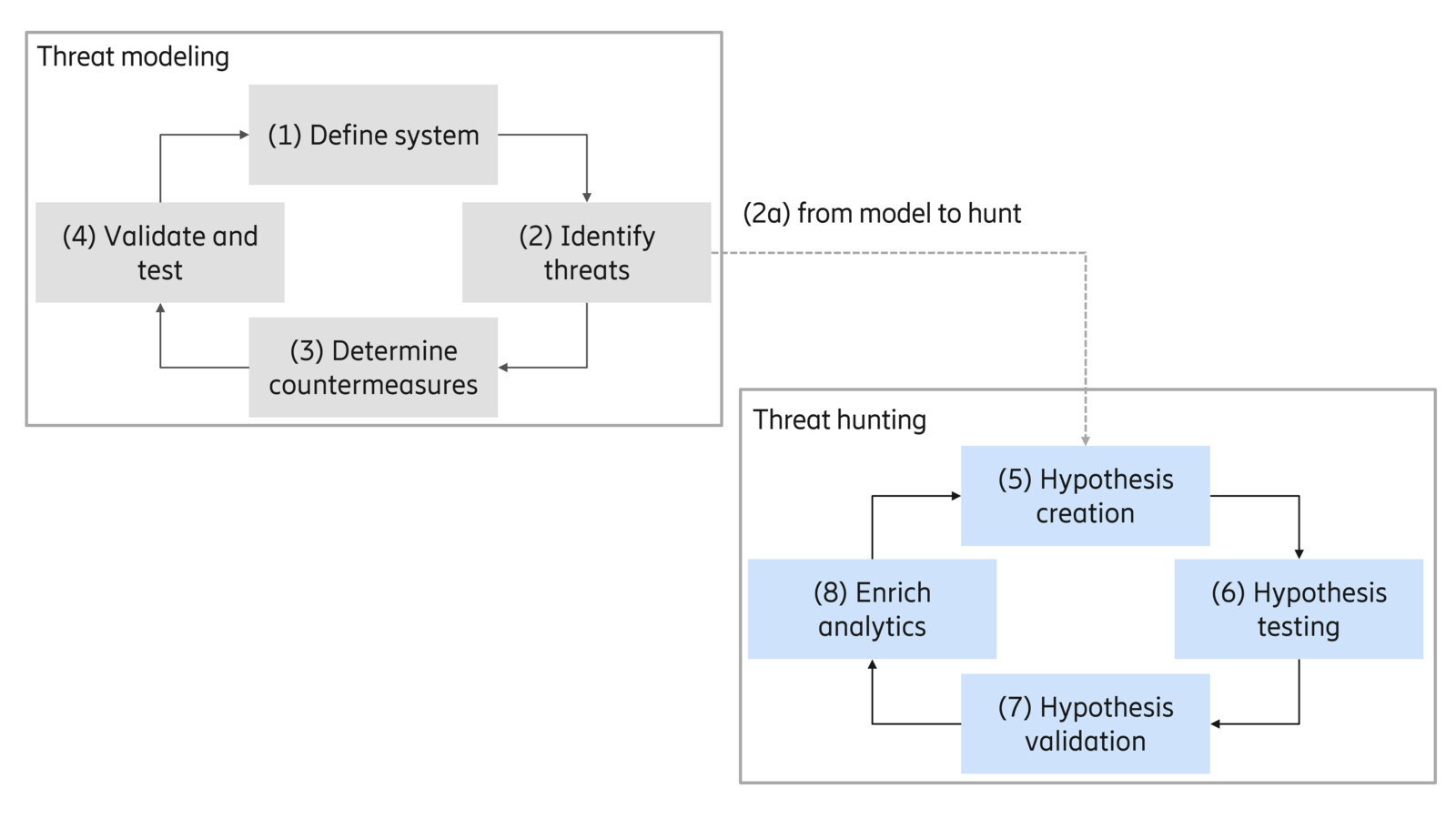
Figure 1: From threat modeling to hunting
In future networks, this combination approach enables threat hunters to proactively search for new signs of compromise on key system assets that are highly valuable. Examples include core network functions that manage and store valuable subscriber data, such as the access and mobility management function or the unified data management, as well as network functions that are exposed to external entities, such as the network exposure function. However, some important and new threats can be overlooked during the threat hunting phase if the threat model is not comprehensive. This approach also necessitates the continuous updating of the threat model to accommodate emerging potential threats.
How does threat hunting update threat modeling with newly discovered threats?
As illustrated in figure 2, this approach starts with an initial round of threat hunting using the threat model database. Through a continuous feedback loop, findings from the hunting phase are used to update and improve the threat model database during runtime, which is considered one step in threat hunting: enriching analytics. The enriched analytics then guide the threat hunting for future investigations. This process is crucial in mobile networks, where new vulnerabilities and attack vectors evolve rapidly. The loop is closed by going back to the hunting phase with an updated threat model database for the next round of threat hunting.
For instance, precise identification and mitigation of threats specific to the telecom domain can be achieved by integrating mobile network threats into the threat model database, ensuring comprehensive coverage. This iterative process ensures that both the threat model and the hunting strategies are continuously refined and kept up to date.
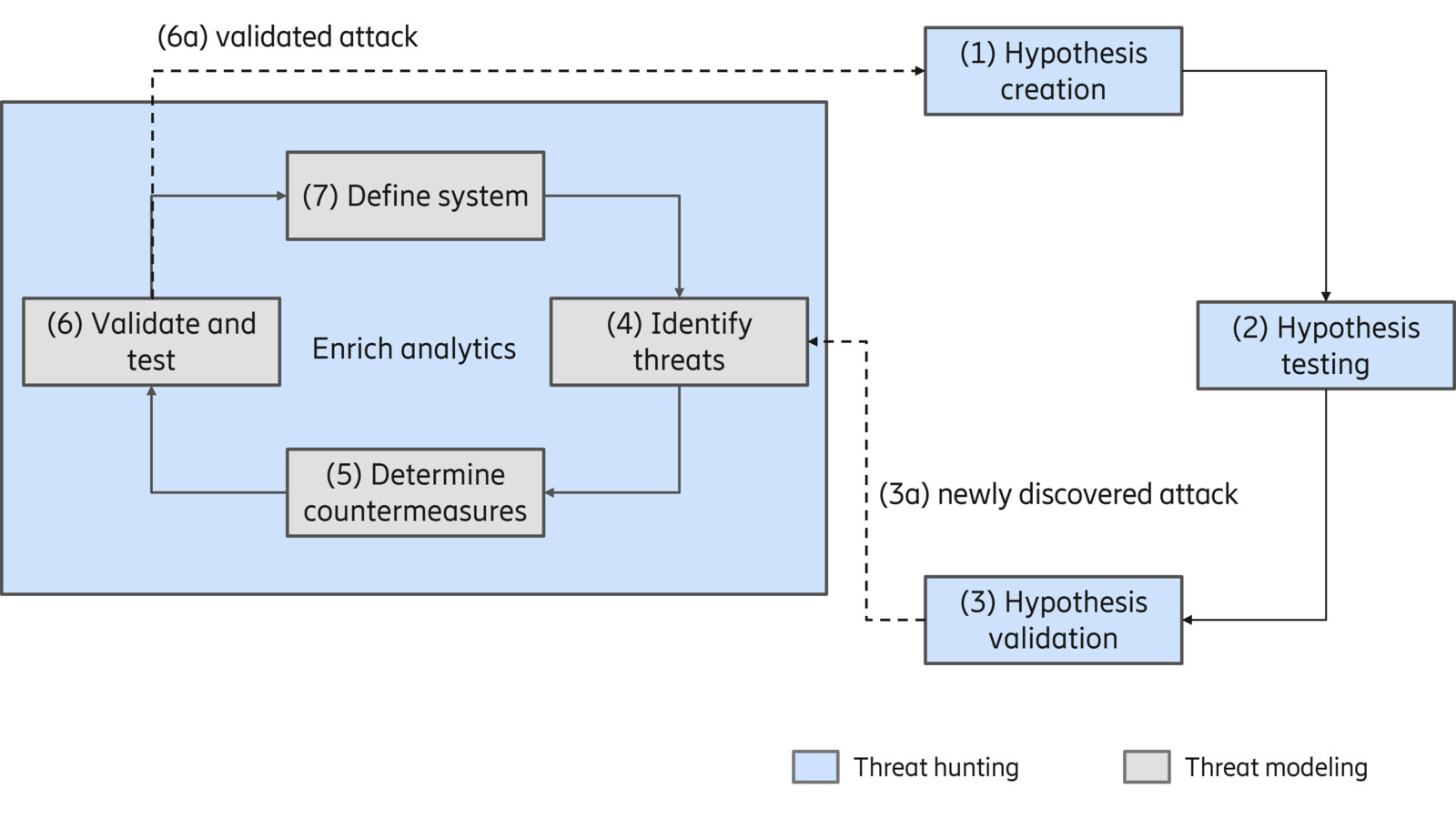
Figure 2: Iterative hunting-modeling feedback
How do threat modeling and hunting work together using common tools?
This approach relies on using tools that can support the hybrid execution of both activities on the same component in networks. In other words, identifying threats in the current system while proactively creating new hypotheses for threat hunting, as illustrated in figure 3.
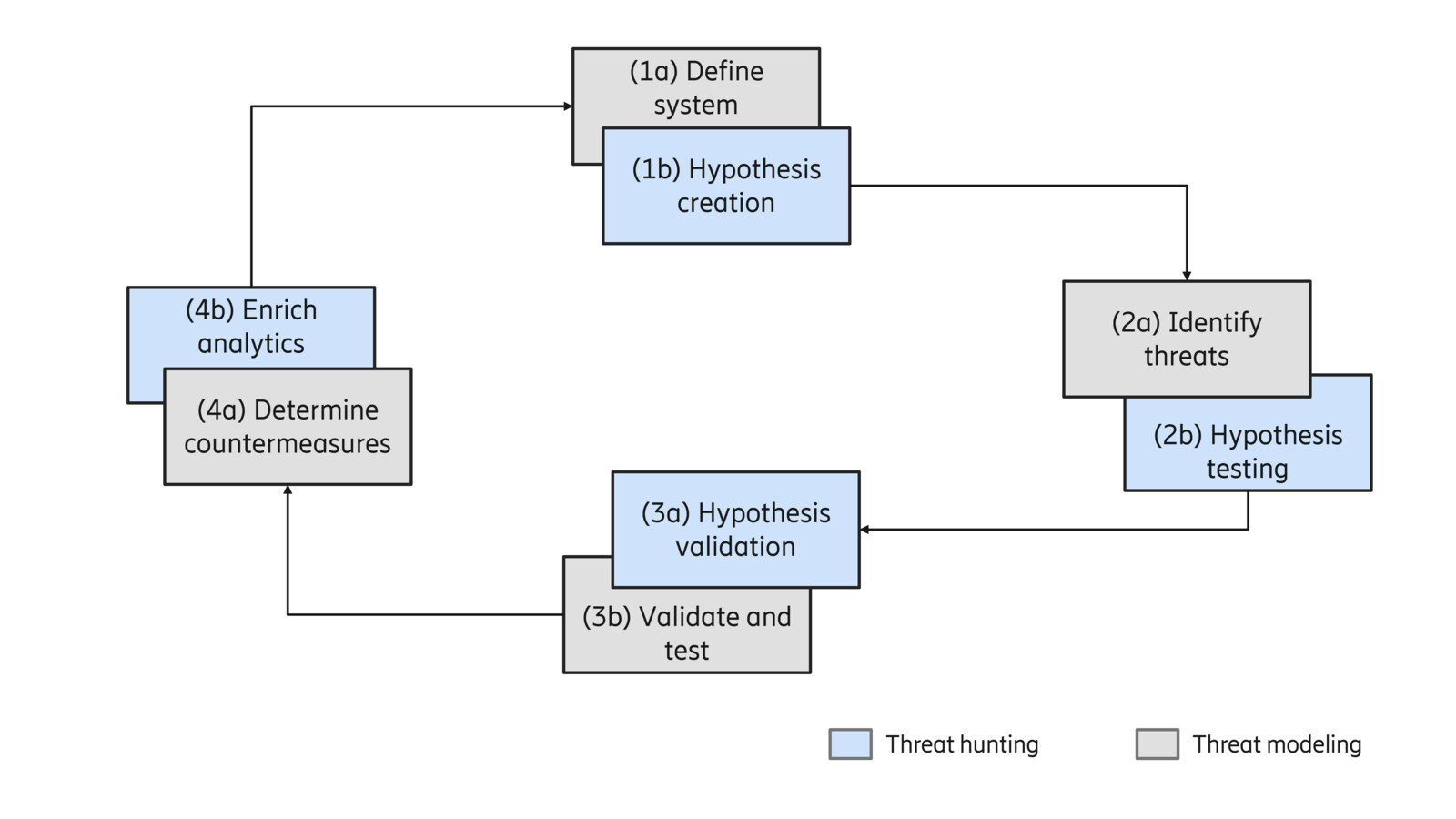
Figure 3 : Common hunting-modeling tooling
In future networks, this integration is crucial because the telecom domain presents unique challenges and opportunities for threat detection and prevention. To perform such seamless integration, the tool must support features from both activities, such as threat visualization, countermeasure suggestions, and hunting analytics. Additionally, the tool should have access to up-to-date cyber threat intelligence (CTI), network data, and incident alerts. This integration helps to populate the threat model as well as threat intelligence databases.
Operating simultaneously through the tool, threat modeling identifies potential vulnerabilities while threat hunting proactively searches for indicators of compromise related to these vulnerabilities. This synergy enables a robust defense against new vulnerabilities and threats in the networks, ensuring that the security posture adapts to the rapid developments and specific characteristics associated with telecom networks.
Summary
The key benefit of this research work lies in building a holistic and dynamic cybersecurity defense mechanism by combining threat modeling and threat hunting. In our solution, the continuous update of threat modeling at runtime using threat hunting findings ensures that the defense mechanism adapts swiftly to emerging threats while, at the same time, threat hunting is guided by threat modeling knowledge.
Threat modeling provides strategic foresight while threat hunting guides in tactical agility. This symbiotic merger is expected to enhance the security posture of a system.
Full research paper behind the work
Download paper
In writing this blog post, the author would like to thank Sonika Ujjwal, Zakaria Laaroussi, Makan Pourzandi, Utku Gülen, Leyli Karaçay, and Loay Abdelrazek for their feedback.
Read more about our security research
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.
