Reports and papers
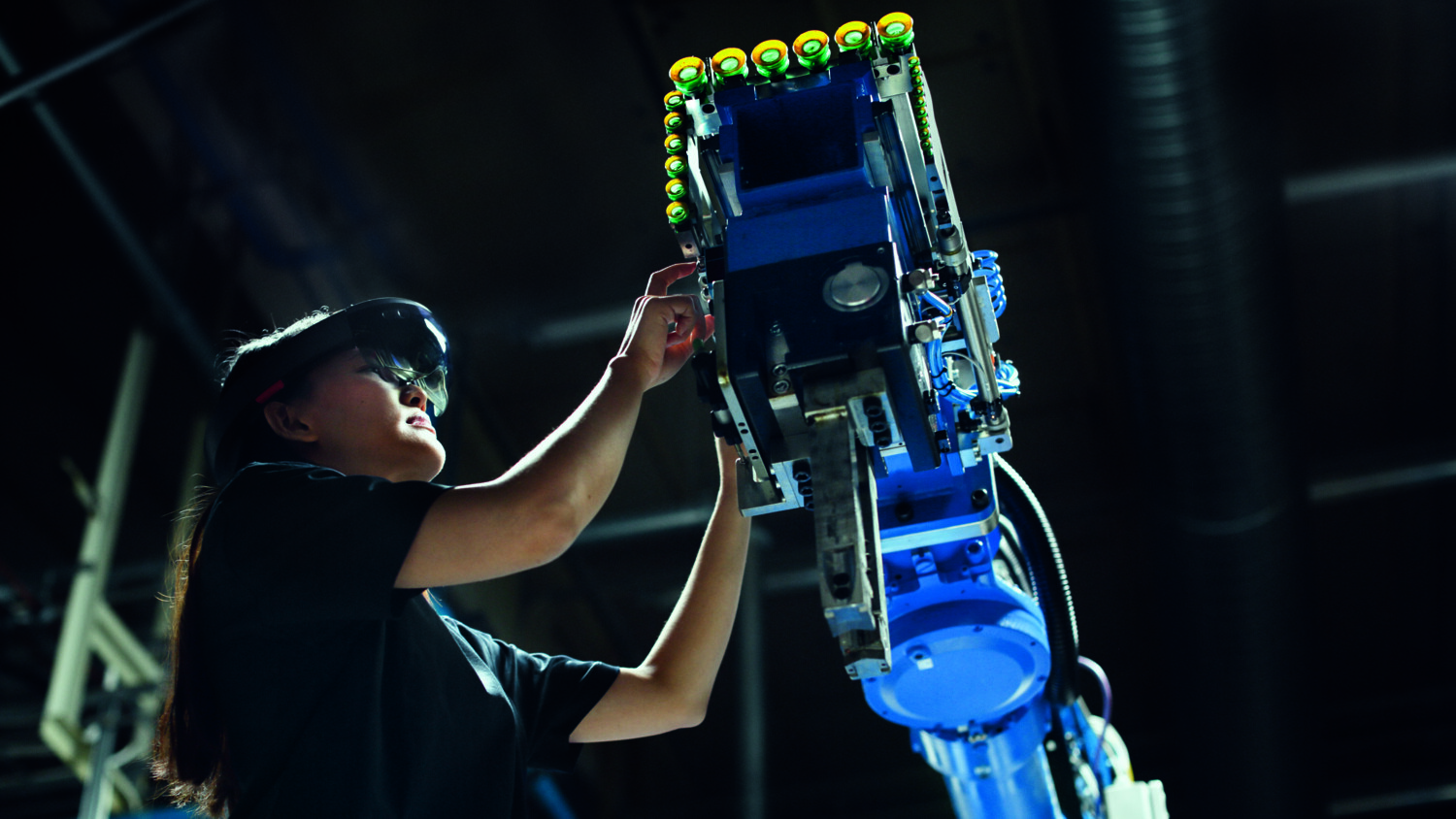
We have captured what's next in ICT, based on inhouse research and research in collaboration with academia and other partners. This is what we see coming, new trends and insights. Explore our reports, white papers, blogs and technical publications.