Critical infrastructure relies on 5G network resilience and security
Governments and enterprises are adopting advanced technologies through 5G, relying on predictable performance and security assurance of mission and business critical processes. 5G is powering everything, from factory automation to remote control of assets and more. When it comes to security and high performance, the 5G platform is a truly resilient system.
What makes a resilient 5G system
A resilient 5G system is always available, reliable, performs as expected, and recovers quickly when facing disturbances or attacks. The technical capabilities of a resilient 5G system include a combination of reliability, availability, robustness and security, whilst protecting privacy. These fundamental properties are inherent within telecom networks today and are extended even further with new technologies and capabilities.
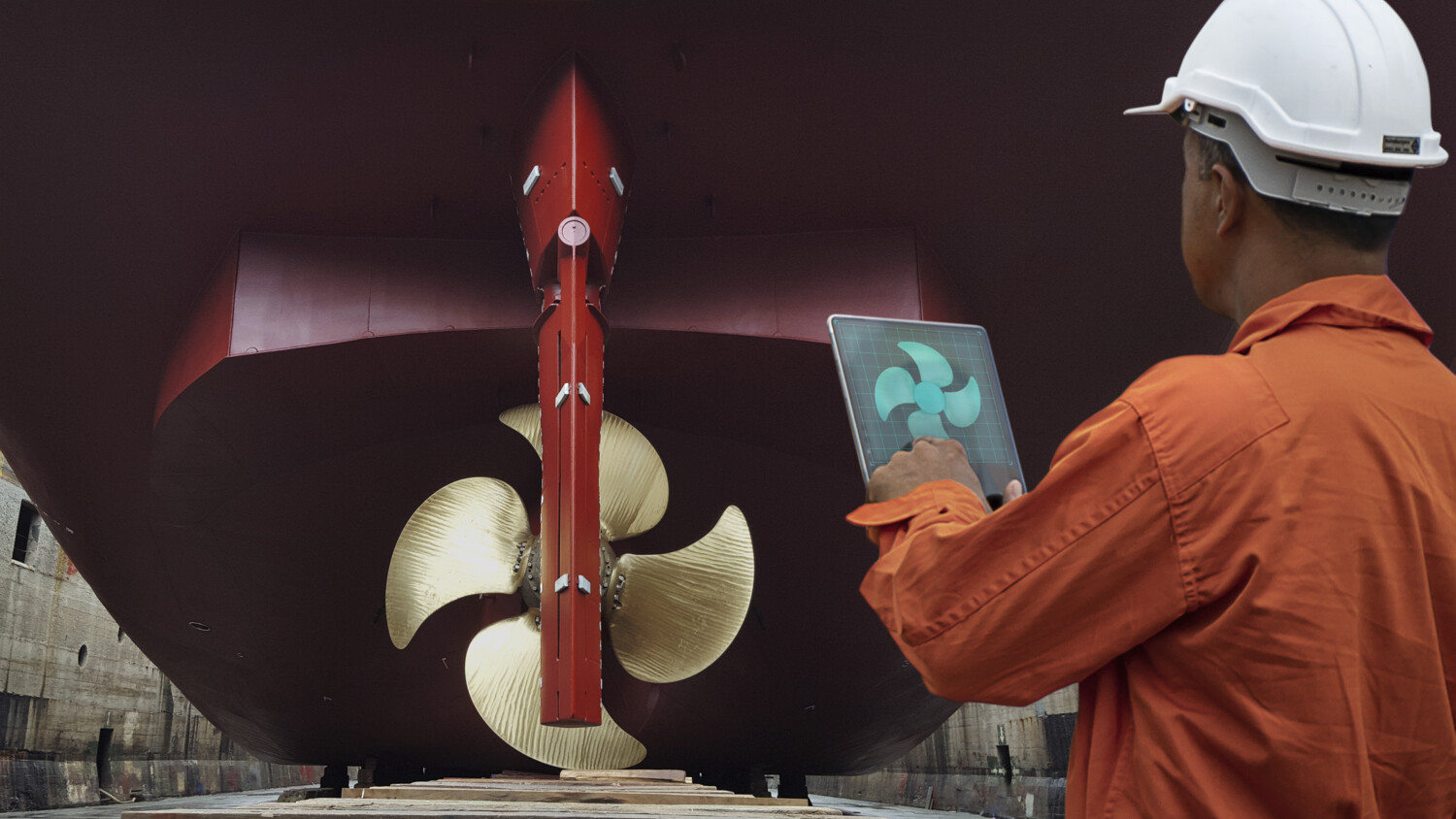
Day by day, existing critical functions in society are being moved into the digital domain, becoming dependent on telecom networks. At the same time, new capabilities are enabling new use-cases to be realized. This is driving the evolution of traditional telecom networks into the primary innovation platform for both industry and society. This has led to various new demands on the 5G system, particularly mission and business critical use cases.
For example, remote-controlled machines that operate on time-critical communication. If a person is obstructing a machine and due to that is in physical danger, the machine needs to stop instantly. In such a scenario, the availability and predictability of the 5G performance must be maintained.
To continually meet the needs of the constantly evolving threat and risk landscape, four key development components are critical for building trustworthy systems.