Why a centralized DevSecOps model?
A centralized model replaces fragmented, manual routines with industrialized software delivery. Traditional operations rely on diverse tooling and local expertise, resulting in slow troubleshooting, uneven quality and long security patch cycles. Centralization enables expert teams to operate shared pipelines and practices so that improvements benefit all customers.
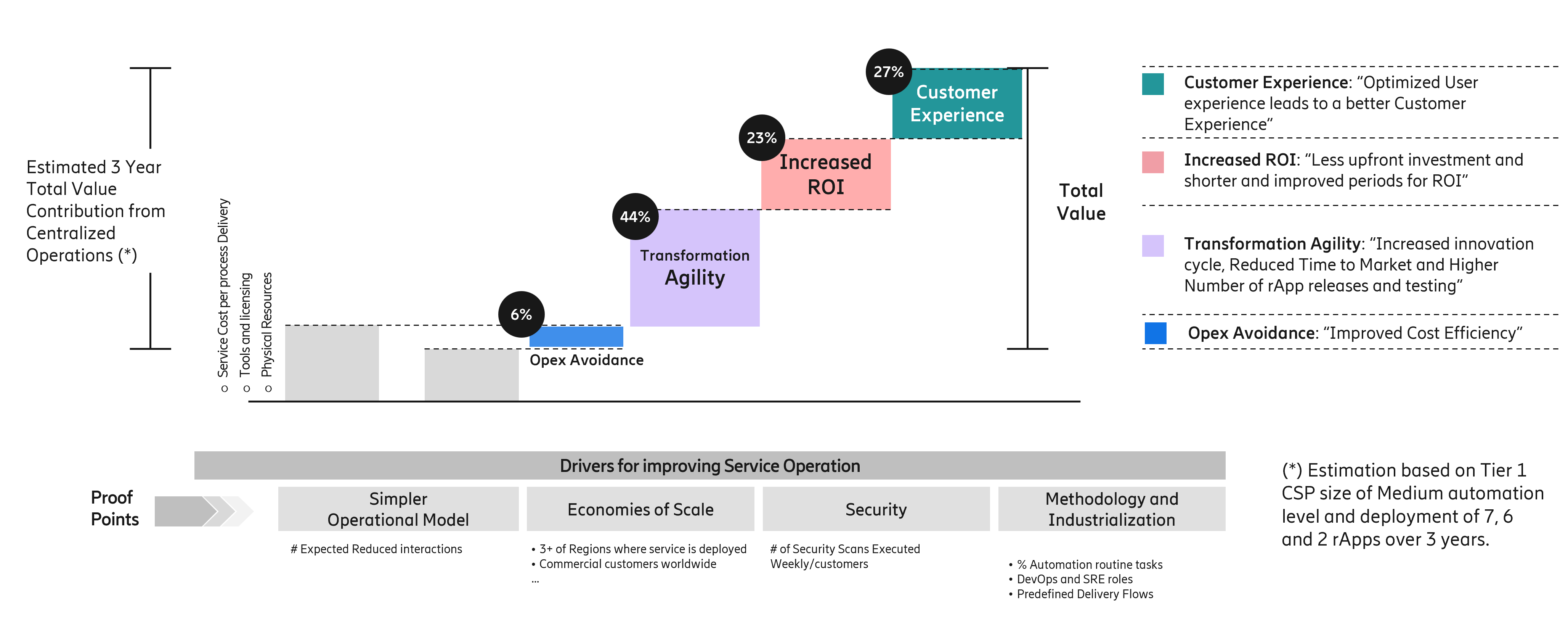
Key business value resides mainly in four categories: OPEX avoidance, transformation agility, increased ROI and enhanced customer experience.
These outcomes translate into accelerated time to value through high cadence automated releases, improved service reliability supported by proactive observability and faster issue resolution, lower risk through standardized and automated security controls, and reduced cost to serve through economies of scale and simplified operations.
Sovereignty remains protected through customer-managed role based access control (RBAC) and strict data handling boundaries.

Key business value resides mainly in 4 categories: OPEX avoidance, transformation agility, increased ROI and enhanced customer experience.
This chart explains how a centralized and automated operating model for rApps drives value for a CSP beyond simple OPEX reduction. While cost efficiency is important, it is not the primary value driver once automation and DevSecOps practices are in place.
These figures represent an estimated three‑year total value contribution based on a Tier‑1 CSP, medium automation maturity, and the deployment of 7 rApps in year one, 6 in year two, and 2 in year three. So the message here is about value distribution and direction, not an exact financial forecast.
Reading the chart from left to right
“Starting on the left, we see the baseline CSP operational cost structure. With centralized operations, we first address OPEX avoidance, which represents roughly 6% of the total value contribution.”
“This includes improved cost efficiency through:
Fewer manual operational tasks
Reduced duplicated tooling and processes
Centralized delivery tools, licensing, and infrastructure”
“OPEX avoidance is real, but it is not the dominant source of value in a mature automation scenario.”
Transformation Agility – the main value driver
“The largest value block comes from Transformation Agility, contributing around 44% of total value.”
“This reflects the impact of:
Faster innovation cycles
Reduced time to market for rApps
Higher frequency of releases, upgrades, and testing
Industrialized deployment and lifecycle management”
“In practice, this is what allows CSPs to scale automation safely while keeping pace with network evolution and vendor innovation.”
Increased ROI
“Next, we have Increased ROI, accounting for about 23% of the total value.”
“This comes from:
Lower upfront investment per rApp
Shorter payback periods
Better reuse of centralized DevSecOps capabilities across multiple rApps and regions”
“Instead of building and maintaining bespoke operational setups per application, the CSP benefits from economies of scale.”
Customer Experience impact
“Finally, Customer Experience contributes roughly 27% of the overall value.”
“This is driven by:
More stable and predictable rApp operations
Faster issue resolution and patching
On‑time security updates and vulnerability remediation
Consistent service quality across regions”
“The key point is that improved user experience is a consequence of better operational agility and security—not an isolated initiative.”
Key takeaway
“The main takeaway from this chart is that centralized operations shift value creation:
Away from pure cost cutting
Toward agility, speed, security, and business outcomes”
“In a Tier‑1 CSP with moderate automation maturity, the majority of value over three years comes from how fast and safely innovation can be delivered at scale, rather than from operational cost reduction alone.”
And with that, the next slide looks at what customers need to have in place to unlock the full value of centralized DevSecOps – from deployment to monitoring to complete lifecycle management.
Figure 1: Value Argumentation – Centralized Operations Benefits
Insights into the centralized operating model
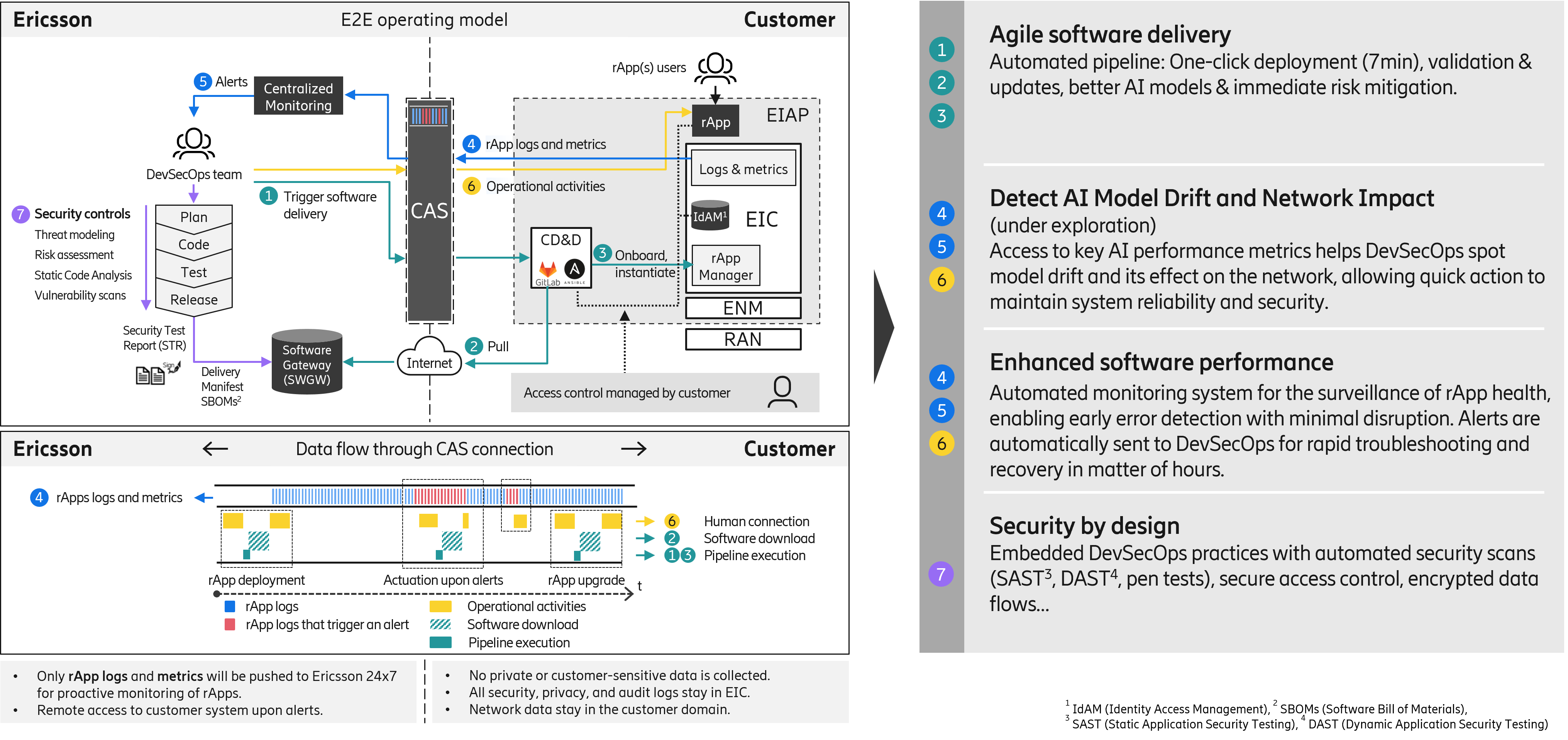
The operating model integrates four core capabilities: automated software delivery, proactive observability, secure connectivity and lifecycle governance. Automated pipelines orchestrate delivery, validation, upgrades and rollbacks with standardized and customized playbooks as needed so as to fulfill customer software security processes.
Proactive monitoring combines logs, metrics and alerting logic to detect anomalies early and trigger rapid incident management response from DevSecOps teams.
Customer Access & Security (CAS) is Ericsson’s solution to provide IP secured network connectivity to customer´s nodes & data to operations and customer support personnel (Human Access) and automated Machine-to-Machine (M2M) communications that support business contracts. CAS provides secure transport for telemetry and controlled remote access. Customer managed Role Based Access Control (RBAC) guarantees least privilege visibility, while all privacy, audit and security logs remain within the Ericsson Intelligent Controller (EIC) 1. Lifecycle governance leverages operational analytics to refine backlogs, evolve quality gates and propagate best practices across markets, turning rApp evolution into an industrialized process.

This image brings everything together by showing how our centralized operating model actually runs in day‑to‑day operations.
Starting on the left, you see the DevSecOps team, where all code changes, security checks, and automated testing occur. Once an update passes all gates, it moves into our controlled delivery pipeline and is triggered securely toward the customer environment.
At the center is CAS, enabling data transfer for our centralized operating model. All operational activities: deployment, metrics collection, incident detection, and automated troubleshooting flow through CAS. Importantly, all performance data remain within the customer domain – no private or sensitive network information ever leaves the site.
The bottom flow shows how continuously we operate. rApp logs, metrics and operational activities are flowing, enabling proactive detection and rapid response. And because no customer‑sensitive data is collected, we maintain full sovereignty and compliance.
On the right side, you see the value this model unlocks:
1. Agile software delivery With automated pipelines, we achieve one‑click deployment in minutes, immediate validation, and instant risk mitigation. This gives customers pace and predictability.
2. Detect AI model drift & network impact - An area that is under exploration to enable the continuous monitoring of AI performance metrics. If a model drifts or if a change affects the network, DevSecOps teams will be alerted immediately and can take corrective action long before service degradation occurs.
3. Enhanced software performance- Automated monitoring allows early detection with minimal disruption. Issues are routed straight to DevSecOps for rapid diagnosis and recovery, often within hours—not days.
4. Security by design- We apply embedded DevSecOps practices: secure coding, automated SAST and DAST testing, encrypted data flows, and strict access control. This ensures that every deployment meets the highest security standards from day one.
In short, this model gives customers a secure, automated, and highly transparent way of running rApps at scale, while giving Ericsson full operational efficiency and consistent quality across all markets.
So with this end‑to‑end model, we can deploy, monitor, and resolve incidents with speed, precision, and built‑in security — all while maintaining full customer sovereignty.
And of course, different customers have different levels of privacy and regulatory requirements. What’s important is that the operating model is flexible enough to adjust to these conditions.
Let’s recap in the next image the business value of the automated and centralized operating model that is being offered.
Figure 2 Centralized Operating Model – Deployment, Monitoring and Security
Customer requirements
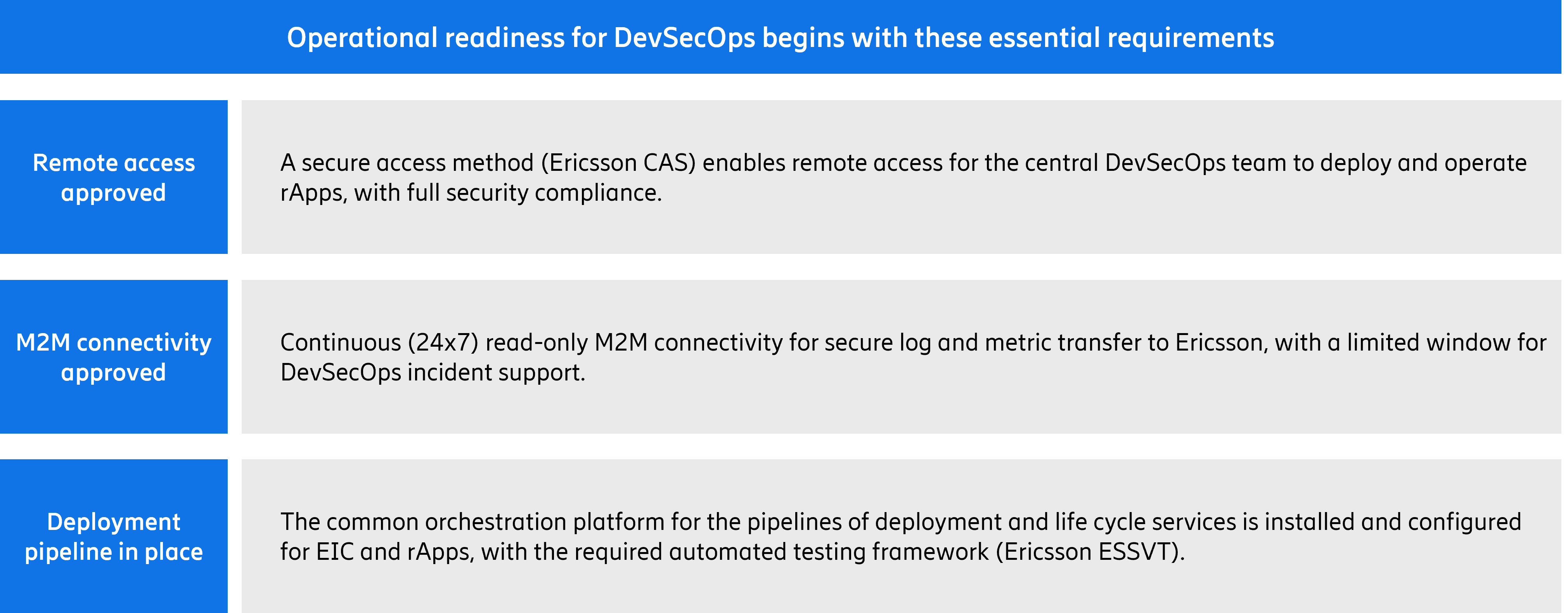
To unlock the full value of centralized DevSecOps, CSPs must meet several baseline readiness conditions. These include:
- CAS remote access approval to enable secure DevSecOps operations.
- Machine to machine (M2M) connectivity for 24×7 read-only transfer of rApp logs and metrics.
- An operational deployment and lifecycle pipeline integrating automated testing and orchestration.
- Aligned governance between customer superusers and DevSecOps teams.

This image outlines the essential readiness criteria a customer needs in order to run centralized DevSecOps effectively. Think of these as the foundational building blocks that enable automation, security, and seamless lifecycle operations.
First: Platform readiness. The customer’s platform – both EIC and the rApps – must be verified and have the required capacity. This ensures that the infrastructure is capable of supporting continuous deployment, proactive monitoring, and all lifecycle automation tasks without performance constraints.
Second: Remote access approval. A secure, compliant access method – through CAS – is required. This is what allows the central DevSecOps team to deploy, upgrade, and operate rApps while still meeting the customer’s sovereignty and security requirements.
Third: M2M connectivity approval. This is a 24×7 read‑only machine‑to‑machine channel that enables secure log and metric transfer. It gives our operations team full visibility into system health while maintaining a very limited and tightly controlled operational window for incident support.
And finally: A deployment pipeline in place.
The customer needs the common orchestration platform configured for both EIC and rApps. This includes the automated testing framework and the toolchain required to execute deployments quickly and consistently.
Together, these four enablers determine a customer’s operational readiness. When all are in place, centralized DevSecOps can operate at full efficiency – delivering rapid updates, continuous monitoring, and high‑quality, secure lifecycle management across all deployed rApp
And this brings us to an important topic many customers ask: What exactly does Ericsson control, and what remains fully under customer authority – especially around optimization and any actuation in the network?
Figure 3: Operational Readiness Requirements for Centralized DevSecOps
When all these enablers are in place, centralized DevSecOps can operate at full efficiency, allowing rapid software updates, continuous monitoring, and high-quality, secure lifecycle management across all deployed rApps.
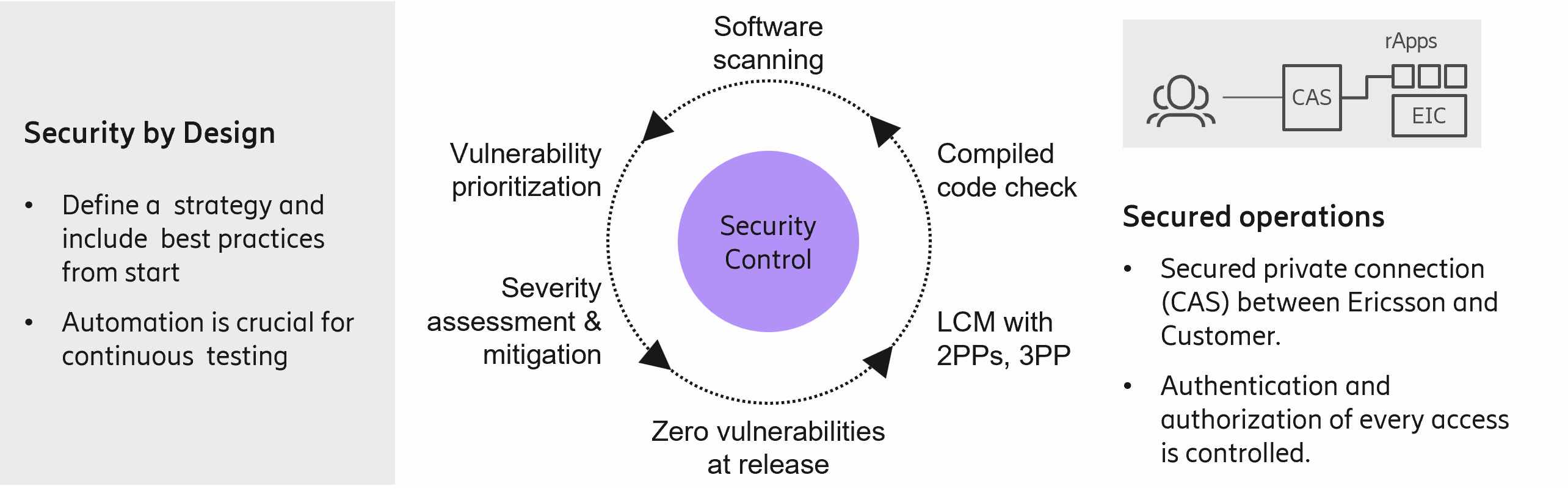
Security “by design”
Security is not an addon, it is built in from day-1 and engineered across the lifecycle. Ericsson security strategy is designed to provide comprehensive protection against a wide range of threats, ensuring the integrity, confidentiality, and availability of critical assets. By adopting a multi-layered approach, vulnerabilities are proactively identified, risks are mitigated, and potential incidents effectively addressed. This strategy emphasizes continuous monitoring, risk assessment, and adherence to industry best practices to maintain a robust security posture.
The security controls implemented encompass a variety of technical and procedural measures. These include access management protocols to restrict unauthorized entry, encryption techniques to safeguard sensitive data, and network security tools such as firewalls and intrusion detection systems to prevent and detect malicious activities. Additionally, regular audits, employee training programs, and incident response plans are integral components that reinforce our defense mechanisms and ensure readiness in the face of evolving cyber threats.

In Ericsson we have a Unique blend of deep domain expertise & leading AI research, delivering both better performance & productivity boost (allowing engineers do new scope | more, faster)
We are also pushing the industry further through Cognitive Labs for open-source AI research
Nothing worthwhile in life comes easy. The results we deliver in the field speak by themselves; they come from 3 things we have put in: 1. significant Time spent to mature differentiated AI – e.g. RET took three years of continuous development to reach the performance it has today. 2. leveraged our Global scale, working closely with many CSPs in collaborative, real‑network environments to train, validate, and refine our AI models. 3. Significant R&D commitment – today we have about 3,500 engineers dedicated to EIC and rApps, and throughout this entire journey we put at the heart.
And this is where our operating model becomes truly unique.
We run a TRUE DevSecOps model, where the same team that develops an rApp also operates it centrally. This creates full accountability end‑to‑end and ensures that the quality, reliability, and of what we deploy remain consistently high.
Security is not an add‑on for us–it’s built in from day one.
We apply Security by Design, meaning every rApp starts with a clear strategy, threat modeling, and best‑practice controls before a single line of code is written.
Our pipelines include continuous automated testing, from code scanning to vulnerability assessment and prioritization.
Every release passes through centralized Security Control, ensuring zero known vulnerabilities at the moment of deployment.
And because the same team develops and operates the rApp, we maintain a continuous feedback loop that strengthens detection, mitigation, and long-term resilience.
This approach ensures that as we scale automation and AI across networks, we do so with the highest levels of trust, protection, and operational confidence.
And this brings me to the core of how we deliver all of this at scale. Our centralized operating model is built on TRUE DevSecOps, where the same team that develops the rApp is also responsible for operating it end‑to‑end.
This creates full accountability, faster innovation cycles, and – most importantly – consistent quality and across every deployment.
With this foundation in place, let’s look at how centralized DevSecOps accelerates rApp value, reduces operational risks, and unlocks a new level of speed and reliability in real customer environments.
Figure 4 - Security strategy of DevSecOps
Conclusion
Ericsson’s Centralized DevSecOps operating model provides a standardized, secure and data-driven way to deploy, validate, monitor and evolve rApps.
This model becomes a fundamental pillar of the CSPs journey towards autonomous networks, as it enables CSPs to unleash the full value of their rApps in a fully flexible and automated fashion while preserving security and data sovereignty.
Read more