Network slicing security: secure design and protection measures
- Network slicing offers significant business opportunities for mobile network operators. It helps diverse industries to run on a shared physical infrastructure.
- Each network slice requires secure and reliable service delivery. In this research blog post, you will learn how to design your network slices securely and to safeguard them from security challenges.
Senior Specialist - Security automation in mobile networks
Senior Specialist - Security automation in mobile networks
Senior Specialist - Security automation in mobile networks
Network slicing allows mobile network operators (MNOs) to partition their physical infrastructure into different virtual networks, known as network slices. Each network slice can be dedicated to a specific vertical industry and offers well-defined Quality of Service (QoS) guarantees for connected devices. Network slicing enables flexible and fast service delivery, drives efficient use and management of network resources, and unlocks new monetization opportunities.
Meeting diverse service requirements across industries, enterprises, and consumers on one shared infrastructure requires careful assessment of the security implications. This ensures secure and reliable service delivery tailored to varying needs.
How do 5G networks guarantee secure network slice access and management?
The security by design of 5G networks is enabled through different network functions and mandatory security protocols.
An end-to-end network slice spans the 5G Radio Access Network (RAN) and the core network. The RAN performs radio resource management of network slices and the 5G core network, which uses a Service Based Architecture (SBA), has a dedicated set of network functions for network slice management.
5G SBA as depicted in figure 1, is based on cloud-native, service-driven deployment. It leverages virtual network functions that are connected through a logically uniform service bus, known as Service Based Interface (SBI), which enables everyone-to-everyone communication. The communication between the 5G network functions is supported by a uniform protocol stack composed of web-based protocols such as Hypertext Transfer Protocol (HTTP)/2, Restful Application Programming Interfaces (APIs) for service exchange, JavaScript Object Notation (JSON), Transport Layer Security (TLS) for mutual authentication, and OAuth2.0 for network service authorization.
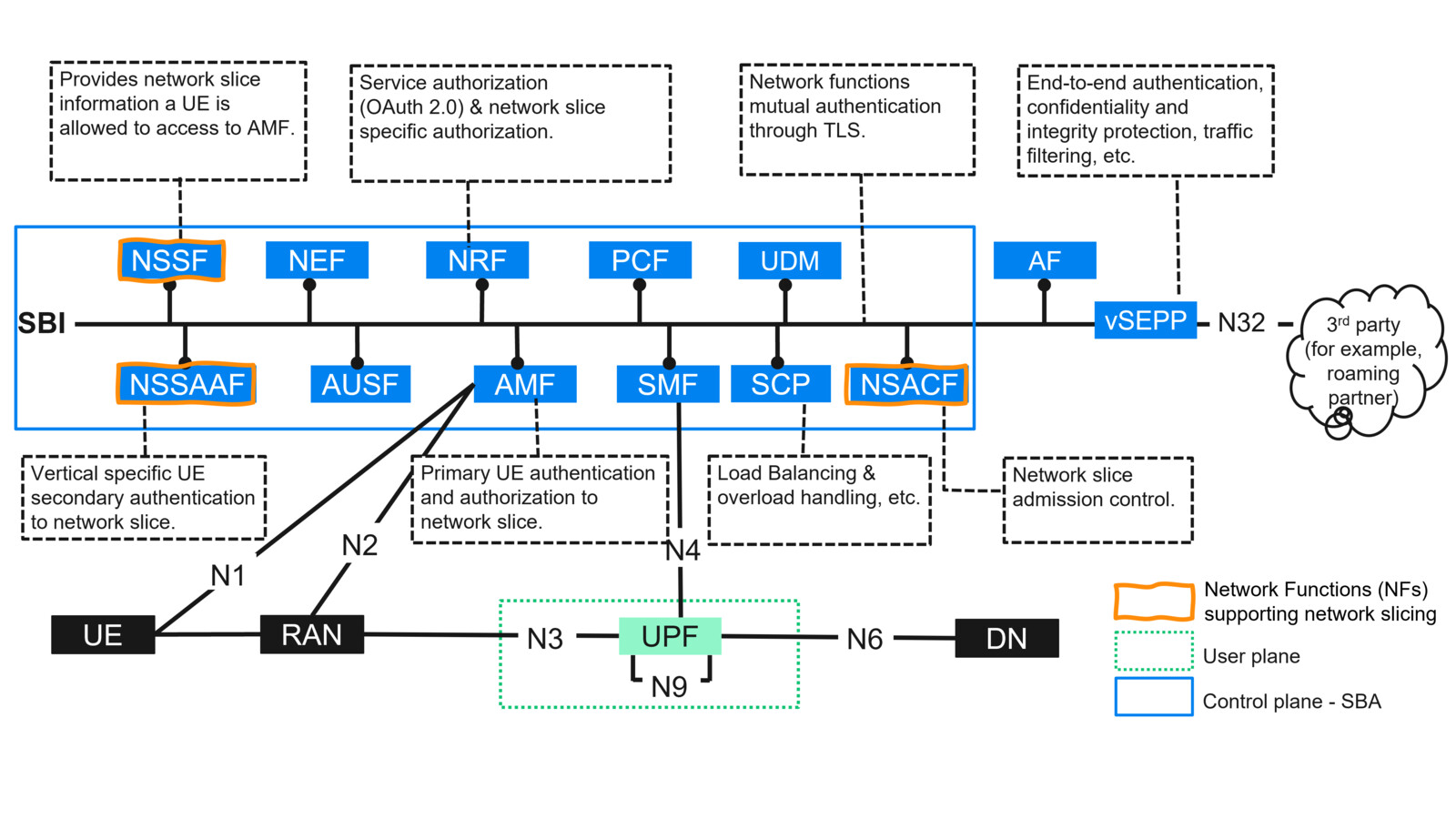
Figure 1: 5G system depicting SBA and highlighting its security features.
In a network slicing context, the use of TLS in SBA ensures mutual authentication between network functions, serving the different network slices. OAuth2.0 is an authorization protocol used by the Network Repository Function (NRF) to authorize network functions to access each other's services. This ensures that a network function serving one network slice can only access allowed and specific services from those provided by another network function serving the same network slice.
The three main 5G SBA dedicated network functions to support network slicing include:
- The Network Slice Selection Function (NSSF) facilitates the selection of a network slice to serve User Equipment (UE). It will contain details about the network slice information a UE can access, as well as the set of Access and Mobility Management Functions (AMFs) available to serve that UE.
- The Network Slice Specific Authentication and Authorization Function (NSSAAF) performs additional authentication and authorization of the UE after the primary authentication and authorization procedure is executed at the AMF. If enabled, this additional step hardens network slice security by forcing the UE to authenticate to the network slice using an authentication method selected by verticals.
- The Network Slice Admission Control Function (NSACF) monitors the number of registered UEs and established Protocol Data Unit (PDU) sessions per network slice to support efficient network slice management and operation.
The security and efficiency of 5G SBA operations are supported by the Service Communication Proxy (SCP). SCP is a network function that performs load balancing, traffic prioritization, and handles overload control, improving the security and efficiency of 5G SBA operations.
To ensure secure exchange between roaming partners, the Security Edge Protection Proxy (SEPP) provides application-layer security. It protects communication between the network functions of the respective roaming partners, and provides functionalities like traffic filtering, end-to-end authentication, confidentiality and integrity protection via signatures and HTTP/2 message encryption, topology hiding, and other functionalities.
How can MNOs address network slicing security considerations?
The security of a network slice is dependent on the security of:
- its life cycle management,
- the infrastructure it runs on, including the RAN and the core network,
- the connected devices accessing it,
- the interconnect security when the network slice spans multiple administrative domains.
Let us look into network slice attacks and countermeasures associated with each of these aspects.
1. Network slice life cycle security

The security of a network slice should be considered throughout its entire life cycle shown in figure 2 – from the design, creation, and modification of its template, which is a list of attributes that characterizes a type of network slice, to its instantiation, configuration, activation, and continuing through its runtime and eventual decommissioning.
A network slice template that is poorly designed or implemented can negatively affect the security of its related network slices as well. Compromised APIs used for network slice configuration can be exploited by attackers to interfere with slice configuration, activation, or installation.
Potential attacks on a network slice during its runtime include denial of service (DoS) attacks and data exposure.
Incorrectly handled decommissioning, carried out without proper precautions, can lead to leakage of sensitive information.
To protect networks from network slice life-cycle management attacks, security measures should be considered at each phase:
- Preparation
Verify the correctness of network slice template and use cryptographic protocols to secure the network slice during its preparation phase. - Instantiation, configuration, and activation
Secure APIs to protect a network slice from intentional misconfiguration attacks. - Runtime
Leverage network slice isolation, anomaly detection, and mitigation solutions to protect from DoS and data exposure. - Decommissioning
Ensure proper decommissioning of network slice functions and deletion of sensitive information to prevent data leakage.
Learn more about attacks and countermeasures during network slice runtime in figure 3.
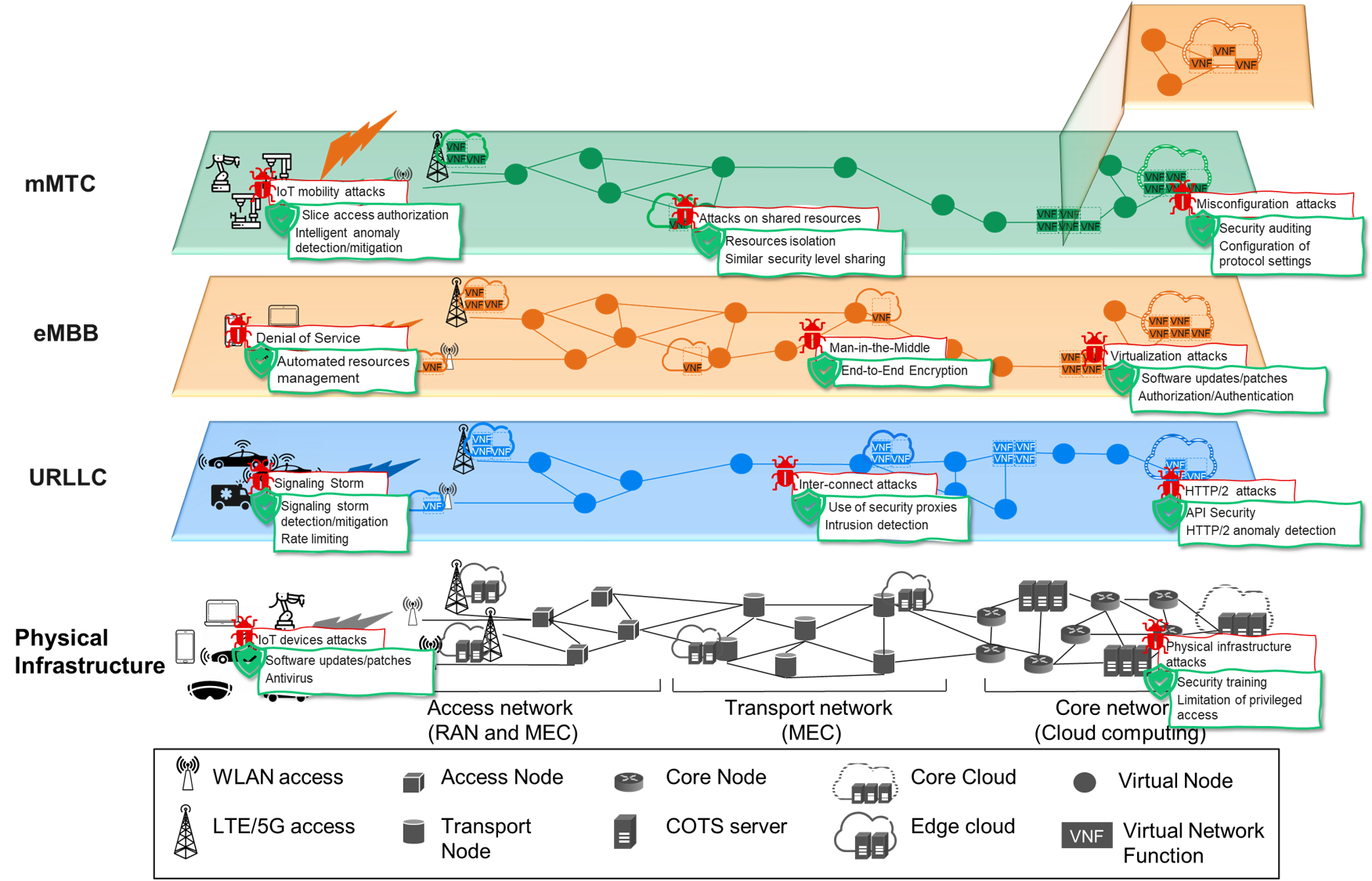
Figure 3: Summary of network slicing attacks and countermeasures.
2. Infrastructure security
Network slice security is highly dependent on its infrastructure security, see figure 4.
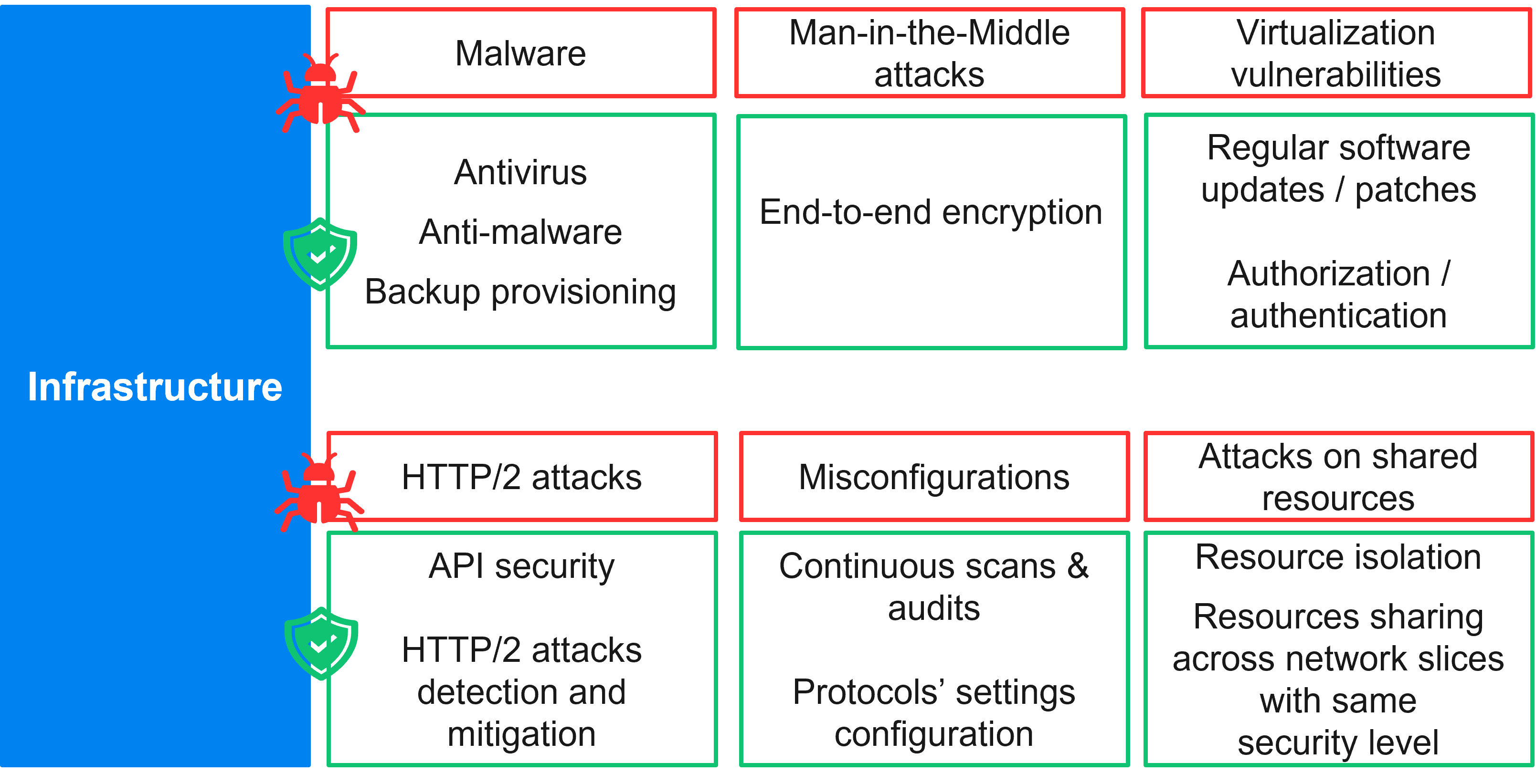
Figure 4: Summary of infrastructure attacks and countermeasures.
Many of today’s attacks are carried out through malware installed on the host machine; it can damage the system and affect all network slices served by the compromised machine. Malware, such as ransomware, can be used by attackers to steal sensitive data, including administrator and user credentials, allowing them illegal access to the system and making their detection challenging. Unauthorized access can also result from Man-in-the-Middle (MitM) attacks, especially when encryption is lacking, allowing attackers to illegally access data and compromise the confidentiality, integrity, and availability of a network slice.
Standardization, product development, network deployment and operations are four important key areas for a secure telecommunication network.
To protect against these attacks, it is critical to deploy antivirus and anti-malware software, perform regular network scans for malware detection, and maintain up-to-date backups. Limiting privileged access to the network infrastructure to only the necessary personnel is extremely important. Additionally, implementing a zero-trust security model with continuous authentication and authorization verification ensures that network access remains legitimate.
As a network slice is a virtual network, its security is closely related to the virtual resources that compose it and the applications and software it hosts. Examples of virtualization vulnerabilities are Virtual Network Functions (VNFs) escalation of privilege, and hyperjacking. Exploitation of those can impact not only the targeted VNF but also the network slices it serves as well as other co-residing VNFs and network slices serviced by those.
For instance, hyperjacking allows attackers to get privileged access to virtual machines (VMs) managed by the compromised hypervisor. These VMs may host 5G core VNFs, which can be used as an entry point to attack network slices—for example, by performing HTTP/2 attacks against VNFs servicing these targeted network slices. HTTP/2 attacks are often linked to misconfigured HTTP/2 settings on 5G VNFs or errors in the VNF descriptor used during deployment. Attacks on the RAN or core network can cause a DoS on the communicating VNF which can impact the availability of the serviced network slices.
Security risks associated with virtualization and softwarization can be mitigated through regular software updates and patches. Implementing strong authentication and authorization mechanisms such as OAuth and TLS in cloud native infrastructure to secure service usage between VNFs is critical to avoid illegal access and malicious activities such as MitM attacks. End-to-end encryption should also be accompanied by secure key management solutions such as trusted execution environment, centralized certificate management that is part of the public key infrastructure system.
While authentication and authorization in 5G SBA reduce the probability of exploitation of HTTP/2 vulnerabilities, it is important to note that awareness and correct configuration of protocol settings such as the HTTP/2 settings coupled with API security is worth the attention to prevent illegal information element and code execution. This is especially true as APIs are used for service exchange between 5G VNFs and across roaming partners. Misconfiguration attacks can be prevented through continuous scans and audits to detect missing patches, misconfigurations, and the use of default configuration/settings.
These mechanisms should complement secure deployment of network slices where strong isolation is required to prevent attacks from less secured slices, especially when slices share common resources.
5G is a critical infrastructure that needs to be continuously monitored and updated to ensure its security and resiliency.
Finally, intelligent, automated, and continuous monitoring, protection, detection, and mitigation solutions should be deployed across different parts of the network and its network slices to provide multi-layered security spanning the physical, transport, and application layers.
3. Connected devices security
Network slices provide exceptional and dedicated QoS guarantees for services accessed through various connected devices, for example Internet of Things (IoT) devices. Multi-vendor connected devices often lack built-in protection, and their security level depends on both the vendor and the user. These device vulnerabilities make them a weak target for attackers who use them as botnets to perform multiple DoS and Distributed DoS (DDoS) attacks on network slices as shown in figure 5.
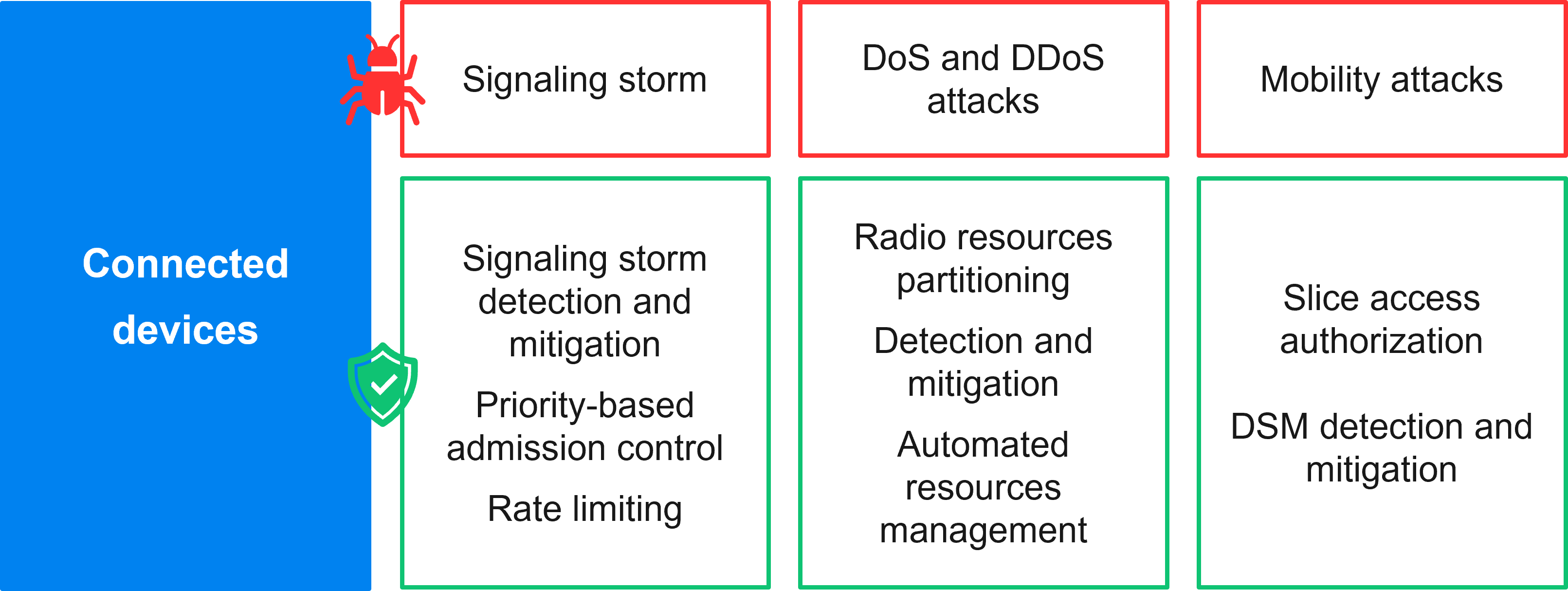
Figure 5: Summary of attacks originating from connected devices and their countermeasures.
These attacks may include signaling storm attacks. That is where malicious connected devices attempt to overload the baseband’s signaling capacity, preventing other devices from requesting more critical services provided by another network slice, maybe a mission critical services slice. A similar impact can occur with flooding attacks launched on the user plane by malicious devices over-utilizing the radio resources.
Attackers can also exploit the mobility of connected devices, excessively switching them across different network slices to cause an economical denial of sustainability through a Distributed Slice Mobility (DSM) attack.
The rise of new services across multiple industry verticals leveraging IoT devices brings to light some best practices for IoT security enforcement in enterprise networks.
Basic security measures such as deploying antivirus protection and regularly installing software updates and patches are of high importance to prevent compromise of connected devices. User awareness of the importance of securing their connected devices is a must but relying solely on that is insufficient. MNOs need to continuously monitor and protect their network against attacks by performing network configuration updates, deploying protection measures along with anomaly detection and mitigation solutions.
For example, applying strict priority based admission control can limit the impact of attacks like signaling storm attacks originating in lower priority network slices for mobile broadband on higher priority network slices supporting mission critical services. Rate limiting techniques at both the RAN and the core can also protect against signaling storm attacks. Radio resources partitioning provides efficient sharing of radio resources and their guarantees for user plane traffic in protected network slices.
Automated resources management and scaling can be adopted to contain DoS and DDoS attacks and maintain network availability. As mentioned, vertical industries can implement the optional network-slice-specific authentication and authorization procedure available in 5G to protect their network slices against DSM attack and prevent unauthorized UEs from accessing network slices, in addition to deploying intelligent DSM attack-detection solutions.
4. Interconnect security
Interconnection refers to the technical, physical, and logical connection between two or more MNOs. These MNOs can have agreements between them to ensure network slice service continuity in roaming scenarios. Since network slices can span multiple administrative domains belonging to different operators, securing their interconnection through SEPP is to be considered.
5G SBA APIs of the different 5G core VNFs are exposed to end points in the same network and through SEPP to entities in the internet protocol exchange. Without proper and up-to-date roaming documentation, specifically GSMA document IR.21, including but not limited to API versions, extensions and information elements; vulnerabilities via, for example, deprecated APIs can be exploited.
Additionally, DoS attacks from malicious or even unauthorized third parties are possible, especially when there are no restrictions on the size and frequency of resources that an API consumer can request, for example brute forcing authorization tokens. Such attacks can impact the whole network slice and potentially the roaming partner network where the targeted API producer resides.
API security is key in protecting networks when exposing their services to external entities.
This highlights the importance of API security and the need for deploying and correctly configuring SEPP to protect network slices against attacks that exploit interconnection interfaces.
To summarize, we note that attacks on network slices can impact both the RAN and the core and may escalate from one network slice to another when proper isolation is lacking.
What are the main recommendations for secure network slicing?
The table below summarizes the security recommendations for 5G network slices.
|
Intra-slice security recommendations |
Inter-slice security recommendations |
|
|
Protection against network slicing attacks starts with careful network slice design, implementation, and configuration. Considering end-to-end network slice security from RAN to the core, including both the control and user planes, is key to ensuring the security of the inner workings of a network slice, that we define as intra-slice security.
The intra-slice security also guarantees authentication, authorization, confidentiality, and integrity protection between network slice components such as VNFs. Compliance with standardization requirements and recommendations is also of high importance. For instance, accounting for primary authentication of connected devices to a network slice should be implemented while secondary authentication is highly recommended. Finally, maintaining continuous auditing and vulnerability patching is a must to secure against attacker exploitation of virtualization vulnerabilities.
Inter-slice security is critical. Failure to enforce it can lead to the escalation of an attack from one network slice to another. Strong isolation between network slices is therefore essential. It can be achieved by avoiding resource-sharing, especially when network slices require different security levels.
Since connected devices can access multiple network slices simultaneously, it is highly recommended to consider mutually exclusive access of these devices to network slices, when necessary. This is needed to prevent data leakage. Additionally, sharing of cryptographic keys between network slices should be prevented.
Finally, it is worth noting the value of automated security management through accounting for intelligent security controls. These include reactive, for example monitoring and detection, proactive like threat hunting or mitigation, and preventive, such as prediction and prevention solutions.
Learn more
To further delve into the details on proactive network security initiatives:
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.