HSM security in 5G core networks
The Ericsson Authentication Security Module offers premium security to enhance end-user privacy protection in the 5G era by integrating a Hardware Security Module (HSM) to Ericsson’s dual-mode 5G Core solution. Learn how.
About HSM security
What is HSM?
HSM (Hardware Security Module) is a dedicated systems to physically and logically secure the cryptographic keys (key generation and key storage) and cryptographic functions in the network. HSM is a purpose-built appliance that includes the hardware, software and firmware necessary for these functions in an integrated package. This is a well-known solution used in IT networks and different business segments that is now made available to mobile networks.
What is authentication and subscriber privacy in mobile network access security?
Authentication is a security process to get a cryptographic assertion that the device and the network are the entities they are claiming to be. It is a critical function on mobile networks present in all its generations. Subscriber privacy is security mechanism to protect the credentials (identities and keys) connected to subscriber authentication process.
Why a HSM-based security in 5G Core networks?
With 5G networks becoming a crucial part of many countries’ critical infrastructure, the tolerance for security risks decreases. As a result, laws and regulations aimed at controlling network access and protecting user data are becoming stricter.
The adoption of technologies such as cloud and network slicing, and a wider variety of devices and access-networks types (e.g., 3GPP, non-3GPP, WiFi, 3G, 4G and 5G) adds an infrastructure complexity and increases the variety of authentication use cases to be handled.
The current standardized solutions will be under stress in the 5G wider eco-system and networks vulnerability risks will increase.
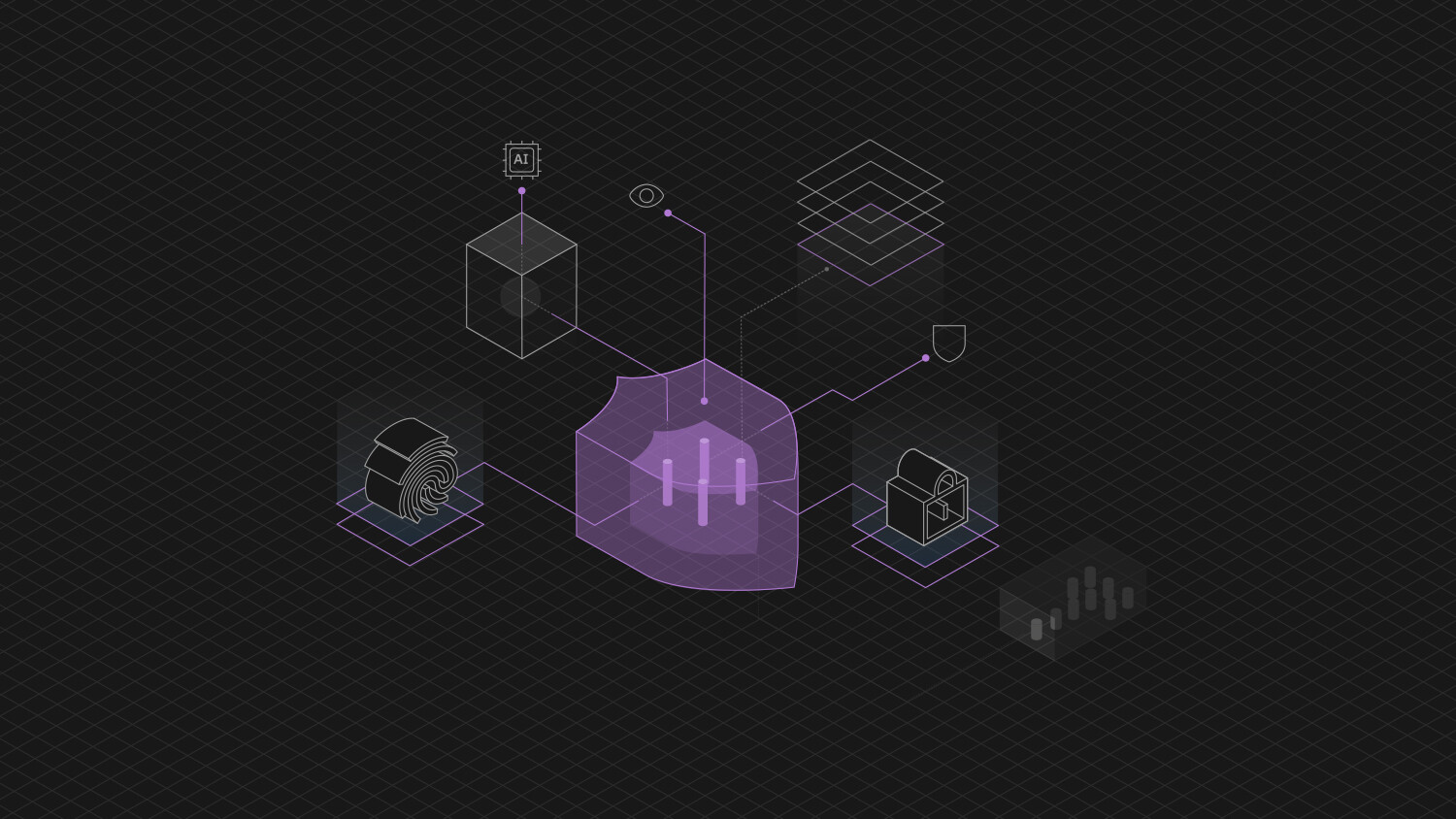
By integrating an HSM to the 5G Core Ericsson provides strong cryptographic key and algorithms protection in tamper-resistant hardware.
With the premium security offered by the Ericsson Authentication Security Module service providers will be able to better addresses the increased security demands from businesses and 5G uses cases with more strict security requirements.
Benefits with Ericsson Authentication Security Module
Hear what the industry and service providers say