How proactive anomaly detection secures 5G networks
Senior Specialist - Security automation in mobile networks
Senior Specialist - Security automation in mobile networks
Senior Specialist - Security automation in mobile networks
Non-standalone implementations of 5G rely on existing LTE Evolved Packet Core, 4G core components and signaling protocols. In our research, we explored the impact of the reliance on 4G core components and signaling protocols on the security of 5G networks. We identified several signaling denial of service attacks targeting the core network. These attacks can be launched by adversaries through exploiting vulnerabilities in IoT devices, virtualization technologies and signaling protocols.
These attacks show the need for appropriate security controls to harden the security posture of 5G networks and ensure a smooth transition from 4G to 5G.
Focus problem – signaling attacks
Many new services enabled by 5G networks are accessed through IoT devices. Some IoT devices, however, are vulnerable and can be exploited to launch attacks towards the virtualized 5G control plane. Studies have shown that the non-standalone implementation of 5G can be subject to information disclosure and denial of service attacks that exploit existing 4G signaling protocols such as the Diameter Protocol.
The reset procedure-related attack is an example of application layer attacks that can hardly be detected at the network layer. It shows the clear need for an application-layer security solution to harden the security posture of the 5G control plane. Therefore, a proactive security solution is required to foresee possible future attacks and enforce appropriate security measures to protect the network against them, even before they happen.
Proactive anomaly detection
With these requirements in mind, we propose a novel, dual-intelligence security solution for proactive anomaly detection in 5G networks. Our solution adopts a data-driven analytical approach using machine learning as a key enabler to streamline the control plane signaling with intelligent protection layers to proactively detect and defend against 5G signaling attacks.
Further down in this post, we present the details of how the reset-procedure related attack works and how our solution counters it.
Advantages
This proactive anomaly detection solution enables adaptive and automated security to be incorporated in the 5G control plane. In terms of advantages, the proposed solution:
- Enhances 5G networks security posture
- Predicts future signaling workload
- Uses the forecasted signaling workload to detect possible anomalies
- Analyzes the potential root-cause of the predicted anomalies
- Issues security recommendations to trigger adequate security measures and prevent forecasted anomalies from happening
- Secures the 5G control plane against selected signaling attacks.
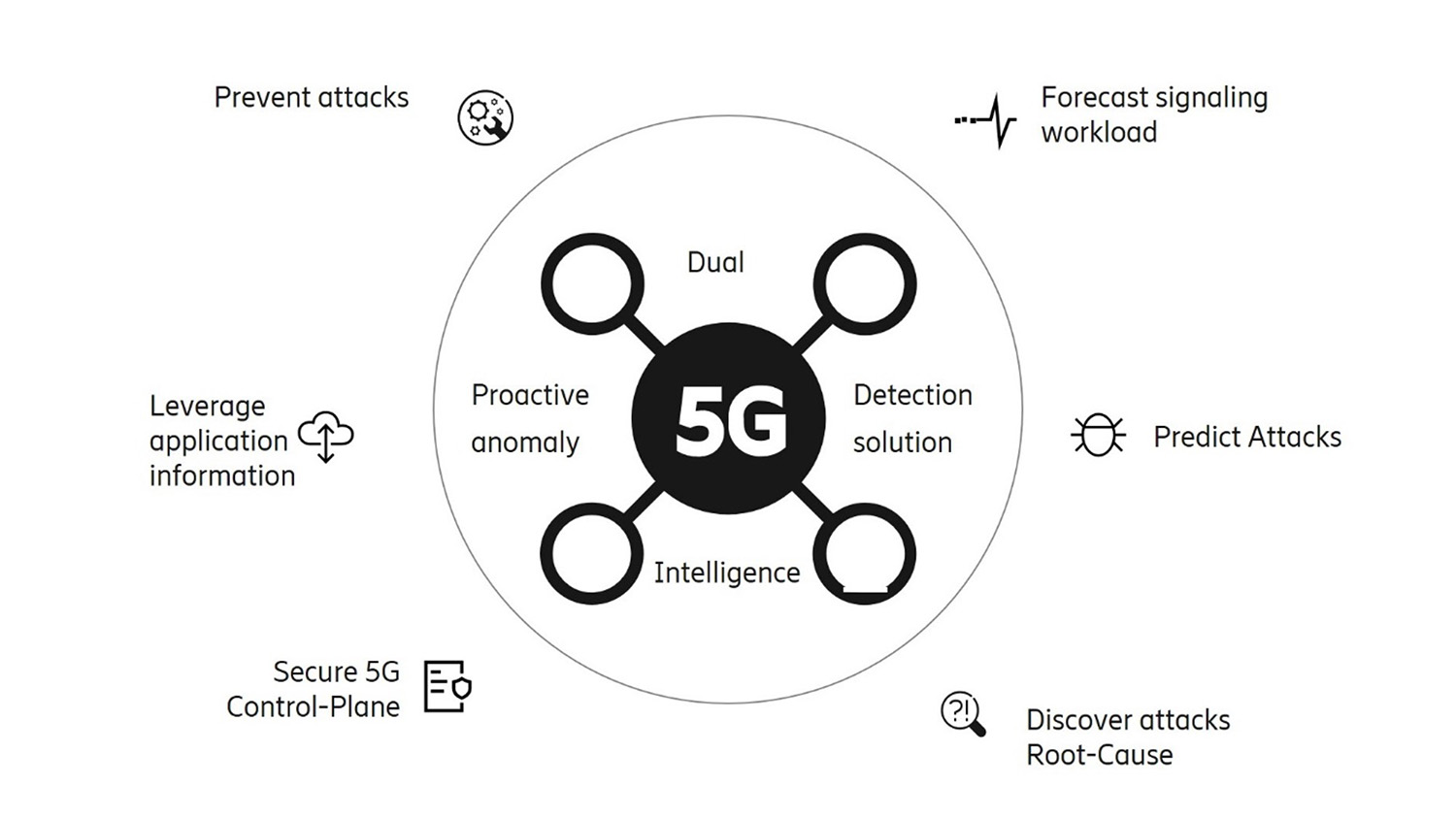
Figure 1: Advantages of our dual intelligence proactive anomaly detection solution.
Details
The reset procedure-related attack
The Diameter protocol is an application layer protocol used for authentication, authorization and accounting between control plane network functions within the same mobile network operator or between roaming partners. Mobile operators protect their mobile networks against Diameter-based attacks through deploying Diameter edge agents that filter incoming traffic. There are, however, some Diameter-based attacks that can bypass firewalling rules implemented in the Diameter edge agents.
Figure 2 presents a Diameter-based signaling attack that causes a denial of service on the Home Subscriber Server (HSS). To perform this attack, an adversary compromises a virtual network function and uses it as a rogue HSS to impersonate the HSS of a victim mobile operator. In this example, we consider that the mobile network operator’s network is virtualized and is running on top of a leased infrastructure.
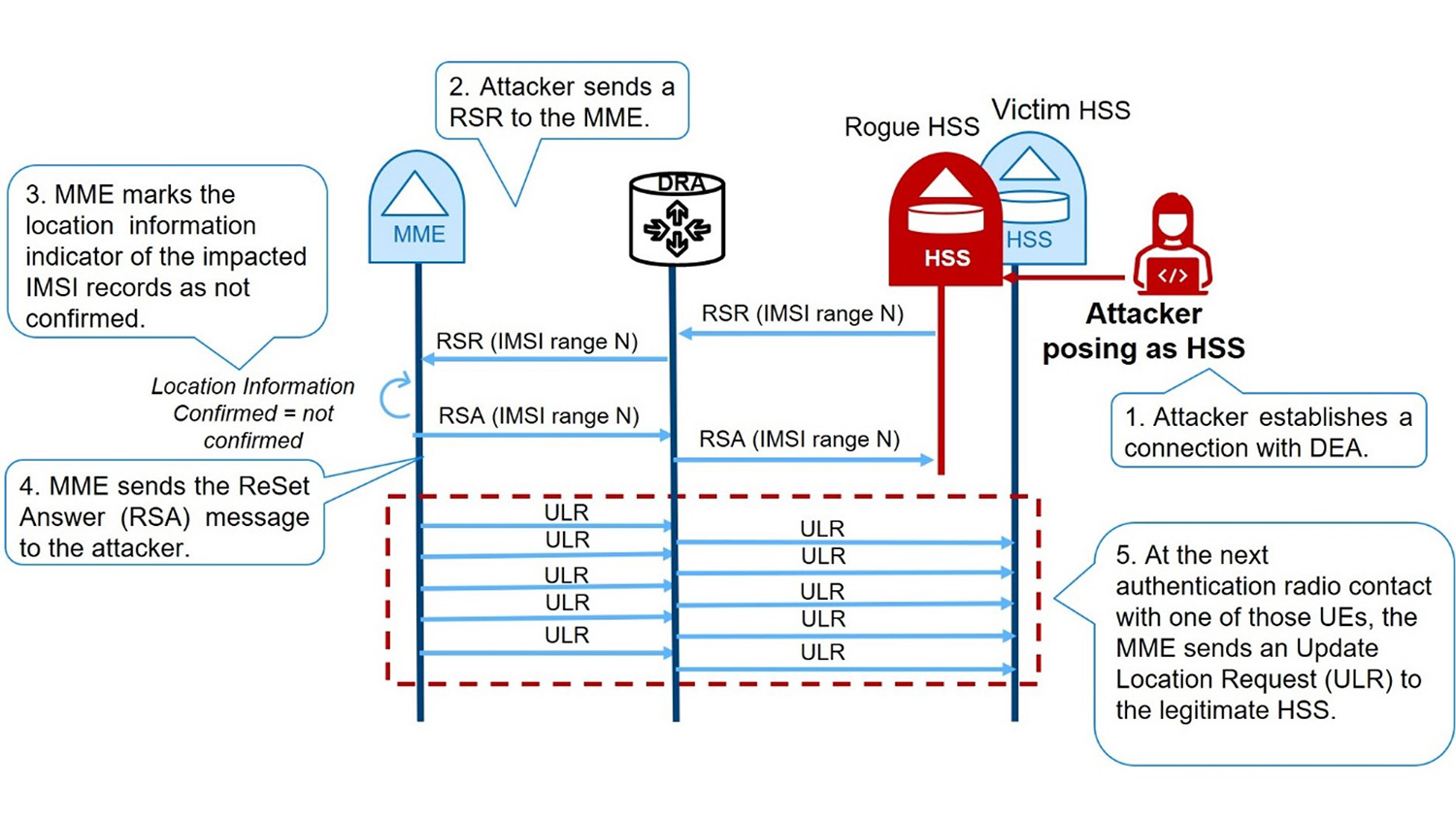
Figure 2: Reset procedure attack targeting a mobile network operator’s virtual network deployed in the cloud.
The attacker uses the rogue HSS to launch a Diameter-based attack by initiating the reset procedure. The reset procedure consists of initiating a ReSet Request (RSR) towards the Mobility Management Entity (MME) as part of the operation, and maintenance actions to prevent service disruption during its planned outage. The attacker forges an RSR message indicating to the MME the list of subscribers that will be affected by an outage.
This will trigger the MME to contact the HSS upon the connection of these subscribers to the network in order to update their locations using an Update Location Request (ULR). Given the potentially large number of ULRs sent to the legitimate HSS, the latter experiences a denial-of-service attack.
The dashed red box in figure 2 highlights this Diameter-based attack which exploits the hop-by-hop routing vulnerability of the Diameter protocol. The hop-by-hop routing forces the Diameter to answer and follow the same route as the request. Note that in Figure 2, the ReSet Answer (RSA) is received by the rogue HSS and not by the victim HSS, which is unaware that it was impersonated.
Our solution
The proposed solution depicted in Figure 3 is composed of a data collection and processing module which is responsible for application-layer information collection and processing to extract features that will be used to train deep learning models.
The collected information is time-based and is used to train a forecasting model that will predict future signaling workload (Diameter workloads, for example). Note that leveraging application-layer information is particularly useful in situations where the network functions of a tenant are deployed within the infrastructure of a third-party provider. In such a scenario, the tenant is provided with more flexibility in designing detection tools by relying on their own application-layer information.
Unlike classic real-time anomaly detection solutions that are reactive in nature, we feed the forecasted signaling workload to the anomaly detection model to proactively detect possible upcoming anomalies in the forecasted time windows. The forecasting and the anomaly detection models constituting the dual-intelligence module are based on deep learning and use signaling workload characteristics as features to offer a proactive anomaly prediction and detection.
Upon the prediction of an anomaly, an alarm can be raised to trigger the feature-based investigation module for preliminary root cause analysis to identify the attributes which are at the origin of the potential anomalies. Therefore, when integrated within a security recommendation tool, our solution not only triggers alarms upon the prediction of anomalies, but it also provides indicators, allowing for the mapping of potential anomalies to their possible origin. Thus, the feature-based investigation module provides a detailed and a richer context for the detected anomalies.
Such context can then be easily correlated with different operations and business support systems events to analyze the potential anomaly provenance. Finally, predicted anomalies and their indicators can be fed into a security recommendation tool to enforce appropriate prevention and mitigation measures.
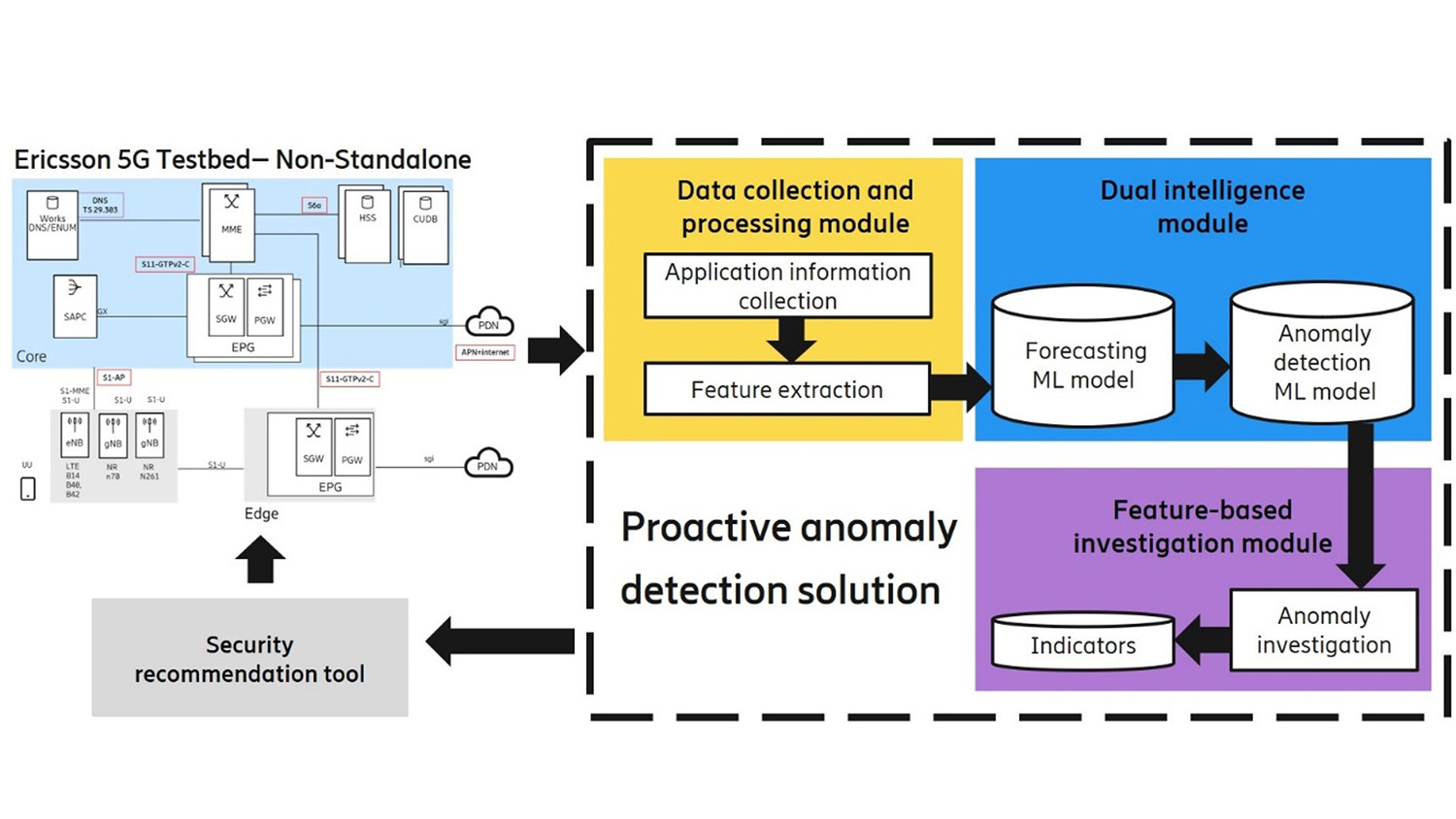
Figure 3: Proactive anomaly detection solution.
The solution described has been integrated in the artificial intelligence operations management platform offered by Ericsson.
Learn more
Read more about future network security.
Learn how to build robust anomaly detectors with machine learning.
Here’s a guide to 5G network security.
Read more about Network security standards.
Learn more about AI operations.
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.