How Ericsson’s security posture supports national security
- Wireless networks are critical infrastructure that require a holistic security approach across the lifecycle while enabling a zero-trust architecture from design through operations
- Ericsson’s security posture protects critical infrastructure today and is prepared for the evolving threat landscape
Wireless networks are critical infrastructure. Wireless networks provide communication for public safety, healthcare, manufacturing, transportation, commerce, and other use cases.
At the same time, telco networks face increasing threats from sophisticated threat actors targeting for the purpose of reconnaissance, unauthorized control, and service disruption. Nation-state actors have been attacking networks with Advanced Persistent Threats (APTs) that exploit vulnerabilities, unsecure credentials, and misconfigurations to move laterally and persist undetected in networks over long dwell times. The expanding attack surface includes APIs, AI, cloud, exponential growth in devices and applications, and open networks with new software integrated over open interfaces.
Ericsson is the world’s leading trusted telecom supplier - protecting critical infrastructure today and prepared for the evolving threat landscape. Our holistic security posture starts with our own corporate culture of security and IT defenses, adding layers of defenses that support our customers’ posture.
Security, privacy and resiliency are an ongoing concerns. The following nine areas provide a holistic overview of how Ericsson thinks about security and the processes, people and systems we have in place to protect ourselves, our customers and the end users of our networks – from research and standardization, through network development and design, deployment and operation.
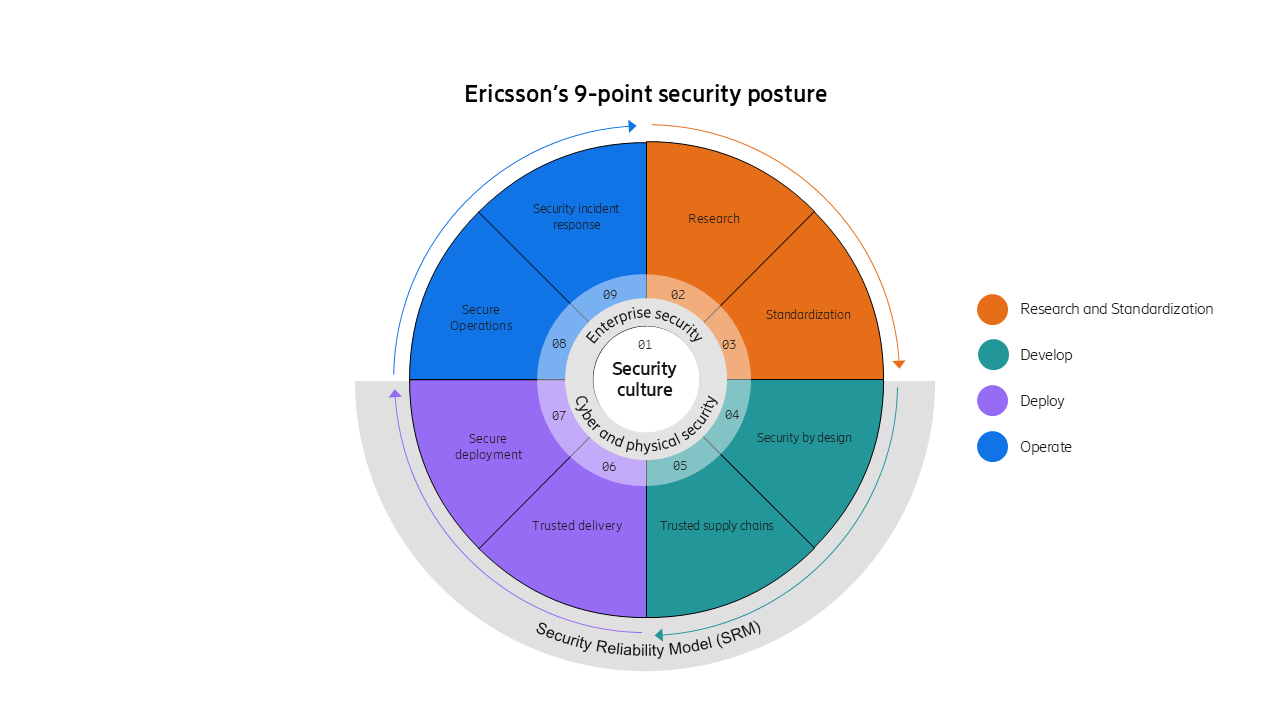
Figure 1. Ericsson’s 9-point security posture
1. Security culture supported by cyber and physical security
Our security and privacy posture starts with our security culture and frameworks with deep integration into our organization's operations, values, and strategic objectives. This includes mandatory security training globally and a specialized program with ~ 5000 Security champions and masters ensuring the protection of both our customers and Ericsson's assets. Our security and privacy posture is cemented through our security frameworks. We follow industry BCP and requirements such as NESAS, SCASes and ISO27001 with ISMS securing our Enterprise, and SRM (Security Reliability Model) securing our product and service posture.
Building upon this foundation, Ericsson’s security strategy expands outward, encompassing four seamlessly integrated phases: Research & Standardization, Development, Deployment, and Operations. Each phase forms an essential layer of Ericsson’s holistic security approach, ensuring critical assets are safeguarded at every stage of innovation, implementation, and operational maintenance.
Research & Standardization – ensuring Ericsson is prepared as threats evolve and relevant industry standards provide the highest level of security for the telecom ecosystem.
2. Research
Ericsson Research focuses on defining 6G security by driving a thorough threat analysis and a security architecture aligned with new requirements, by driving open standards, applying zero-trust principles, and taking a holistic view on security, including also implementation, deployment, and operational security aspects. Relevant technologies are AI and automation, network exposure and API security, assurance and situational awareness, and quantum-safe cryptography for resilience against future threats. Together, these domains aim to create adaptive, trusted digital infrastructures resilient to evolving threats in line with regulatory demands.
3. Standardization
Ericsson invests heavily in security standardization and community influence and is a leading contributor across regional and global standards and policy organizations including 3GPP, O-RAN ALLIANCE, IETF, ETSI, GSMA, ATIS and NIST. Our investments advance security standards globally. Ericsson is also a leader in government-industry collaboration to secure critical infrastructure including FCC CSRIC and DHS SCRM. Leadership positions include Co-Chair of the Security Working Group in O-RAN ALLIANCE, Co-Chair of ATIS Steering Group on Enhanced Zero Trust in 5G and Chair of ETSI SAGE (Security Algorithms Expert Group). Ericsson is providing leadership for standardization of Post-Quantum Cryptographic (PQC) algorithms at industry SDOs.
Develop – leading product development that ensures security is built in and customers can access differentiated capabilities that provide premium cyber protection. Hardware and software supply chains that ensure security and resilience
4. Security by design
Ericsson develops security features for operators to achieve a ZTA in their network based upon NIST SP 800-207. Ericsson adheres to secure software development using GSMA NESAS (Network Equipment Security Assurance Scheme), 3GPP SCAS (Security Assurance specifications) and Ericsson Security Reliability Model (SRM), which is guided by the NIST Secure Software Development Framework (SSDF). Ericsson follows best practices such as least privilege access, data encryption, and continuous monitoring during design and development phases and we apply DevSecOps with Continuous Integration/Continuous Deployment (CI/CD).
Ericsson is a leader in developing ZTA-enabling features and technologies including 5G SA, Open RAN, Continuous Security Monitoring and AI/ML-based security automation. We implement a unified and robust foundation for secure operations across Ericsson Silicon with hardware-based security across the radio portfolio, a capability developed in the Ericsson Austin R&D hub [5G hardware and software development center in Austin - Ericsson]. Ericsson uses robust third-party security assessments to continually challenge our networks, identify and resolve potential vulnerabilities.
5. Ericsson trusted, diversified and transparent supply chain
Ericsson maintains a secure and resilient supply chain. Our manufacturing and development processes are built on end-to-end traceability, rigorous quality controls, integrity checks, regular site audits and thorough testing. Our Business Continuity Management (BCM) framework aligns with ISO 22301 standards, ensuring the resilience of our operations and supply chain. Through the company’s USA 5G Smart Factory, Ericsson addresses a critical challenge ensuring secure, long-term manufacturing and supply chain reliability for essential RAN technology in the United States. For almost 150 years, integrity and trustworthiness have been the cornerstone of Ericsson’s supply chain strategy, and the company actively manages security risks globally while complying with regional and customer-specific regulations. Specifically, our hardware and software supply chains:
- Are GSMA NESAS compliant
- Comply with industry security standards from 3GPP and O-RAN Alliance
- Are certified under ISO/IEC 27001:2022
- Use weighted measurements from multiple data sources when vetting security in open-source software
- Ensure software supply chain security, including Software Bill of Materials (SBOM) and alignment to TIA SCS 9001
- Adopt strong product security requirements for suppliers
- Provide resilient supply chains with local manufacturing, product development and new product introduction
Deploy – these steps take our products from our own servers and factories to our customers’ networks.
6. Trusted delivery
Trusted delivery is ensured by alignment to the TIA Supply Chain Security SCS 9001, secure transport by our suppliers (C-TPAT requirements) and providing our SW via a secure download from the Ericsson Software Gateway. Software downloads include a signature which provides a trust anchor guaranteeing origin and secure transit. Systems hardening is aligned with US DHS CISA guidance.
7. Secure deployment
Deployment is secured through dedicated security competence including security champions, security masters and customer security directors. Dedicated configuration and hardening guidelines include rigorous system hardening aligned with US DHS CISA guidance to reduce attack surfaces and strengthen resilience. Our deployment practices leverage ZTA-enabling security features, public key infrastructure and centralized identity management. Ericsson deployment teams use secure network design principles and ensure traffic and network data protection through confidentiality and integrity protection with NIST-approved ciphers.
Operate – Our job does not stop once networks have been delivered. Ericsson is committed to provide our customers the tools they need to follow up US Goverment best practices and evolve to a full zero trust architecture. Our security response team is on standby 24x7x365 to respond to any incident.
8. Secure operations
Ericsson flagship security solution, Ericsson Security Manager (ESM) acts as an enabler for Zero-Trust implementation during operations, which helps our customers comply with CISA hardening guidelines. ESM enables continuous mobile security monitoring based upon NIST Cybersecurity Framework (CSF) including:
- Leading capability for false base station detection and anti-jamming
- Leading capability for threat and vulnerability intelligence
- CISA configuration auditing
- Comprehensive Attack Surface Management
- Extended Detection and Response
- Certificate and Trust Management
Ericsson uses our Ericsson Vulnerability Management System (EVMS) to monitor and track all published vulnerabilities and security updates that impact our products. Our PSIRT, product development, 3PP technology and customer support organizations then work as trusted intermediaries to all stakeholders to ensure proper notification and action.
9. Security Incident Response
Incident response is a key part of managing vulnerabilities. Ericsson Product Security Incident Response Team (PSIRT) provides immediate global response and support for any incident. We partner with our customers and law enforcement to recover from and resolve cyber threats. Ericsson partners in the Common Vulnerabilities and Exposures (CVE) Program and designated CVE Number Authority (CNA). Ericsson Threat Intelligence reports, recurring security bulletins and CVE information are resources for our customers. Ericsson is also part of GSMA CVD program supporting researchers and the wider ecosystem resolve vulnerabilities and protect customer security.
Security is central to Ericsson’s vision of enabling trusted and resilient connectivity across critical networks. From meticulous development rooted in industry-leading research and standards, to secured deployment supported by a trusted supply chain, and comprehensive tools for ongoing operation, Ericsson’s solutions address the full spectrum of cybersecurity challenges. By empowering operators with frameworks that accommodate emerging technologies such as AI and edge computing, Ericsson ensures adaptability without compromising security. These measures not only prepare CSPs and enterprises for today’s dynamic landscape but position them for secure innovation and growth under robust, scalable defenses.
Discover how Ericsson’s dedication to shaping secure networks is paving the way for a safer future in connectivity.
Read more
RELATED CONTENT
Like what you’re reading? Please sign up for email updates on your favorite topics.
Subscribe nowAt the Ericsson Blog, we provide insight to make complex ideas on technology, innovation and business simple.