The network security experience of 5G end-users is defined by the security posture of deployed networks in use, as is the case with end-users experience of network performance and coverage. This means that a comprehensive and holistic approach to network security is required to protect end-users. The guide to 5G network security aims to provide the necessary context and depth to design a holistic policy approach to network security.
The 5G guide to network security also provides an overview of how security posture of deployed networks and appropriate mitigation takes into account the four key layers: standards, products and related development processes, network deployments and network operation. Collectively these four layers define the security status of deployed networks and hence the de-facto end-user security experience. A comprehensive approach ensures that mitigating measures are implemented in such a way that interdependencies between the layers as well as specifics for a layer in question are addressed effectively.
The four layers of 5G network security
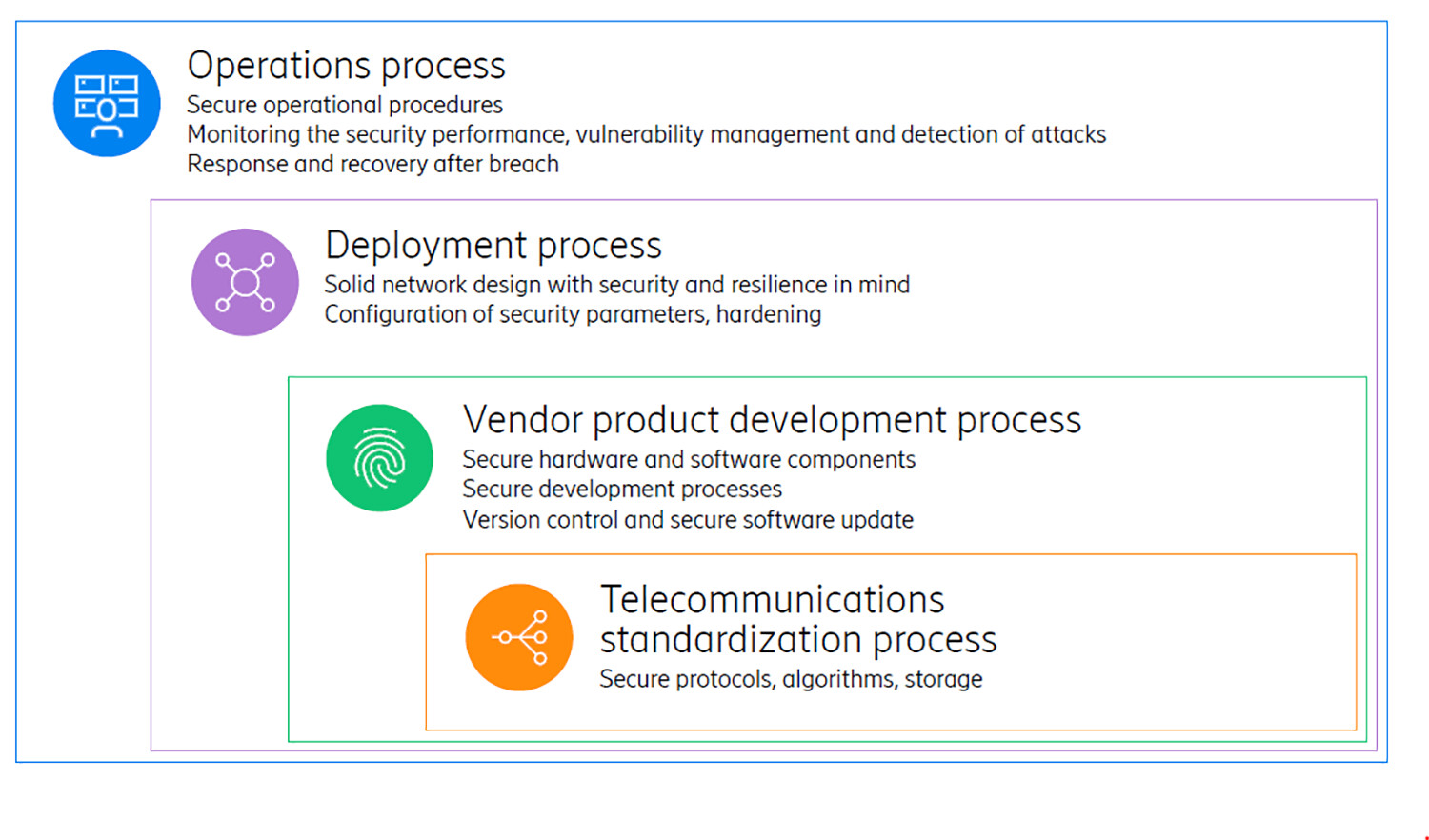
A holistic approach to secure 5G mobile network
Securing mobile networks is a key objective to realize the rewards from the advancements in mobile networks as these set the foundation and conditions for the realization of the benefits of digitalization to a society. The right security policy frameworks in place ensure the security of mobile networks. A holistic security approach provides the necessary foundation when developing policy frameworks and regulations It is an absolute prerequisite to mitigate risks.

